The Gentlemen ransomware now uses SystemBC for bot-powered attacks
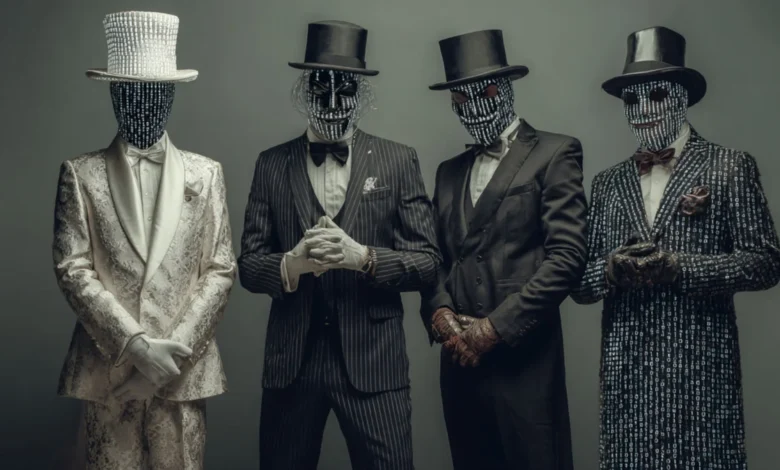
The Rise of the Gentlemen Ransomware-as-a-Service
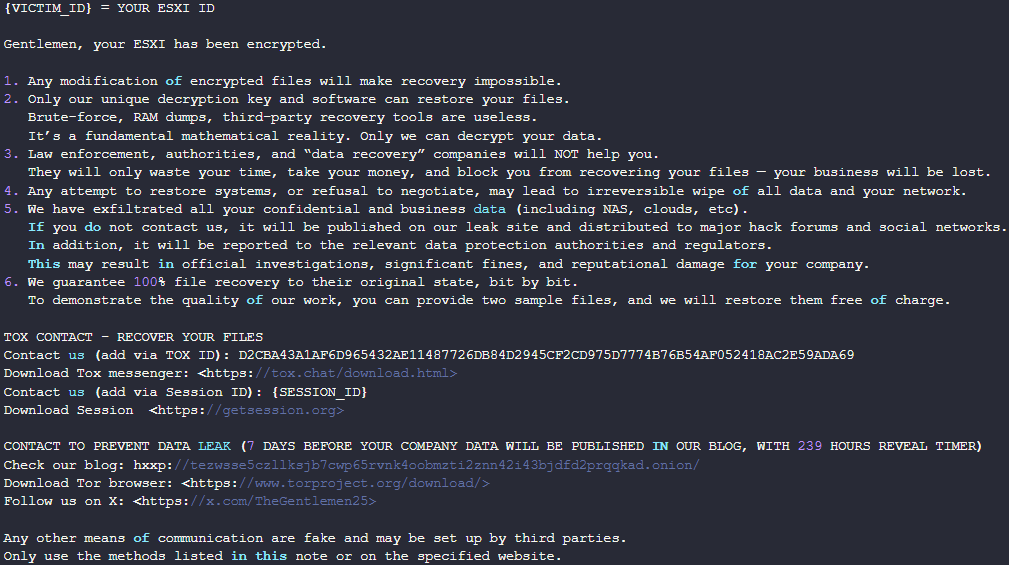
The Gentlemen RaaS operation first appeared on the threat landscape in mid-2025, quickly distinguishing itself through its cross-platform capabilities and aggressive recruitment strategies on underground forums. Unlike many nascent ransomware groups that focus on a single operating system, Gentlemen arrived with a mature toolkit. Their primary encryptor is written in the Go programming language (Golang), allowing for seamless deployment across Windows, Linux, Network Attached Storage (NAS) devices, and BSD systems. Furthermore, the group developed a specialized C-based locker specifically designed to target ESXi hypervisors, a move that aligns with the industry-wide trend of attackers prioritizing virtualization servers to maximize the impact of a single breach.
Since its inception, the Gentlemen operation has claimed responsibility for approximately 320 victims. While the group maintained a relatively low profile during its first few months, 2026 has seen a surge in activity. In December 2025, the gang gained international notoriety after compromising the Oltenia Energy Complex, one of Romania’s largest energy providers. This attack not only disrupted critical infrastructure but also served as a proof-of-concept for the gang’s ability to infiltrate high-value targets. More recently, in April 2026, The Adaptavist Group disclosed a breach that saw the Gentlemen ransomware list the organization on its dedicated data leak site, further cementing the group’s reputation as a top-tier threat actor.

The Integration of SystemBC and Botnet Infrastructure
The integration of SystemBC into the Gentlemen toolkit represents a strategic evolution. SystemBC is a long-standing proxy malware that has been active in the wild since at least 2019. It is primarily used for SOCKS5 tunneling, a technique that allows attackers to mask their communication with command-and-control (C2) servers by routing traffic through infected "zombie" computers. By using a network of proxies, threat actors can bypass geographic-based firewalls and evade detection by security software that might otherwise flag direct connections to known malicious IP addresses.
Despite a major international law enforcement effort in 2024, known as Operation Endgame, which targeted the infrastructure of several prominent malware loaders, SystemBC has proven remarkably resilient. Last year, reports indicated that the botnet was infecting up to 1,500 commercial virtual private servers (VPS) daily. The discovery of a new 1,570-host botnet linked specifically to Gentlemen ransomware affiliates suggests that the malware is being utilized not just for stealth, but as a robust delivery mechanism for human-operated intrusions.
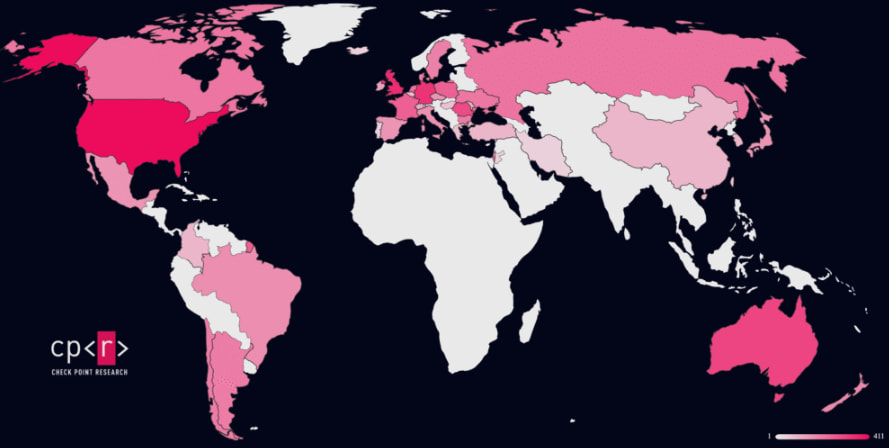
Check Point researchers observed that the infection profile of this specific botnet focuses heavily on corporate and organizational environments rather than individual consumers. This suggests a highly targeted approach designed to facilitate lateral movement within large networks. The geographic distribution of these infected hosts is concentrated in several major economies, with the United States, the United Kingdom, Germany, Australia, and Romania bearing the brunt of the infections.

Analysis of the Attack Chain and Lateral Movement
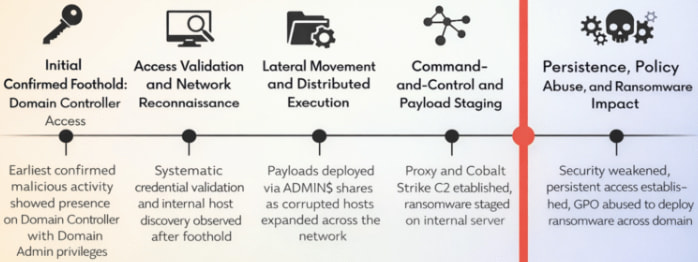
The Gentlemen ransomware affiliates employ a sophisticated multi-stage attack chain that prioritizes the total compromise of the victim’s internal infrastructure. While the exact initial access vector remains a subject of ongoing investigation—common methods include phishing, the exploitation of unpatched vulnerabilities, or the purchase of access from Initial Access Brokers (IABs)—the subsequent stages of the attack are well-documented.
Once inside a network, the threat actors focus on gaining Domain Admin privileges. In the incidents analyzed by Check Point, the attackers operated directly from a Domain Controller. From this vantage point, they conducted extensive internal reconnaissance to map the network and identify high-value assets. To maintain a persistent presence and facilitate further movement, the attackers deployed Cobalt Strike, a popular penetration testing tool frequently repurposed by cybercriminals for post-exploitation activities.
The lateral movement phase is characterized by the use of "Living off the Land" (LotL) techniques. The attackers used Mimikatz, a credential-harvesting tool, to extract plaintext passwords and NTLM hashes from memory. With these credentials, they leveraged Remote Procedure Call (RPC) and built-in administrative tools to execute commands on remote systems. The final stage of the intrusion involves staging the ransomware on an internal server and using Group Policy Objects (GPO) to trigger a near-simultaneous execution of the encryptor across all domain-joined machines. This synchronized deployment is designed to overwhelm the victim’s incident response capabilities and ensure maximum data loss before the breach can be mitigated.
Technical Specifications of the Encryption Scheme
The Gentlemen ransomware employs a sophisticated hybrid encryption scheme that balances speed with cryptographic security. The malware utilizes X25519, an elliptic curve Diffie-Hellman (ECDH) protocol, for key exchange, and XChaCha20 for the actual file encryption. For every file targeted, a random ephemeral key pair is generated, ensuring that the compromise of one key does not lead to the decryption of other files.
To increase the speed of the encryption process—thereby reducing the window for detection—the ransomware uses a partial encryption strategy for larger files. Files under 1 MB are encrypted in their entirety. However, for files exceeding this size, the malware only encrypts specific chunks of data. Depending on the file size and configuration, the encryptor may only scramble 9%, 3%, or even as little as 1% of the file’s content. While this leaves most of the data untouched, it is sufficient to render the file unreadable and unusable by standard software.
Before the encryption process begins, the malware performs several "pre-flight" checks and destructive actions:
- Process Termination: The ransomware identifies and kills processes related to databases (SQL, Oracle), backup software (Veeam, Veritas), and virtualization.
- Shadow Copy Deletion: Using the
vssadmintool, the malware deletes Volume Shadow Copies to prevent the victim from using Windows’ built-in recovery features. - Log Clearing: System and security logs are wiped to hinder forensic investigations.
- Virtual Machine Management: The ESXi-specific variant of the ransomware is programmed to shut down virtual machines (VMs) before encryption. This ensures that the virtual disks (.vmdk files) are not locked by the hypervisor and can be fully encrypted.
Broader Impact and Industry Implications
The emergence of the Gentlemen-SystemBC partnership is a troubling sign for the global cybersecurity landscape. It indicates that mid-tier ransomware operations are successfully integrating professional-grade proxy infrastructure into their workflows, a level of sophistication previously reserved for "Big Game Hunting" groups like Conti or REvil.
The focus on corporate environments in the US, UK, and Germany suggests that the Gentlemen gang is pursuing a high-revenue model, targeting organizations with the financial capacity to pay large ransoms. The targeting of energy providers, such as the Oltenia Energy Complex, also highlights the ongoing risk to critical infrastructure. Such attacks have far-reaching consequences, potentially impacting national security and public safety.
Security analysts warn that the growth of the Gentlemen RaaS is being fueled by aggressive recruitment. By offering a robust, cross-platform encryptor and a mature C2 infrastructure powered by SystemBC, the group is attracting skilled affiliates who can execute complex, human-operated attacks. This "talent influx" is likely to lead to an increase in both the frequency and the severity of Gentlemen ransomware incidents throughout the remainder of 2026.
Defensive Recommendations and Mitigation
In response to this growing threat, Check Point and other security organizations have provided Indicators of Compromise (IoCs) and signature-based detection rules, including YARA rules, to help defenders identify Gentlemen ransomware activity. However, given the group’s use of legitimate administrative tools and sophisticated proxying, a multi-layered defense-in-depth strategy is required.
Key recommendations for organizations include:
- Hardening Domain Controllers: Restricting access to Domain Controllers and monitoring for unauthorized GPO changes can prevent the mass deployment of ransomware.
- Endpoint Detection and Response (EDR): Deploying advanced EDR solutions that can detect the behavior of Cobalt Strike and Mimikatz is essential for catching lateral movement.
- Network Segmentation: Properly segmenting networks can limit the spread of ransomware from a single point of entry to the entire corporate environment.
- Vulnerability Management: Prioritizing the patching of internet-facing assets and virtualization platforms (like ESXi) is critical to closing the initial access vectors used by ransomware affiliates.
- Immutable Backups: Maintaining offline or immutable backups is the only guaranteed way to recover data without paying a ransom in the event of a successful encryption event.
As the Gentlemen ransomware gang continues to refine its tactics and expand its botnet infrastructure, the cybersecurity community must remain vigilant. The transition to bot-powered attacks signifies a new chapter for this group—one characterized by greater stealth, wider reach, and a higher potential for disruption on a global scale.
