Global Security Risk Intensifies as Over 80,000 Hikvision Surveillance Cameras Remain Vulnerable to Critical Year Old Command Injection Flaw

A comprehensive report from cybersecurity firm Cyfirma has revealed that more than 80,000 Hikvision surveillance cameras distributed globally continue to operate with a critical, unpatched security vulnerability, nearly a year after a fix was officially released. The flaw, identified as CVE-2021-36260, represents one of the most significant risks to the Internet of Things (IoT) landscape in recent years, primarily due to the widespread adoption of Hikvision hardware in both public and private sectors. Despite the availability of a firmware patch since September 2021, the persistence of these vulnerable devices highlights a systemic failure in vulnerability management and IoT maintenance across more than 100 countries.
Hikvision, formally known as Hangzhou Hikvision Digital Technology, is a Chinese state-owned manufacturer and the world’s largest supplier of video surveillance equipment. While the company maintains a dominant market share, its relationship with the Chinese government has made it a focal point of geopolitical tension. In 2019, the United States Federal Communications Commission (FCC) designated Hikvision as an "unacceptable risk to U.S. national security," yet the brand remains ubiquitous in corporate offices, residential complexes, and critical infrastructure sites worldwide. The discovery that tens of thousands of these devices are currently susceptible to remote hijacking underscores the urgent need for a shift in how organizations manage their physical security hardware.
Understanding CVE-2021-36260: A Critical Gateway for Attackers
The vulnerability at the heart of this crisis is a command injection flaw that resides in the webserver of several Hikvision camera models. When the National Institute of Standards and Technology (NIST) analyzed the exploit, it assigned it a Common Vulnerability Scoring System (CVSS) score of 9.8 out of 10. This "critical" rating is reserved for vulnerabilities that require no user interaction, can be exploited remotely, and allow for a complete takeover of the affected system.
In technical terms, the flaw allows an attacker to send specially crafted messages to the device’s web interface. Because the input is not properly validated, the attacker can execute arbitrary commands with "root" privileges—the highest level of access available. Once an attacker gains root access, they effectively own the device. They can view live video feeds, download archived footage, disable the camera entirely, or use the device as a "pivot point" to launch further attacks into the organization’s internal network. This ability to move laterally is particularly dangerous for businesses that do not isolate their IoT devices from their primary data networks.
A Chronology of the Vulnerability and Response
The timeline of CVE-2021-36260 illustrates a troubling gap between the identification of a threat and the implementation of a solution. The vulnerability was first discovered and reported by a security researcher known as "Watchfull" in the summer of 2021. Recognizing the severity of the flaw, Hikvision worked to develop a fix, officially releasing a firmware update on September 19, 2021.
By late 2021, security researchers began observing active attempts to exploit the flaw in the wild. Initial reports suggested that botnet operators were targeting the cameras to enlist them into Mirai-style Distributed Denial of Service (DDoS) networks. However, as the months progressed, the nature of the threat evolved. By mid-2022, when Cyfirma conducted its research, the focus had shifted toward more targeted exploitation.
In August 2022, Cyfirma’s analysis confirmed that over 80,000 devices across 2,300 organizations remained unpatched. This data indicates that despite the global publicity surrounding the initial disclosure, a significant portion of the user base failed to take action. The chronology suggests that the "set it and forget it" mentality regarding surveillance hardware has created a long-tail security risk that threat actors are now actively harvesting.
Dark Web Activity and the Involvement of Advanced Threat Actors
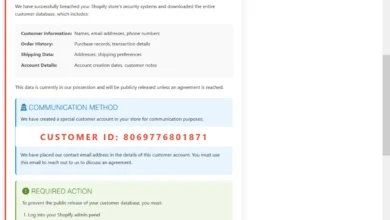
The Cyfirma report shed light on the burgeoning underground market for Hikvision exploits. Researchers discovered multiple instances on Russian-speaking dark web forums where hackers were collaborating to exploit the command injection vulnerability. These discussions often included the sharing of "combolists"—databases of leaked credentials—alongside instructions on how to use automated tools to scan the internet for vulnerable Hikvision hardware.
The threat is not limited to opportunistic cybercriminals or botnet operators. The report identified potential interest from sophisticated State-Sponsored Advanced Persistent Threat (APT) groups. Specifically, groups such as APT41 (also known as MISSION2025) and APT10, both of which have historical links to Chinese intelligence operations, were named as entities that could leverage these vulnerabilities. Additionally, unknown Russian threat actors are suspected of seeking access to these devices to fulfill geopolitical motives.
In the context of modern warfare and espionage, access to a nation’s surveillance infrastructure is an invaluable asset. A compromised camera in a government building or a shipping port provides more than just a visual feed; it provides metadata about personnel movements, operational patterns, and potential physical security weaknesses. The fact that these cameras remain open to exploitation nearly a year after a patch was issued represents a massive intelligence windfall for any motivated adversary.
The Systemic Challenges of IoT Security
The persistence of the Hikvision vulnerability highlights the unique challenges inherent in securing the Internet of Things. Unlike a modern smartphone or a desktop operating system, which frequently pushes automatic updates to users, IoT devices often lack a standardized, user-friendly update mechanism.
Paul Bischoff, a privacy advocate at Comparitech, noted that the burden of security for these devices falls almost entirely on the end-user. "Updates are not automatic; users need to manually download and install them, and many users might never get the message," Bischoff explained. This manual process requires the user to be aware that a vulnerability exists, locate the correct firmware on the manufacturer’s website, and successfully flash it onto the device. For many small business owners or residential users, this process is prohibitively complex or simply overlooked.
Furthermore, Hikvision cameras are frequently deployed with default credentials. Even if the command injection flaw is patched, many devices remain accessible via the open internet because they use "admin/12345" or similar factory-set passwords. Search engines like Shodan and Censys allow attackers to filter for Hikvision devices specifically, making it trivial to find thousands of targets in a matter of seconds.
David Maynor, senior director of threat intelligence at Cybrary, pointed out that the security architecture of these devices is often flawed from the start. "Their product contains easy to exploit systemic vulnerabilities or worse, uses default credentials," Maynor stated. He also highlighted a critical issue for incident response: "There is no good way to perform forensics or verify that an attacker has been excised." This means that even if an organization patches its cameras today, they may have no way of knowing if an attacker has already planted a persistent backdoor within the system.
National Security and the Regulatory Landscape
The Hikvision crisis has reignited debates regarding the security of supply chains and the risks of utilizing technology from state-owned enterprises in sensitive environments. The FCC’s 2019 decision to label Hikvision a national security risk was followed by the Secure Equipment Act of 2021, which effectively prohibits the FCC from reviewing or issuing new equipment licenses to companies on the "covered list."
Other nations have followed suit. The United Kingdom’s Government Communications Headquarters (GCHQ) has raised concerns about the use of Chinese-made surveillance tech in sensitive sites, and Australia has seen movements to strip such cameras from government buildings. However, these bans often apply only to new installations or specific government sectors, leaving the vast majority of existing infrastructure in the private sector untouched and unmonitored.
The geopolitical implications are significant. As tensions between the West and China continue to fluctuate, the presence of millions of Chinese-manufactured sensors in Western cities creates a "digital dual-use" scenario. While intended for safety and monitoring, these devices can be converted into tools for foreign intelligence gathering if left unmaintained and exposed.
Implications for Global Infrastructure and Business Continuity
The risks posed by 80,000 unpatched cameras extend beyond privacy concerns. For a corporation, a compromised camera system can lead to the theft of intellectual property through visual monitoring of whiteboards or laboratory environments. For a municipality, it can lead to the disruption of traffic management systems or the monitoring of law enforcement activities.
The financial implications of a breach are also substantial. Under frameworks like the General Data Protection Regulation (GDPR) in Europe, the failure to secure personal data—which includes video footage of identifiable individuals—can result in massive fines. Organizations that have neglected to patch their Hikvision hardware are essentially operating in a state of "willful negligence," which significantly increases their legal and insurance liabilities in the event of a cyberattack.
Moreover, the use of these cameras in DDoS attacks can have a cascading effect on global internet stability. A botnet comprised of tens of thousands of high-bandwidth cameras can generate enough traffic to take down major websites and services, causing millions of dollars in economic damage.
Conclusion: The Urgent Path Forward
The revelation that over 80,000 Hikvision cameras remain vulnerable to CVE-2021-36260 is a stark reminder of the "security debt" that currently plagues the global IoT ecosystem. As long as these devices remain connected to the internet without proper patching, they serve as a permanent invitation to cybercriminals and state-sponsored actors.
To mitigate this risk, organizations must move away from the "set it and forget it" model of physical security. Cybersecurity must be integrated into the maintenance lifecycle of every connected device. This includes regular firmware audits, the mandatory changing of default passwords, and the implementation of network segmentation to ensure that even if a camera is compromised, the broader corporate network remains isolated.
For the wider industry, this incident serves as a call for "Secure by Design" principles. Manufacturers must prioritize automatic update mechanisms and move away from default credentials to protect their users from the inherent complexities of manual maintenance. Until these systemic changes are made, the world’s surveillance infrastructure will remain a fragile link in the global security chain, vulnerable to the very threats it was designed to monitor.