Seiko USA Website Defaced as Cybercriminals Claim Theft of Shopify Customer Database and Demand Ransom Payment
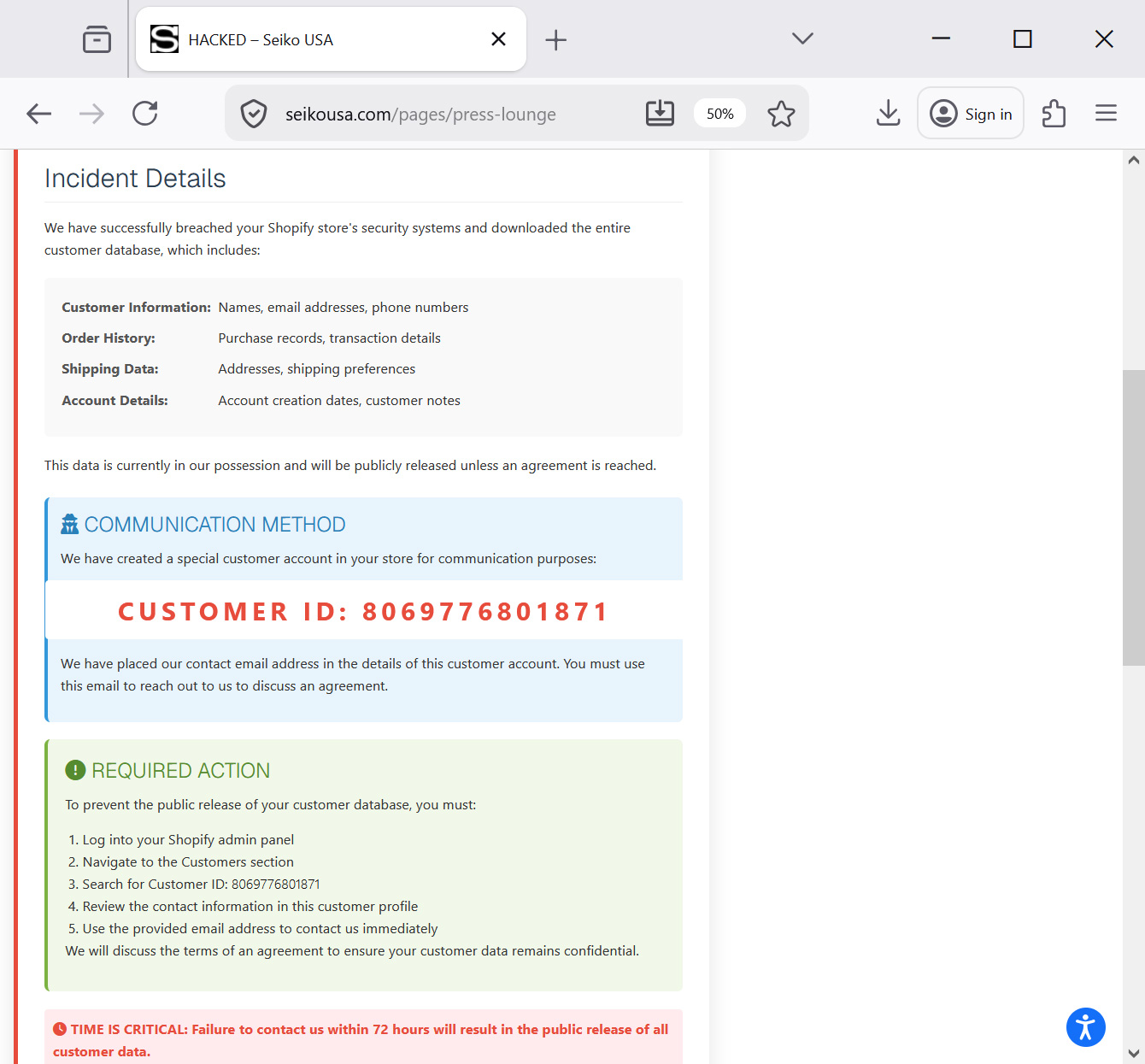
The official website of Seiko USA became the target of a high-profile cyberattack over the weekend, resulting in the defacement of its "Press Lounge" section and the public airing of an extortion demand. Visitors to the compromised portion of the site were greeted by a stark "HACKED" headline, replacing the company’s standard media and corporate communications content with a detailed ransom note. The attackers, whose identities remain unverified, claimed to have successfully infiltrated the company’s Shopify backend, exfiltrating a comprehensive database containing sensitive customer information. This incident marks a significant security breach for the American subsidiary of the renowned Japanese watchmaker, raising urgent questions regarding the security of third-party e-commerce platforms and the protection of consumer data in the digital retail landscape.
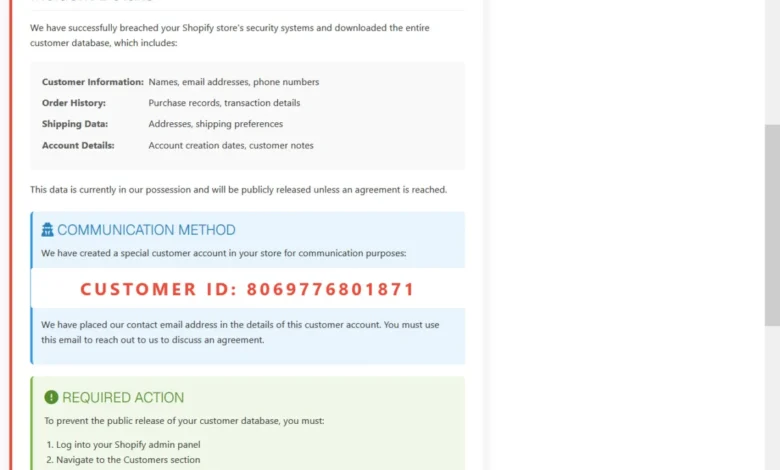
The message displayed on the defaced webpage was framed as an "urgent security notification" directed at the company’s management. In a bold display of confidence, the threat actors asserted that they had bypassed Seiko USA’s security protocols and "downloaded the entire customer database." While the full extent of the compromised data was not immediately detailed in the public-facing note, the attackers explicitly threatened to release the information to the public domain unless Seiko USA entered into ransom negotiations within a strictly defined timeframe. To facilitate communication, the hackers provided a non-traditional instruction: rather than providing a dark web link or a standard email address, they directed Seiko’s IT and administrative staff to locate a specific customer account within the Shopify admin panel—identified by ID 8069776801871—where a contact email address had been surreptitiously added to the profile.
Chronology of the Cyberattack and Immediate Response
The breach was first detected over the weekend when cybersecurity monitors and observant visitors noticed the anomalous content on the Seiko USA Press Lounge. The defacement appears to have been a calculated move to ensure maximum visibility to both the company and the public, utilizing a section of the site often frequented by journalists and industry analysts. By Sunday evening, the "HACKED" banner and the accompanying extortion text were the primary features of the page, signaling a total loss of administrative control over that specific web directory.
Upon the discovery of the defacement, the attackers initiated a 72-hour countdown. They warned that the failure to establish contact via the compromised Shopify account profile would result in the immediate publication of the stolen database. This tactic, known as "double extortion" without the traditional deployment of ransomware, has become increasingly common among cybercriminal groups who prioritize data theft over system encryption. By threatening a public leak, attackers aim to force a settlement by leveraging the potential for regulatory fines, reputational damage, and the loss of customer trust.

In the hours following the public discovery of the breach, Seiko USA took steps to mitigate the visible damage. The defaced "Press Lounge" page was taken offline or restored to its original state, effectively removing the attackers’ message from public view. However, as of the time of publication, Seiko USA has not issued a formal statement regarding the validity of the data theft claims or the current status of their Shopify environment’s security. Requests for comment from major cybersecurity news outlets, including BleepingComputer, have so far gone unanswered by the company’s corporate communications team.
Technical Analysis of the Shopify Infiltration Claim
The attackers’ claim of gaining access to the Shopify backend is particularly concerning given the platform’s widespread use among major retail brands. Shopify is a multi-tenant SaaS (Software as a Service) platform, meaning that while the core infrastructure is managed by Shopify, the individual "storefronts" and their associated data are managed by the brand. Security breaches in such environments typically occur not through a failure of Shopify’s central systems, but through compromised administrative credentials, insecure third-party application integrations (apps), or the exploitation of API keys.
In this instance, the attackers’ ability to modify a specific customer profile (ID 8069776801871) strongly suggests they had administrative or "Staff" level access to the Shopify admin panel. This level of access would theoretically allow them to export customer lists, view order histories, and potentially access sensitive payment metadata, although Shopify generally masks full credit card numbers to comply with PCI-DSS standards. The specific nature of the data allegedly stolen likely includes:
- Full names of customers
- Email addresses and phone numbers
- Shipping and billing addresses
- Order histories and purchase values
- Account creation dates and login metadata
The use of the website defacement as a notification tool suggests the attackers wanted to ensure their presence was known immediately, bypassing internal security filters that might have caught a standard ransom email. By placing the demand on the public website, they essentially "shamed" the company into acknowledging the breach.
Historical Context: Seiko’s Previous Cybersecurity Challenges
This is not the first time the Seiko brand has faced a significant cybersecurity crisis. In August 2023, the global Seiko Group Corporation confirmed a massive data breach involving its primary servers in Japan. That attack was eventually claimed by the BlackCat (also known as ALPHV) ransomware gang. In that previous incident, the hackers claimed to have stolen over 60,000 items of data, including technical drawings of watch movements, employee details, and confidential business correspondence.

The 2023 attack highlighted vulnerabilities in Seiko’s global infrastructure and forced the company to undergo a comprehensive security overhaul. The current incident involving the USA subsidiary and its Shopify platform suggests that while the core Japanese servers may have been hardened, localized e-commerce divisions remain attractive targets for opportunistic threat actors. The shift from a complex ransomware attack on manufacturing infrastructure to a direct data theft and defacement attack on a retail-facing site indicates a persistent interest in the Seiko brand by various tiers of the cybercrime ecosystem.
Broader Implications for the Retail and Luxury Sector
The attack on Seiko USA underscores a growing trend in the retail sector where cybercriminals target the digital supply chain and e-commerce platforms rather than traditional corporate networks. As brands move toward "Direct-to-Consumer" (DTC) models, they accumulate vast amounts of personally identifiable information (PII) that is highly valuable on the dark web.
The Threat of Data Leaks and Regulatory Scrutiny
Under the California Consumer Privacy Act (CCPA) and other state-level data protection laws in the United States, Seiko USA could face significant legal and financial repercussions if it is proven that customer PII was compromised due to inadequate security measures. Regulators often look at whether Multi-Factor Authentication (MFA) was enabled on administrative accounts and whether API access was properly audited. If the 72-hour deadline passes and the attackers follow through on their threat to leak the database, the company will be legally obligated to notify all affected individuals, a process that is both costly and damaging to brand equity.
The "Extortion-Only" Evolution
This incident reflects the evolution of cybercrime tactics. Many groups are moving away from the "loud" process of encrypting files (ransomware), which often triggers immediate defensive responses and backups. Instead, they opt for "silent" data exfiltration followed by a "loud" public demand. This approach is often more effective in the retail sector, where the value of the business lies in its customer relationships and data privacy rather than just the uptime of its manufacturing plants.
Expert Recommendations and Mitigation Strategies
While the situation at Seiko USA is still unfolding, cybersecurity experts suggest that companies operating on platforms like Shopify must take proactive steps to prevent similar occurrences. These include:
- Mandatory MFA: Ensuring that every staff account with access to the Shopify admin panel requires hardware-based or app-based multi-factor authentication.
- Third-Party App Audits: Regularly reviewing the permissions granted to third-party Shopify apps, as these are frequent entry points for attackers.
- API Key Management: Rotating API keys and ensuring they are not hardcoded in public-facing scripts or stored in insecure repositories.
- Monitoring for Defacement: Utilizing automated tools to monitor website integrity and alert IT teams to unauthorized changes in real-time.
For customers of Seiko USA, the current advice is to remain vigilant. While there is no evidence yet that the stolen data has been used for fraudulent purposes, individuals who have made purchases through the site should be on the lookout for targeted phishing attempts. Cybercriminals often use stolen order histories to craft highly convincing emails that appear to be from the brand, asking for further "verification" of payment details.
Conclusion
The defacement of the Seiko USA website and the subsequent extortion threat serve as a stark reminder of the vulnerabilities inherent in modern e-commerce. As the 72-hour ultimatum looms, the industry remains focused on how Seiko will respond. Whether the company chooses to negotiate, ignores the threat, or reveals that the "breach" was less severe than claimed, the event has already added to the growing list of high-profile retail security failures in 2024. For a brand that prides itself on precision and reliability, the coming days will be a critical test of its digital resilience and its commitment to consumer privacy.
Further updates on this story are expected as Seiko USA completes its internal investigation and as the deadline set by the threat actors approaches. For now, the "Press Lounge" remains a focal point of a digital standoff that highlights the high stakes of corporate cybersecurity in the age of global e-commerce.
