Apple Issues Critical Security Updates to Address Actively Exploited Zero-Day Vulnerabilities in iOS and macOS

Apple has issued an urgent call to action for users of iPhones, iPads, and Mac computers, releasing a series of emergency security patches to address two sophisticated zero-day vulnerabilities currently being exploited by threat actors in the wild. The updates, which arrived on Wednesday, target critical flaws within the operating system’s kernel and the WebKit browser engine, both of which provide a pathway for attackers to gain full administrative control over affected devices. Security experts warn that these vulnerabilities are particularly dangerous because they allow for arbitrary code execution with the highest levels of system privileges, potentially enabling a "Pegasus-like" surveillance scenario if left unpatched.
The software updates—identified as iOS 15.6.1, iPadOS 15.6.1, and macOS Monterey 12.5.1—are designed to close security gaps that impact nearly every modern Apple device. According to Apple’s official security advisories, the vulnerabilities were discovered and reported by an anonymous researcher. While the tech giant has maintained its characteristic discretion regarding the identity of the attackers or the specific targets of the exploits, the admission that the flaws "may have been actively exploited" has sent ripples through the cybersecurity community, prompting immediate warnings from government agencies and private security firms alike.
Technical Analysis of the Vulnerabilities
The two vulnerabilities, tracked as CVE-2022-32894 and CVE-2022-32893, represent a classic "one-two punch" in the world of cyber exploitation. The first, CVE-2022-32894, is a kernel-level bug found in both iOS and macOS. The kernel is the most sensitive part of the operating system, serving as the bridge between software and hardware. Apple described the flaw as an "out-of-bounds write issue" that was addressed through "improved bounds checking." In technical terms, an out-of-bounds write occurs when a program writes data past the end of its intended buffer, potentially overwriting adjacent memory locations. When this happens in the kernel, an attacker can execute arbitrary code with kernel privileges, essentially giving them the "keys to the kingdom." With kernel access, a threat actor can bypass all security permissions, access encrypted data, monitor communications, and even disable security software.
The second vulnerability, CVE-2022-32893, resides in WebKit, the open-source web browser engine that powers Safari and serves as the foundation for all web browsers on iOS and iPadOS. Because Apple requires all third-party browsers on its mobile platforms—including Google Chrome and Mozilla Firefox—to use the WebKit engine, this flaw has a massive attack surface. Similar to the kernel bug, this is an out-of-bounds write issue. It allows a remote attacker to execute code on a device simply by tricking a user into visiting a "maliciously crafted" website. Once the WebKit flaw is exploited, the attacker can then use the kernel vulnerability to escalate their privileges, completing a full device takeover without the user ever realizing their security has been compromised.
Chronology and Context of the Discovery
The release of these patches follows a busy year for Apple’s security teams. The tech industry has seen a notable increase in the discovery of zero-day vulnerabilities—security flaws that are discovered by attackers before the software vendor is aware of them. This latest incident marks the seventh and eighth zero-day vulnerabilities Apple has had to patch in 2022 alone.
Earlier in the year, Apple addressed similar flaws that were being utilized in targeted attacks against journalists and political dissidents. The timeline of these discoveries suggests that sophisticated threat actors are increasingly focusing their resources on mobile ecosystems. As mobile devices have become the primary repositories for personal and corporate data, the "bounty" for a working exploit chain on iOS has skyrocketed, with some private exploit brokers offering millions of dollars for zero-click vulnerabilities that require no interaction from the user.
The discovery of these latest flaws coincides with a broader industry trend. Just days prior to Apple’s announcement, Google released an emergency update for its Chrome browser to address its fifth zero-day of the year. This suggests a heightened state of activity among advanced persistent threat (APT) groups, who are likely racing to utilize these exploits before they are discovered and neutralized by vendors.
Expert Reactions and the "Pegasus" Comparison
The severity of the situation has led security experts to draw parallels to the Pegasus spyware developed by the NSO Group. Pegasus gained international notoriety for its ability to infect iPhones through "zero-click" exploits, allowing state actors to monitor the activities of activists, heads of state, and journalists.
Rachel Tobac, CEO of SocialProof Security, emphasized the urgency of the situation on social media, advising the general public to update their software by the end of the day. However, for individuals with an "elevated threat model"—such as journalists, activists, or those targeted by nation-states—Tobac warned that the update must be performed immediately. The concern is that these vulnerabilities provide exactly the kind of entry point needed for high-end spyware to be installed remotely.
Andrew Whaley, Senior Technical Director at Norwegian app security company Promon, noted that the ubiquity of iPhones makes these flaws particularly concerning. "While we all rely on our mobile devices, they are not invulnerable, and as users we need to maintain our guard just like we do on desktop operating systems," Whaley stated. He further argued that the responsibility for security should not rest solely on the OS provider. Whaley suggested that app developers, particularly those in the banking and fintech sectors, should implement their own layers of security controls to protect user data, rather than relying entirely on the underlying integrity of the operating system.
The Broader Impact on the Apple Ecosystem
The list of affected devices is extensive, covering nearly the entire current user base of Apple products. For iOS and iPadOS, the update is required for the iPhone 6s and later, all models of the iPad Pro, the iPad Air 2 and later, iPad 5th generation and later, iPad mini 4 and later, and the iPod touch (7th generation). For Mac users, the patch is available for those running macOS Monterey, though Apple also released updates for older operating systems like Big Sur and Catalina to address related WebKit issues, highlighting the pervasive nature of the code in question.
This incident underscores a growing tension in the tech world: as Apple continues to market its devices as the gold standard for privacy and security, the constant discovery of high-stakes vulnerabilities challenges that narrative. However, proponents of Apple’s ecosystem argue that the company’s ability to push out universal updates to millions of devices simultaneously is its greatest security strength. Unlike the fragmented Android ecosystem, where security patches must often go through manufacturers and carriers before reaching the end-user, Apple can close a security hole globally within hours of a fix being finalized.
Analysis of the Threat Landscape
The shift toward targeting the kernel and browser engines is a strategic move by threat actors. As operating systems become more "sandboxed"—a security practice where apps are isolated from each other and the system core—attackers must find flaws in the very components that manage those sandboxes. WebKit is a frequent target because it is the "window" through which the device interacts with the outside world. By compromising the browser engine, an attacker can bypass the first layer of defense.
Furthermore, the anonymous nature of the researcher who discovered these flaws has led to speculation within the industry. Often, these researchers are part of internal "Red Teams" or independent "bug bounty" hunters. However, in some cases, these vulnerabilities are discovered by monitoring the activity of known hacking groups. The fact that Apple acknowledged the "active exploit" status of these bugs indicates that they likely have telemetry or evidence of the flaw being used in a real-world attack, rather than just a theoretical proof-of-concept.
Recommendations for Users and Organizations
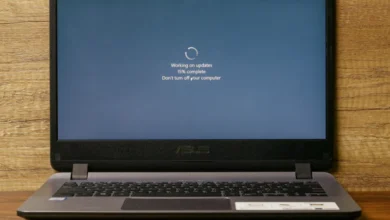
For individual users, the recommendation from cybersecurity professionals is clear: navigate to the "Settings" menu on your iPhone or iPad, select "General," and then "Software Update" to install iOS 15.6.1. Mac users should access "System Preferences" and select "Software Update" to install macOS Monterey 12.5.1.
For organizations, this event serves as a reminder of the importance of Mobile Device Management (MDM) solutions. Companies that allow employees to use personal devices for work (BYOD) or provide corporate-issued iPhones must ensure that they have the capability to enforce mandatory updates. A single unpatched device in a corporate network could serve as an entry point for a broader lateral attack on the company’s infrastructure.
Additionally, the incident highlights the need for a multi-layered security approach. While OS patches are critical, they are not a panacea. Users are encouraged to remain vigilant against phishing attempts, which remain the most common delivery mechanism for malicious links that trigger WebKit exploits.
Conclusion
The discovery and subsequent patching of CVE-2022-32894 and CVE-2022-32893 serve as a stark reminder of the ongoing arms race between software developers and cybercriminals. As our lives become increasingly digital, the devices we carry in our pockets represent both our greatest tools and our greatest vulnerabilities. Apple’s rapid response in deploying these patches is a necessary step in mitigating a significant threat, but the "active exploit" status of these zero-days suggests that for some users, the race to update may already be a race against an intruder already inside the gates. As the cybersecurity landscape continues to evolve, the burden of security remains a shared responsibility between the manufacturers who write the code, the developers who build the apps, and the users who must remain proactive in maintaining their digital defenses.