Microsoft Defender Zero-Day Exploits Rise as Threat Actors Weaponize BlueHammer RedSun and UnDefend Flaws

The cybersecurity landscape has been jolted by a series of critical alerts from Huntress, a leading managed security platform, warning that threat actors have begun actively exploiting a trio of recently disclosed vulnerabilities within Microsoft Defender. These security flaws, which were initially released as zero-days by a disgruntled independent researcher, are being utilized by attackers to escalate privileges and disable essential security updates on compromised Windows environments. The situation highlights a growing friction between the security research community and major software vendors, as well as the immediate danger posed when proof-of-concept (PoC) code is released publicly before patches are available for all identified risks.
The vulnerabilities in question—codenamed BlueHammer, RedSun, and UnDefend—represent a significant threat to endpoint security across the globe. Microsoft Defender, which is built into hundreds of millions of Windows installations, serves as the primary line of defense for both individual consumers and large-scale enterprises. The exploitation of these flaws allows attackers who have already gained a foothold in a system to bypass standard security restrictions, effectively granting them the "keys to the kingdom" or the ability to blind the antivirus software to subsequent malicious activities.
Technical Breakdown of the Exploits
The three vulnerabilities target different aspects of the Microsoft Defender ecosystem, providing a versatile toolkit for attackers seeking to entrench themselves within a target network.
BlueHammer (CVE-2026-33825)
BlueHammer is a Local Privilege Escalation (LPE) vulnerability. In a typical attack scenario, a threat actor gains access to a system through a low-privileged account—perhaps via a phishing link or an unpatched browser exploit. Under normal circumstances, this account would be restricted from accessing sensitive system files or making global changes. BlueHammer allows the attacker to exploit a flaw in how Defender handles internal processes, elevating their permissions to the SYSTEM level. This level of access is the highest possible on a Windows machine, allowing the attacker to install kernel-level malware, steal credentials, and move laterally across a network.
RedSun
Similar to BlueHammer, RedSun is an LPE vulnerability that targets the endpoint protection engine. While Microsoft has moved to address BlueHammer, RedSun remains a potent threat as it relies on a different mechanism of action within the Defender service. As of the latest reports, this vulnerability remains unpatched in several versions of the Windows operating system, leaving a window of opportunity for sophisticated actors to maintain persistence even if other vulnerabilities are mitigated.
UnDefend
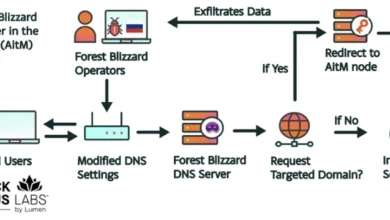
The third flaw, UnDefend, is categorized as a Denial-of-Service (DoS) vulnerability, but its implications are more insidious than a simple system crash. UnDefend can be triggered to effectively block Microsoft Defender from receiving definition updates. In the fast-moving world of cybersecurity, antivirus software is only as good as its last update. By preventing the system from downloading new threat signatures, an attacker can ensure that their custom-built malware remains undetected by Defender’s scanning engine. This creates a "blind spot" that allows for long-term espionage or data exfiltration without triggering traditional alarms.
The Origins of the Zero-Days: The "Chaotic Eclipse" Controversy
The public release of these exploits is rooted in a dispute over the vulnerability disclosure process. The flaws were published by a researcher operating under the pseudonym "Chaotic Eclipse" (also known as Nightmare-Eclipse). According to the researcher, the decision to release the details and PoC code on GitHub was a direct response to Microsoft’s perceived mishandling of the initial reports.
In the cybersecurity industry, "Coordinated Vulnerability Disclosure" (CVD) is the standard practice. It involves researchers privately informing vendors of flaws and allowing them a set period (usually 90 days) to develop and release a patch before the information is made public. Chaotic Eclipse alleged that the communication with Microsoft was insufficient or that the severity of the flaws was being downplayed, leading to a "full disclosure" event.
This move has reignited the debate over the ethics of zero-day releases. While full disclosure forces vendors to act quickly, it also provides a ready-made blueprint for cybercriminals. In this instance, the time between the public posting of the exploits and their observation in the wild was remarkably short, demonstrating how quickly threat actors monitor platforms like GitHub for new weaponizable code.

Chronology of the Exploitation and Response
The timeline of events suggests a rapid escalation from disclosure to active threat:
- Early April 2026: Chaotic Eclipse publishes the details and PoC for BlueHammer, RedSun, and UnDefend on GitHub, citing frustration with the disclosure process.
- April 10, 2026: Huntress observes the first signs of BlueHammer being weaponized in real-world attacks. These attacks targeted organizations with standard Windows configurations where Defender was the primary security tool.
- April 14, 2026: Microsoft releases its monthly "Patch Tuesday" updates, which include a fix for BlueHammer, now officially tracked as CVE-2026-33825.
- April 16, 2026: Despite the patch for BlueHammer, Huntress reports that threat actors have begun integrating RedSun and UnDefend into their toolkits. The firm observes "hands-on-keyboard" activity, indicating that human attackers are actively navigating compromised systems.
- April 17, 2026: Huntress issues a formal warning to the security community, detailing the specific commands used by attackers and urging immediate patching and monitoring.
Anatomy of an Attack: Hands-on-Keyboard Activity
The data provided by Huntress offers a chilling look at how these vulnerabilities are used in the middle stages of a cyberattack. Security analysts observed attackers running a series of enumeration commands immediately following the successful exploitation of the Defender flaws. These included:
whoami /priv: Used to verify the newly acquired elevated privileges.cmdkey /list: Executed to find stored credentials or passwords that could be used to access other systems on the network.net group: Used to map out the organizational structure and identify high-value targets like Domain Administrators.
The transition from automated exploit scripts to manual command-line interaction—often called "hands-on-keyboard" activity—is a hallmark of sophisticated ransomware groups and state-sponsored actors. It suggests that the attackers are not just looking for a quick hit but are performing reconnaissance for a more significant, long-term operation.
Microsoft’s Official Response and Mitigation Efforts
Microsoft has acknowledged the situation and is working to address the remaining vulnerabilities. In a statement, a Microsoft spokesperson emphasized the company’s commitment to security: "Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible. We also support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure."
The company confirmed that CVE-2026-33825 (BlueHammer) has been addressed and urged all users to apply the April 2026 updates immediately. However, the lack of official patches for RedSun and UnDefend at the time of writing remains a point of concern for IT administrators. Microsoft is reportedly working on out-of-band updates or signature-based detections to mitigate the impact of these remaining flaws.
Broader Cybersecurity Implications: The Defender Paradox
The exploitation of Microsoft Defender presents a unique paradox in cybersecurity. As an integrated, "always-on" security solution, Defender is one of the most effective tools for stopping common malware. However, its ubiquity also makes it a "single point of failure." If an attacker finds a way to subvert the very tool meant to protect the system, the rest of the OS becomes significantly more vulnerable.
This incident also highlights the risks associated with "Living off the Land" (LotL) techniques. Attackers are increasingly moving away from bringing their own malware into a system, which is easily detected. Instead, they use built-in Windows tools and vulnerabilities in security software to achieve their goals. By turning Defender against itself, attackers can operate in a way that appears legitimate to many basic monitoring tools.
Furthermore, the "retaliatory" disclosure by Chaotic Eclipse underscores a fracturing relationship between independent researchers and "Big Tech." As bug bounty programs become more complex and legal frameworks more stringent, some researchers feel marginalized, leading to more frequent public releases of unpatched flaws. This trend poses a significant challenge for global cybersecurity stability.
Strategic Recommendations for Organizations
In light of the active exploitation of these Defender vulnerabilities, security experts recommend a multi-layered defense strategy:
- Immediate Patching: Ensure that the April 2026 Patch Tuesday updates are applied to all Windows systems to close the BlueHammer (CVE-2026-33825) loophole.
- Enhanced Monitoring: Utilize Endpoint Detection and Response (EDR) tools to look for the specific enumeration commands mentioned by Huntress. Unusual use of
whoamiornet groupby non-administrative accounts should trigger an immediate investigation. - Definition Update Tracking: Monitor the status of Windows Defender definition updates. If a system suddenly stops receiving updates or shows "Update Failed" errors repeatedly, it could be a sign of an UnDefend exploitation.
- Network Segmentation: Limit the ability of a single compromised endpoint to communicate with sensitive parts of the network. This prevents the lateral movement that often follows a privilege escalation attack.
- Review Disclosure Policies: For larger organizations, participating in and supporting the vulnerability disclosure community can provide early warnings of emerging threats before they are weaponized.
As the situation evolves, the cybersecurity community remains on high alert. The exploitation of core security components like Microsoft Defender serves as a stark reminder that no software is infallible and that the speed of modern threat actors requires an equally rapid and transparent response from vendors and researchers alike.