Russian Intelligence Operatives Leverage Global SOHO Router Network to Harvest Microsoft Authentication Tokens at Scale
Cybersecurity researchers have uncovered a massive, state-sponsored espionage campaign orchestrated by Russian military intelligence, which successfully compromised more than 18,000 internet routers to facilitate the mass harvesting of Microsoft Office authentication tokens. The operation, attributed to the notorious threat actor known as Forest Blizzard, utilized a remarkably stealthy method of DNS hijacking that allowed the group to siphon sensitive credentials from thousands of networks globally without the need for traditional malware deployment.
Microsoft, in a joint disclosure with security division Black Lotus Labs, revealed today that the campaign targeted a diverse array of victims, including over 200 high-profile organizations and 5,000 individual consumer devices. By exploiting known vulnerabilities in older, unpatched hardware, the Russian General Staff Main Intelligence Directorate (GRU) was able to intercept secure communications and bypass modern security protocols, such as multi-factor authentication (MFA), by capturing OAuth tokens directly from the traffic stream.
The Evolution of APT28: From Malware to Infrastructure Manipulation
Forest Blizzard, also known in the cybersecurity community as APT28 or Fancy Bear, is a sophisticated hacking unit long associated with the GRU’s Unit 26165. The group has a documented history of high-stakes political interference and industrial espionage, most notably the 2016 breach of the Democratic National Committee (DNC) and the Hillary Clinton presidential campaign. While their previous operations often relied on bespoke malware and spear-phishing, this latest campaign represents a strategic shift toward infrastructure-level manipulation.
The transition to infrastructure-based attacks was highlighted by researchers at Black Lotus Labs, the security arm of internet backbone provider Lumen. According to their findings, Forest Blizzard reached the peak of its current activity in December 2025. The group’s surveillance dragnet focused on end-of-life or unsupported Small Office/Home Office (SOHO) routers, specifically those manufactured by Mikrotik and TP-Link. These devices, often neglected by users and administrators in terms of security updates, provided a perfect entry point for the GRU to build a persistent, global intercept network.
The Mechanics of the DNS Hijacking Campaign
The technical sophistication of the Forest Blizzard operation lies in its simplicity. Rather than attempting to infect end-user computers or mobile devices—which are often protected by modern antivirus and endpoint detection software—the attackers focused on the gateway to the internet: the router.
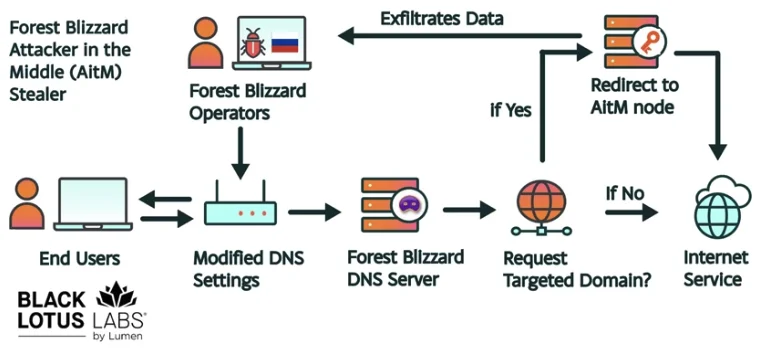
By exploiting unpatched vulnerabilities in the router firmware, the hackers gained administrative access and modified the device’s Domain Name System (DNS) settings. DNS serves as the "phonebook" of the internet, translating human-readable web addresses like "outlook.office.com" into the numerical IP addresses used by computers. By altering these settings, Forest Blizzard redirected specific DNS queries to malicious servers under their control.
Ryan English, a security engineer at Black Lotus Labs, noted that this "old-school" approach allowed the attackers to remain undetected for extended periods. "Everyone is looking for some sophisticated malware to drop something on your mobile devices," English explained. "These guys didn’t use malware. They did this in a graybeard way that isn’t really sexy, but it gets the job done."
Once the DNS settings were compromised, the attackers could perform Adversary-in-the-Middle (AiTM) attacks. When a user on a compromised network attempted to log into Microsoft Outlook or other Office services, their traffic was routed through a GRU-controlled proxy. This allowed the hackers to intercept Transport Layer Security (TLS) connections and capture OAuth authentication tokens.
Bypassing Multi-Factor Authentication via Token Siphoning
The most alarming aspect of this campaign is its ability to circumvent multi-factor authentication (MFA). In a typical secure login process, a user provides a password and then a secondary code (MFA). Once authenticated, the service issues an OAuth token—a digital "key" that allows the user to remain logged in for a set period without re-entering their credentials.

Because Forest Blizzard intercepted these tokens after the user had successfully completed the MFA process, the hackers gained immediate, direct access to the victim’s email and cloud accounts. This method allowed the GRU to bypass the very security measures that many organizations rely on as their primary line of defense. By siphoning these tokens, the attackers could impersonate the victims and access sensitive internal communications, law enforcement data, and diplomatic cables without ever needing to steal a single password.
Chronology of the Surveillance Dragnet
The timeline of the Forest Blizzard operation reveals a highly adaptive adversary that responds quickly to public disclosures.
- August 2025: The United Kingdom’s National Cyber Security Centre (NCSC) released a report detailing APT28’s use of malware on a small, targeted group of routers.
- Late August 2025: Almost immediately following the NCSC report, Forest Blizzard abandoned their malware-heavy approach. They pivoted to a more systemic, automated method of mass-altering DNS settings on thousands of vulnerable routers.
- December 2025: The campaign reached its zenith, with over 18,000 routers actively participating in the DNS hijacking network. The targets expanded from specific strategic entities to a broader net covering government agencies, ministries of foreign affairs, and third-party email providers.
- March 23, 2026: In response to the growing threat of foreign-controlled hardware, the U.S. Federal Communications Commission (FCC) announced a sweeping new policy regarding consumer-grade routers.
- April 2026: Microsoft and Lumen publicly disclosed the full scope of the Forest Blizzard activity, identifying the global impact on over 200 organizations.
Danny Adamitis, a researcher at Black Lotus Labs, emphasized that the group’s shift in tactics was a direct reaction to being "burned" by security researchers. "Before the last NCSC report came out, they used this capability in very limited instances," Adamitis said. "After the report was released, they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable."
Target Profiles and Global Impact
The targets of the Forest Blizzard campaign were not chosen at random. The GRU focused heavily on organizations that handle sensitive geopolitical information. This included law enforcement agencies, which hold records of criminal investigations and surveillance, and ministries of foreign affairs, which manage international relations and classified diplomatic traffic.
By targeting third-party email providers, the attackers were also able to gain a foothold in the communications infrastructure used by smaller businesses and private individuals who might be connected to high-value targets. The 18,000 compromised networks were spread across the globe, indicating that the GRU was seeking to cast as wide a net as possible to gather intelligence on a variety of international interests.
Regulatory Repercussions: The FCC’s Hardware Ban
The discovery of the Forest Blizzard operation has accelerated a major shift in U.S. technology policy. On March 23, the FCC announced it would no longer certify consumer-grade internet routers produced outside of the United States. This decision represents a dramatic escalation in the effort to secure the domestic supply chain against foreign interference.
The FCC’s "Covered List" update was driven by the realization that foreign-made routers, particularly those from nations considered adversarial, present an untenable risk. The commission warned that poorly secured routers could be leveraged to "immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons."
While the policy includes a provision for "conditional approval" from the Department of War or Department of Homeland Security, the move has faced criticism from industry experts who argue that it will severely limit consumer choice. Currently, very few consumer-grade routers are manufactured entirely within the United States, with Elon Musk’s Starlink—produced in Texas—being one of the few notable exceptions.
Analysis of Implications for Cybersecurity Strategy
The Forest Blizzard campaign serves as a stark reminder that the "perimeter" of a network is increasingly difficult to define. The vulnerability of SOHO devices highlights a significant gap in the global security posture: the "forgotten" hardware that sits between a secure enterprise network and the public internet.
- The Death of the Perimeter: As more employees work from home or in small satellite offices, the security of consumer-grade hardware becomes as critical as the security of the corporate data center.
- MFA is Not a Silver Bullet: While MFA remains essential, this campaign proves that it is not infallible. Organizations must look toward "Zero Trust" architectures that monitor for suspicious token usage and session hijacking.
- The Lifespan of Hardware: The use of end-of-life routers in this attack underscores the danger of legacy systems. Vendors and regulators may need to implement more aggressive "kill switches" or notification systems for devices that no longer receive security patches.
- Supply Chain Sovereignty: The FCC’s move toward domestic manufacturing signals a future where "hardware provenance" is a primary security metric. The world is moving toward a bifurcated technology market where trust is determined by the country of origin.
As Forest Blizzard and other state-backed actors continue to evolve, the burden of defense is shifting from reactive patching to proactive infrastructure management. For now, security experts recommend that all users of Mikrotik and TP-Link devices immediately check for firmware updates, change default administrative passwords, and, if the hardware is no longer supported by the manufacturer, replace it with a modern, secure alternative.





