authentication
-
Cybersecurity and Privacy
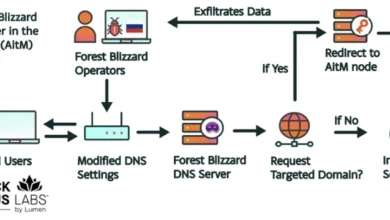
Russian Intelligence Operatives Leverage Global SOHO Router Network to Harvest Microsoft Authentication Tokens at Scale
Cybersecurity researchers have uncovered a massive, state-sponsored espionage campaign orchestrated by Russian military intelligence, which successfully compromised more than 18,000…
Read More »
