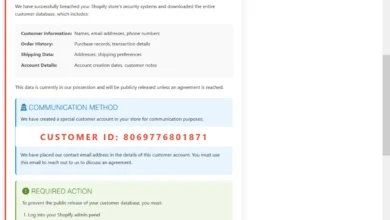
Critical Systemic Vulnerability in Anthropic Model Context Protocol Exposes Global AI Supply Chain to Remote Code Execution Attacks
Cybersecurity researchers have identified a foundational security flaw within the architecture of the Model Context Protocol (MCP), a standardized framework developed by Anthropic to facilitate communication between artificial intelligence models and external data sources. The vulnerability, described as being "by design," creates a direct pathway for remote code execution (RCE) on systems utilizing the protocol, potentially compromising a vast ecosystem of AI-driven applications and services. According to an extensive analysis published by OX Security, the flaw is rooted in the protocol’s core software development kits (SDKs) and has already rippled through the global AI supply chain, affecting millions of users and thousands of production environments.
The discovery, credited to researchers Moshe Siman Tov Bustan, Mustafa Naamnih, Nir Zadok, and Roni Bar, highlights a systemic weakness in how MCP handles configuration over its standard input/output (STDIO) transport interface. By exploiting unsafe default settings, an attacker can execute arbitrary commands on a host system, granting them unauthorized access to sensitive internal databases, API credentials, chat histories, and other private user data. The impact is significant, as the vulnerability is baked into the official Anthropic MCP SDKs across multiple programming languages, including Python, TypeScript, Java, and Rust.
The Architecture of a Systemic Risk
The Model Context Protocol was introduced to solve a growing problem in the AI industry: the lack of a universal standard for connecting Large Language Models (LLMs) to the tools and data they need to be effective. Before MCP, developers had to create custom integrations for every new data source, a process that was both time-consuming and prone to error. MCP aimed to provide a "plug-and-play" interface, allowing AI agents to seamlessly interact with everything from local file systems to complex enterprise databases.
However, the very ease of integration that made MCP popular has become its primary security liability. At the heart of the issue is the STDIO transport mechanism. In a standard implementation, the protocol allows an LLM to initiate a local server process to handle data requests. The researchers found that the MCP SDKs provide a direct "configuration-to-command" execution path. While this was intended to allow the LLM to start a local server and receive a handle for communication, the implementation fails to sufficiently sanitize or restrict the commands being executed.

"In practice, this allows anyone to run any arbitrary operating system command," the OX Security team explained. "If the command successfully creates an STDIO server, it returns the handle. However, even if the command is entirely unrelated to the protocol, the system executes it first and only returns an error after the damage is done."
This behavior effectively turns a configuration file or a dynamic request into a high-privileged command prompt. Because many AI applications are designed to be autonomous—taking instructions from users or external triggers—an attacker can craft a prompt that tricks the AI into sending a malicious configuration string to the MCP interface, resulting in full system compromise.
Mapping the Impact: 150 Million Downloads at Risk
The scale of the vulnerability is staggering, leading researchers to label it "the mother of all AI supply chains." Data gathered by OX Security indicates that the flaw affects more than 7,000 publicly accessible servers and software packages. Collectively, the impacted libraries and frameworks have been downloaded more than 150 million times, illustrating the rapid adoption of MCP within the developer community.
The systemic nature of the flaw means that any project built on top of the vulnerable Anthropic SDKs inherits the RCE risk. The researchers identified at least 10 major vulnerabilities across several of the most popular AI development frameworks, including:
- LiteLLM: A widely used proxy for interacting with multiple LLMs.
- LangChain and LangFlow: Leading frameworks for building LLM-powered applications and workflows.
- Flowise: A low-code tool for creating AI agents.
- LettaAI and LangBot: Emerging platforms for AI-driven automation and communication.
The researchers categorized the vulnerabilities into four primary attack vectors: command injection through environment variables, insecure parsing of configuration files, lack of validation in binary execution paths, and the exposure of internal handles to external inputs. In each case, the underlying cause was the protocol’s reliance on the host operating system to execute commands without a robust security sandbox or permission layer.

Chronology of Discovery and Industry Response
The path to discovering this systemic flaw was paved by a series of individual security reports over the past year. While these earlier reports focused on specific software implementations, they collectively pointed toward a deeper, architectural problem within the MCP itself.
- Mid-2025: Initial reports surfaced regarding CVE-2025-49596, a vulnerability in the MCP Inspector tool that allowed for localized code execution.
- Late 2025: Security audits of AI-integrated editors and chat platforms led to the discovery of CVE-2025-54136 in Cursor and CVE-2025-54994 in the
@akoskm/create-mcp-server-stdiopackage. - Early 2026: Further vulnerabilities were documented in WeKnora (CVE-2026-22688) and LibreChat (CVE-2026-22252), confirming that the issue was not isolated to a single developer’s mistake.
- April 2026: OX Security published its comprehensive analysis, linking these disparate CVEs to the core Anthropic MCP SDKs and declaring the issue a systemic supply chain threat.
Despite the mounting evidence and the severity of the RCE risk, Anthropic has reportedly declined to alter the fundamental architecture of the protocol. In communications with researchers, the company characterized the current behavior as "expected," arguing that the protocol is designed for local use cases where the user already has control over the environment.
However, the cybersecurity community has pushed back against this assessment. Analysts argue that in the modern cloud-native world, "local" interfaces are frequently exposed to remote triggers, especially when integrated into web-facing AI agents. By leaving the reference implementation unpatched, Anthropic has placed the burden of security entirely on downstream developers, many of whom may not be aware of the inherent risks within the protocol they are adopting.
Technical Implications and Attack Scenarios
The implications of an RCE vulnerability in an AI protocol are particularly severe because AI systems often have privileged access to organizational data. A successful exploit could allow an attacker to move laterally through a network, escalating their privileges from a simple AI chat interface to the core infrastructure of an enterprise.
Consider a scenario where a company uses an MCP-enabled AI agent to analyze internal financial reports. If an attacker can send a malicious document to that agent—or even a specially crafted email that the agent is programmed to read—they could trigger an MCP command that installs a backdoor on the server. Because the AI agent is viewed as a "trusted" internal entity, its malicious actions might bypass traditional signature-based security tools.

Furthermore, the "by design" nature of the flaw makes it difficult to patch without breaking backward compatibility. If Anthropic were to introduce strict command whitelisting or sandboxing into the SDK, thousands of existing MCP servers might cease to function correctly, requiring a massive, coordinated update across the entire AI ecosystem.
Mitigation Strategies for Developers and Enterprises
In the absence of a central fix from Anthropic, security experts are urging developers to implement several defensive layers to protect their systems. The following best practices are recommended for any organization currently using or planning to deploy MCP-based tools:
- Network Isolation: Ensure that MCP-enabled services are never directly accessible from the public internet. Block public IP access to any port associated with MCP STDIO transports.
- Sandboxing: Run MCP servers and the AI agents that interact with them in highly restricted environments, such as Docker containers with minimal privileges or specialized gVisor/Firecracker micro-VMs.
- Input Validation: Treat every piece of external data—whether it comes from a user prompt, an API call, or a file—as untrusted. Never allow external input to directly influence the configuration strings passed to the MCP SDK.
- Monitoring and Logging: Implement detailed logging for all MCP tool invocations. Monitor for unusual process creation or shell commands originating from AI service accounts.
- Verified Sources: Only install and run MCP servers from known, verified sources. Avoid the use of third-party "community" MCP servers unless a thorough code audit has been performed.
A Turning Point for AI Security
The controversy surrounding the Model Context Protocol serves as a stark reminder of the "security debt" being accumulated during the current AI gold rush. As companies race to integrate LLMs into every facet of their operations, the underlying protocols and standards are often being built with a focus on functionality and speed rather than "Secure by Design" principles.
The OX Security report concludes that the MCP vulnerability is a landmark case in AI security. "What made this a supply chain event rather than a single CVE is that one architectural decision, made once, propagated silently into every language, every downstream library, and every project that trusted the protocol to be what it appeared to be," the researchers stated.
As AI continues to transition from experimental chatbots to autonomous agents capable of interacting with the physical and digital world, the security of the protocols that govern those interactions will become as critical as the security of the internet’s foundational layers. For now, the AI industry remains at a crossroads, forced to decide whether to prioritize the convenience of open protocols or the rigorous safety standards required to protect the global digital infrastructure.