Starkiller Phishing-as-a-Service Uses Real-Time Relays and Headless Browsers to Neutralize Multi-Factor Authentication
The landscape of cyber-enabled fraud is undergoing a sophisticated transformation as traditional, static phishing methods give way to dynamic, real-time interception platforms. At the forefront of this evolution is a newly identified phishing-as-a-service (PhaaS) offering known as Starkiller. Unlike conventional phishing kits that rely on static, easily detectable clones of login pages, Starkiller employs a sophisticated relay mechanism that acts as a bridge between the victim and the legitimate service. By utilizing headless browser technology and containerized infrastructure, the service allows even low-skill threat actors to bypass robust security measures, including multi-factor authentication (MFA), by intercepting session tokens and credentials in real time.
The Technical Architecture of Starkiller
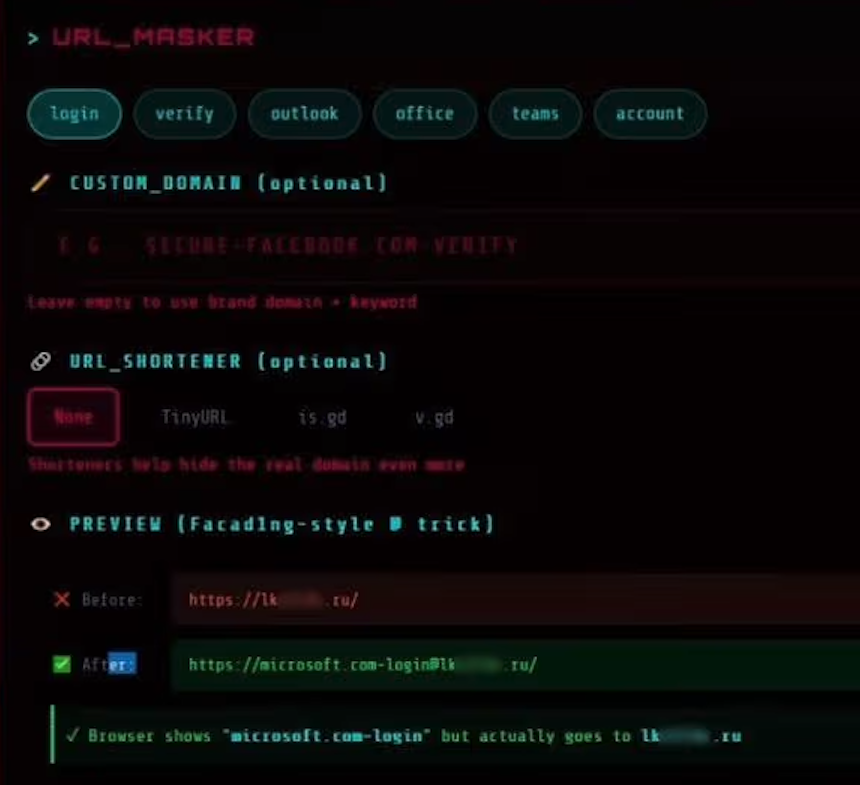
The core innovation of Starkiller lies in its departure from the "template-based" phishing model. In a traditional attack, a fraudster hosts a copy of a website like Microsoft 365 or Gmail. Security filters often flag these pages because the underlying code remains static and deviates from the original source. Starkiller sidesteps this by not hosting a copy at all. Instead, it utilizes a headless Chrome browser—a web browser without a graphical user interface—running within a Docker container.
When a victim clicks a malicious link generated by the Starkiller platform, the service triggers a dedicated instance of this headless browser to navigate to the actual, legitimate login page of the targeted brand, such as Apple, Google, or Facebook. The platform then mirrors the live site’s content to the victim’s browser. This process creates a "Man-in-the-Middle" (MitM) or "Adversary-in-the-Middle" (AitM) scenario. Because the victim is technically interacting with the real website through the attacker’s proxy, the visual cues, such as loading animations and security prompts, are indistinguishable from a legitimate session.
As the victim enters their username and password, the data is captured by the Starkiller infrastructure before being forwarded to the legitimate site. If the legitimate site requests an MFA code—whether via SMS, an authenticator app, or a push notification—the Starkiller relay passes that request to the victim. Once the victim enters the code, it is captured, logged, and forwarded to the real service to complete the authentication. The attacker then harvests the resulting session cookies and tokens, which grant them full, authenticated access to the account without needing to know the victim’s password or bypass MFA a second time.
Sophisticated URL Masking and Delivery
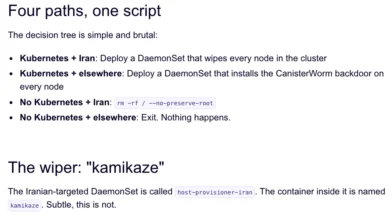
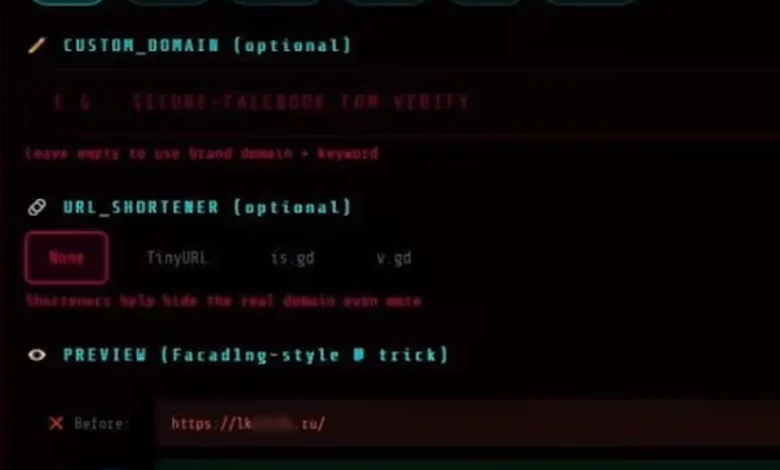
To ensure high click-through rates and evade initial scrutiny by email gateways, Starkiller employs a variety of deceptive URL-masking techniques. One of the primary methods identified by researchers at Abnormal AI is the use of the "at" (@) symbol in the URI structure. In standard web protocols, the information preceding the "@" symbol in a URL is treated as user-info data, while the actual destination is determined by the string following the symbol.
For example, a malicious link might appear as "[email protected]." To an untrained eye or a mobile browser that truncates long strings, the URL appears to originate from Microsoft. However, the browser ignores the "login.microsoft.com" portion and directs the user to the malicious infrastructure hosted on the ".ru" domain. Furthermore, the Starkiller platform integrates with various URL-shortening services, allowing attackers to further obfuscate the final destination and bypass blocklists that target known malicious domains.
The Jinkusu Ecosystem and PhaaS Business Model
Starkiller is not an isolated tool but a flagship product within a broader suite of cybercrime services managed by a threat group known as Jinkusu. This group operates with the professional veneer of a legitimate software-as-a-service (SaaS) provider. They maintain active user forums where "subscribers" can troubleshoot deployments, request new features, and share successful social engineering templates.
The platform’s administrative dashboard provides attackers with real-time analytics that would be familiar to any digital marketer. It tracks visit counts, conversion rates, and geographic data of the victims. Operators can set up automated alerts via Telegram, ensuring they are notified the instant a new set of credentials or a session token is harvested. This level of automation allows a single attacker to manage dozens of simultaneous campaigns with minimal manual intervention.
Beyond Starkiller, the Jinkusu group offers modular add-ons, including a tool designed to scrape contact lists and email histories from compromised accounts. This data is then fed back into the system to create highly targeted "follow-on" phishing lists, turning a single successful breach into a self-sustaining cycle of further compromises within an organization’s network.
The Evolution of Phishing: A Brief Chronology
To understand the threat posed by Starkiller, it is necessary to view it within the context of the historical evolution of phishing:
- The Early Era (2000s): Phishing consisted primarily of "spray and pray" email campaigns using poorly crafted replicas of banking websites. Detection was relatively simple, based on static signatures and domain age.
- The Template Era (2010s): Phishing kits became commoditized, allowing attackers to deploy high-quality clones of hundreds of different brands. Security responded with reputation-based filtering and the widespread adoption of MFA.
- The AitM Revolution (2020–Present): Tools like Evilginx and Muraena introduced the concept of transparent proxies to bypass MFA. Starkiller represents the next step in this evolution by moving the infrastructure to a scalable, containerized SaaS model that uses headless browsers to ensure 100% fidelity with the target site.
This progression shows a clear trend: as defensive technologies improve, offensive tools move closer to the "source," eventually reaching the point where the attacker is no longer mimicking the service but simply acting as a transparent, malicious layer on top of it.
Supporting Data and the Cost of Credential Theft
The rise of platforms like Starkiller is reflected in global cybersecurity trends. According to the 2024 Anti-Phishing Working Group (APWG) reports, the number of unique phishing sites detected has reached record highs, with a significant shift toward targeting enterprise social media and cloud identity providers.
Data from the FBI’s Internet Crime Complaint Center (IC3) suggests that business email compromise (BEC), which is frequently initiated through credential theft, accounts for billions of dollars in annual losses. The ability of tools like Starkiller to bypass MFA is particularly concerning given that many organizations rely on MFA as their primary—and sometimes only—defense against unauthorized access. A 2023 study by security firms indicated that while MFA reduces the risk of automated bot attacks by over 90%, its effectiveness against targeted AitM attacks is significantly lower, as these tools are specifically designed to subvert the logic of secondary authentication.
Industry Reactions and Defensive Implications
Security researchers have expressed significant concern regarding the democratization of such advanced capabilities. Callie Baron and Piotr Wojtyla of Abnormal AI noted in their analysis that Starkiller represents a "significant escalation" because it provides low-skill actors with capabilities that were previously the domain of sophisticated state-sponsored groups or highly technical independent hackers.
The consensus among cybersecurity professionals is that traditional defenses, such as static blocklisting and basic MFA, are no longer sufficient. Organizations are being urged to move toward "phishing-resistant" authentication methods. These include FIDO2-compliant hardware security keys (like YubiKeys) and Passkeys, which use cryptographic binding between the device and the specific domain. Unlike SMS codes or TOTP (Time-based One-Time Password) tokens, a FIDO2 key will not provide an authentication credential to a proxy site because the domain name does not match the legitimate service’s registered origin.
Furthermore, security operations centers (SOCs) are being advised to implement behavioral analytics that can detect the subtle anomalies associated with proxy traffic. This includes monitoring for "impossible travel" (a user logging in from two distant geographic locations simultaneously) and identifying the use of headless browsers or known data center IP ranges for user authentication sessions.
Broader Impact and Analysis
The emergence of Starkiller signals a new chapter in the "arms race" between cybercriminals and defenders. By treating phishing as a high-performance SaaS product, the Jinkusu group has reduced the operational overhead of cybercrime to near zero. This commodification means that the volume of sophisticated attacks will likely increase, as the technical barriers to entry have been effectively removed.
From a strategic perspective, Starkiller highlights a critical vulnerability in the modern web: the reliance on session cookies. Even with the strongest passwords and MFA, the "session" remains a point of failure. If an attacker can steal the token that says "this user is already logged in," the most robust front-door security becomes irrelevant.
As we move forward, the success of Starkiller will likely inspire clones and competitors, leading to a crowded market of MFA-bypass tools. For businesses and individuals, the takeaway is clear: the visual appearance of a website and the presence of an MFA prompt are no longer guarantees of safety. Vigilance must shift toward verifying the integrity of the URL and adopting hardware-based security standards that are immune to the "Man-in-the-Middle" tactics perfected by platforms like Starkiller.