Microsoft Warns of Rising Helpdesk Impersonation Attacks via External Teams Collaboration

The landscape of enterprise cybersecurity is facing a sophisticated shift as threat actors increasingly pivot toward social engineering tactics that exploit the inherent trust within collaboration platforms. Microsoft has issued a comprehensive warning regarding a surge in helpdesk impersonation attacks conducted through external Microsoft Teams communications. These intrusions, characterized by their reliance on legitimate administrative tools and native protocols, represent a significant challenge for modern security operations centers (SOCs) because the malicious activity often blends seamlessly into the noise of routine IT support operations. According to Microsoft’s Threat Intelligence team, these human-operated intrusions are designed to bypass traditional perimeter defenses by targeting the human element—specifically the willingness of employees to cooperate with perceived technical support staff.
The current wave of attacks leverages a multi-stage intrusion playbook that begins with the exploitation of external collaboration settings within Microsoft Teams. By taking advantage of configurations that allow external users to message employees within a different organization, threat actors are able to initiate contact under the guise of being internal IT personnel or authorized helpdesk contractors. This initial point of contact is the catalyst for a sequence of events that leads from a simple chat message to the total compromise of domain controllers and the exfiltration of sensitive corporate data.
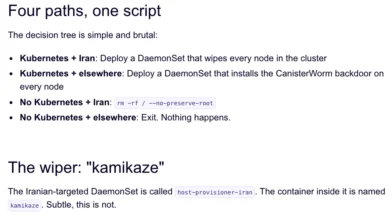
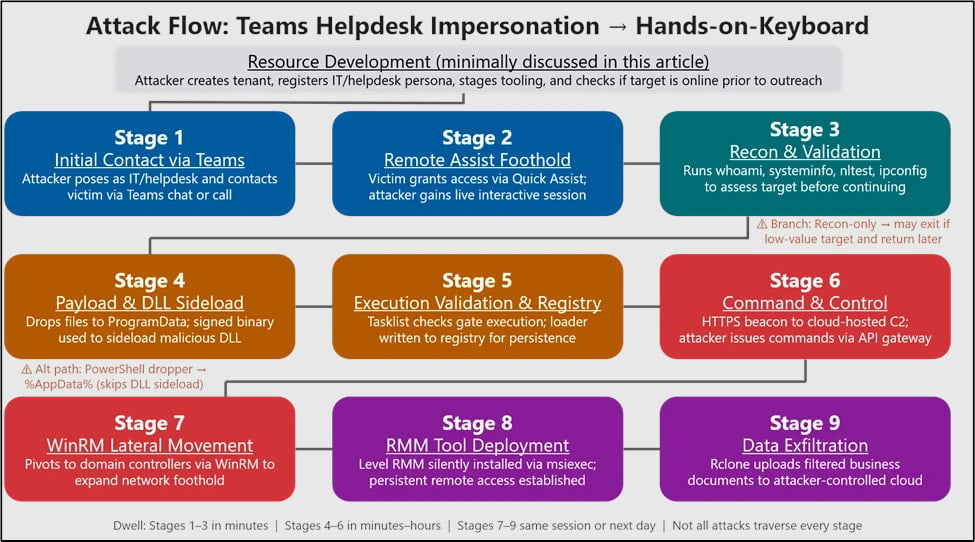
The Anatomy of the Nine-Stage Attack Chain
Microsoft has documented a consistent nine-stage attack chain that defines these helpdesk impersonation campaigns. The precision and speed of these attacks suggest a high level of operational maturity among the threat actors involved.
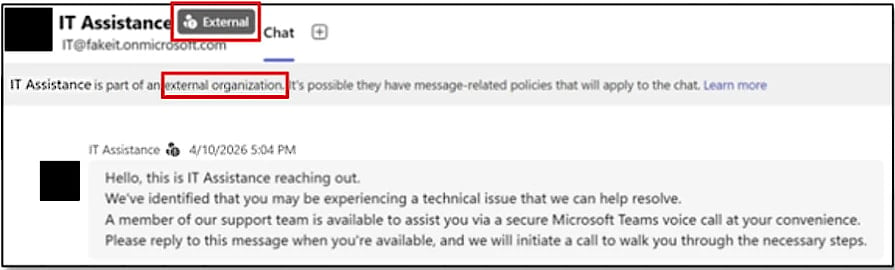
The first stage begins with the "Initial Contact." Using an external tenant, the attacker sends a message to a target employee via Microsoft Teams. The message is typically framed as an urgent security update or a necessary account verification process. Because the message appears within the familiar Teams interface, many employees fail to notice the "External" tag or the subtle indicators that the sender is not part of their organization. The attacker’s goal in this phase is strictly psychological: establishing authority and creating a sense of urgency.

In the second stage, the attacker moves to "Remote Access Acquisition." Once the target is engaged, the attacker requests that the employee initiate a remote support session. To avoid raising red flags with third-party software, they frequently direct the user to "Quick Assist," a legitimate, built-in Windows feature designed for remote troubleshooting. By using a native Windows tool, the attacker bypasses many security software alerts that might otherwise block the installation of unauthorized remote access Trojans (RATs).
Once the remote session is established, the third stage, "System Reconnaissance," begins. With direct control over the employee’s machine, the attacker uses standard administrative interfaces such as Command Prompt and PowerShell. They execute a series of discovery commands to determine the user’s privilege level, identify domain membership, and map the local network. This phase is critical for the attacker to assess the value of the compromised workstation as a jumping-off point for further movement.
The fourth stage involves "Payload Delivery and Execution." To maintain a foothold that persists beyond the remote session, the attacker drops a small payload bundle into user-writable directories, such as the ProgramData folder. To evade detection, they utilize a technique known as DLL side-loading. This involves placing a malicious Dynamic Link Library (DLL) in the same directory as a legitimate, digitally signed application—such as those from Adobe, Autodesk, or even Windows native processes. When the legitimate application is launched, it inadvertently loads the malicious DLL, allowing the threat actor’s code to run under the umbrella of a trusted process.
In the fifth stage, the attacker establishes "Command-and-Control (C2) Communication." The malicious code initiates an HTTPS-based connection to an external server. By using standard web ports and encrypted traffic, the C2 communication is designed to mimic normal outbound web browsing, making it nearly impossible for traditional firewalls or basic network monitoring tools to flag it as anomalous.
The sixth stage is "Persistence." The attacker modifies the Windows Registry or creates scheduled tasks to ensure that their malicious components remain active even if the system is rebooted. This ensures that the initial effort spent on social engineering provides long-term access to the network.

In the seventh stage, the attack shifts toward "Lateral Movement." Having secured a foothold, the threat actor abuses Windows Remote Management (WinRM) to move across the network. WinRM is a standard protocol used by IT administrators for remote configuration, meaning its use rarely triggers security alerts in a typical enterprise environment. The attacker targets other domain-joined systems, searching for accounts with higher privileges.
The eighth stage focuses on "Targeting High-Value Assets." The ultimate goal of the lateral movement is often the Domain Controller (DC) or servers containing sensitive intellectual property and financial data. By compromising a DC, the attacker can gain full control over the organization’s identity infrastructure, allowing them to create new accounts or reset passwords at will.
The final and ninth stage is "Data Exfiltration." Using specialized utilities like Rclone—a legitimate command-line program used to manage files on cloud storage—the attackers bundle and transfer sensitive data to external cloud storage providers. Microsoft notes that this exfiltration is often highly targeted; attackers use filters to identify specific file types or keywords, ensuring they only steal the most valuable information while minimizing the network traffic footprint to avoid detection.
The Strategy of Living off the Land
One of the most concerning aspects of this trend is the heavy reliance on "Living off the Land" (LotL) techniques. By using legitimate administrative tools like Quick Assist, WinRM, PowerShell, and Rclone, threat actors effectively "hide in plain sight." Traditional antivirus solutions are often tuned to look for known malicious file signatures. However, when an attacker uses a built-in Windows tool for a malicious purpose, there is no "malware" for the antivirus to catch.
This approach exploits the visibility gap in many organizations. Security teams often struggle to distinguish between a legitimate IT administrator using WinRM to fix a server and a threat actor using the same protocol to steal a database. Microsoft emphasizes that the use of signed, trusted applications for DLL side-loading further complicates the defense, as it leverages the trust relationship between the operating system and established software vendors.
Historical Context and Evolution of Teams-Based Attacks
The abuse of Microsoft Teams is not a entirely new phenomenon, but the tactics have evolved significantly. In previous years, researchers identified vulnerabilities such as "GIFShell," which allowed attackers to use GIFs to exfiltrate data through Teams. Other campaigns, such as those attributed to the threat group Storm-0324, have used Teams to distribute malicious attachments.
However, the current shift toward helpdesk impersonation highlights a move toward "human-operated" intrusions. Rather than relying on automated botnets or mass phishing emails, these attackers are active participants in the intrusion. They respond to user queries in real-time, adapt their social engineering scripts based on the target’s reactions, and manually navigate the network once access is gained. This hands-on approach significantly increases the success rate of the breach.
Technical Data and Observed Trends
Microsoft’s telemetry suggests that these attacks are not limited to a single industry but are instead targeting organizations with large, distributed workforces where employees are accustomed to receiving remote support. The data indicates a preference for exploiting the "External Access" feature in Teams, which is often enabled by default in many Microsoft 365 tenants to facilitate business-to-business collaboration.
Furthermore, the use of Rclone for exfiltration has become a hallmark of modern ransomware and data extortion groups. By syncing stolen data directly to cloud services like Mega, Dropbox, or private S3 buckets, attackers can bypass traditional Data Loss Prevention (DLP) systems that are primarily configured to monitor for bulk transfers to unknown or un-categorized IP addresses.
Official Responses and Defensive Recommendations
Microsoft has integrated several security features into Teams to combat these threats, including explicit warning banners when a user receives a message from an external contact. These banners warn that the sender is from outside the organization and provide a one-click option to block or report the user.
In their recent advisory, Microsoft urges IT administrators to take a proactive stance:
- Restrict External Access: Organizations should evaluate whether they truly need open federation in Teams. Microsoft recommends limiting external communications to specific, trusted domains or disabling it entirely for users who do not require it.
- Harden Remote Assistance Tools: If Quick Assist is not required for business operations, it can be disabled via administrative templates. If it is required, its use should be strictly monitored through endpoint detection and response (EDR) tools.
- Monitor WinRM and PowerShell: Security teams should implement logging for PowerShell and WinRM. Any lateral movement using these protocols from a standard workstation to a sensitive server should be treated as a high-priority alert.
- User Education: Employees must be trained to recognize that IT support will rarely, if ever, initiate contact through an external Teams chat. Standard operating procedures for requesting support should be clearly communicated and reinforced.
Broader Implications for Enterprise Security
The rise of helpdesk impersonation via Teams is a symptom of a broader trend in the cybersecurity industry: the commoditization of identity-based attacks. As software vulnerabilities become harder to find and more expensive to exploit, threat actors are returning to the most reliable vulnerability of all—human psychology.
This shift necessitates a "Zero Trust" approach not just for network architecture, but for internal communications. The assumption that a message appearing within a corporate application is inherently safe is a dangerous one. As organizations continue to rely on unified communication platforms to bridge the gap between remote and office-based work, these platforms will remain a primary battleground for cyber defenders.
The implications for incident response are also profound. When an intrusion is carried out using legitimate tools, the forensic trail is much harder to follow. Investigators must look for "behavioral IOAs" (Indicators of Attack) rather than "static IOCs" (Indicators of Compromise). This requires a more sophisticated level of telemetry and a deep understanding of what constitutes "normal" behavior within a specific corporate environment.
Microsoft’s warning serves as a critical reminder that as defensive technologies improve, attackers will continue to find the path of least resistance. In the era of digital transformation, that path often leads directly through the helpdesk chat window. Ensuring that both technical controls and human awareness are synchronized is the only viable path forward in mitigating this growing threat.