Sanctioned Cryptocurrency Exchange Grinex Halts Operations After Claiming 13.7 Million Dollar Hack by Western Intelligence Agencies

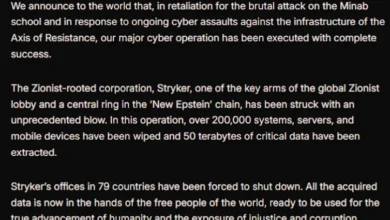
The Kyrgyzstan-incorporated cryptocurrency exchange Grinex, a platform long scrutinized by international regulators for its alleged role in facilitating Russian sanctions evasion, has officially suspended all operations. The closure follows a reported security breach on April 15, 2026, which the exchange claims resulted in the theft of approximately 1 billion Russian rubles, equivalent to roughly $13.74 million. In a provocative statement released shortly after the incident, Grinex leadership attributed the hack to the coordinated efforts of Western intelligence agencies, characterizing the event as an act of state-sponsored financial sabotage aimed at undermining Russia’s domestic economic stability.
The suspension marks a significant escalation in the ongoing digital and financial friction between Russian-linked crypto entities and Western regulatory bodies. While the exchange frames itself as a victim of geopolitical warfare, blockchain analytics firms and international law enforcement agencies suggest a more complex narrative, involving a history of money laundering, rebranding to evade sanctions, and the potential for a "false flag" operation designed to mask an internal collapse or a strategic exit.
The Breach and Immediate Aftermath
On the morning of April 15, 2026, at approximately 12:00 UTC, Grinex’s internal monitoring systems reportedly detected unauthorized withdrawals of Tether (USDT) and other digital assets. According to data provided by blockchain intelligence firms such as Elliptic and TRM Labs, the stolen funds were rapidly moved across the TRON and Ethereum blockchains. The attackers utilized high-velocity "frantic swapping" techniques, converting the stolen USDT into more decentralized assets like Ether (ETH) and Tron (TRX).
This specific tactic is a hallmark of sophisticated cybercriminal activity. By converting stablecoins like USDT—which are managed by central entities capable of "freezing" addresses—into native blockchain tokens, the perpetrators effectively neutralized the ability of issuers to recover the funds. Within hours of the initial exploit, the assets were distributed across approximately 70 unique addresses, making tracking and recovery efforts significantly more difficult for forensic investigators.
Grinex’s response was swift and laden with political rhetoric. In a statement posted to its official website, the company claimed that the "technological sophistication" and "unprecedented level of resources" required for the attack were capabilities "typically available exclusively to the agencies of hostile states." The exchange further alleged that the breach was not a standard criminal theft but a strategic strike intended to inflict "direct damage upon Russia’s financial sovereignty."
A History of Sanctions and Rebranding
To understand the weight of the Grinex closure, one must look at its lineage. Investigations by the U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) and the U.K.’s Office of Financial Sanctions Implementation (OFSI) have consistently identified Grinex as a successor or "rebrand" of Garantex.

Garantex was originally sanctioned by the U.S. in April 2022 for its role in laundering proceeds from the Hydra darknet market and the Conti ransomware group. Despite these sanctions, the entity proved resilient. By mid-2025, the Treasury Department renewed its focus on the group, noting that Garantex had continued to process over $100 million in illicit transactions. Blockchain analysts discovered that the exchange had migrated its core customer base to Grinex, a new entity incorporated in Kyrgyzstan, to bypass the 2022 restrictions.
Grinex maintained its operations by utilizing a ruble-backed stablecoin known as A7A5. This allowed the exchange to provide a bridge between the traditional Russian financial system and the global cryptocurrency market, effectively creating a "shadow" financial corridor. Reports from Elliptic in February 2026 highlighted that Rapira, a Moscow-linked exchange incorporated in Georgia, had moved over $72 million through Grinex, further cementing its status as a hub for sanctions evasion.
The TokenSpot Connection and Synchronized Downtime
The April 15 hack did not occur in isolation. TRM Labs identified that TokenSpot, another Kyrgyzstan-based exchange, was impacted by the same series of transactions. Investigators believe TokenSpot serves as a front for Grinex, providing additional layers of obfuscation for high-volume traders and state-linked actors.
On the day of the Grinex breach, TokenSpot posted a notice on its Telegram channel stating that the platform would be "temporarily unavailable due to technical maintenance." While TokenSpot claimed to have resumed operations the following day, forensic data showed that a small amount of capital—less than $5,000—was routed from TokenSpot addresses to the same consolidation wallets used in the Grinex exploit. This synchronization suggests that the two platforms share the same underlying infrastructure or are controlled by the same administrative group.
Expert Analysis: Hack or False Flag?
The claim that Western intelligence agencies orchestrated a $13.7 million theft has met with skepticism from the global cybersecurity community. While state-sponsored cyber operations are a reality of modern geopolitics, analysts at Chainalysis have raised the possibility that the incident could be a "false flag" attack.
A false flag in this context would involve the exchange’s own operators staging a hack to explain away missing funds, cover the tracks of illicit transfers, or provide a pretext for a permanent shutdown in the face of mounting international pressure. "Given the exchange’s heavily sanctioned status and its history of using obfuscation techniques, we must consider if this is a legitimate exploit or an orchestrated event by insiders," Chainalysis noted in its technical breakdown.
The "frantic swapping" of assets observed on the blockchain is a tactic often used by both hackers and insiders looking to launder money quickly before a platform goes dark. By blaming "hostile states," Grinex provides a politically convenient explanation to its Russian-based users and regulators, potentially shielding the operators from domestic legal repercussions for the loss of customer funds.

Broader Implications for Global Compliance
The collapse of Grinex represents a significant, albeit messy, disruption to the infrastructure supporting Russian sanctions evasion. Since the beginning of the conflict in Ukraine, the use of cryptocurrency as a tool to bypass the SWIFT banking network and traditional financial oversight has been a primary concern for the G7 nations.
-
Increased Pressure on "Neutral" Jurisdictions: The Grinex incident puts the spotlight back on jurisdictions like Kyrgyzstan and Georgia. Western regulators are likely to increase pressure on these nations to tighten their Anti-Money Laundering (AML) and Counter-Terrorism Financing (CTF) frameworks. The ease with which Grinex was able to incorporate and operate suggests a regulatory gap that state-linked actors are eager to exploit.
-
The Evolution of Stablecoin Risks: The use of the A7A5 ruble-backed stablecoin and the rapid conversion of USDT into ETH/TRX highlights the limitations of current stablecoin regulation. While Tether has shown a willingness to freeze addresses linked to criminal activity, the speed of the Grinex "hack" demonstrates how quickly assets can be moved into more permissionless environments where central intervention is impossible.
-
Geopolitical Weaponization of Cyber Claims: By framing a financial loss as an attack on "financial sovereignty," Grinex and its affiliates are contributing to a narrative of digital victimization. This could lead to further fragmentation of the global internet and financial systems, as nations look to build "sovereign" digital infrastructures that are insulated from Western influence—and oversight.
Timeline of Events: April 2026
- April 15, 12:00 UTC: Unusual outbound transaction volume detected from Grinex and TokenSpot wallets. Assets are converted from USDT to ETH and TRX.
- April 15, 14:00 UTC: TokenSpot announces "emergency technical maintenance" and suspends all user withdrawals.
- April 16: TokenSpot claims to resume full operations, though liquidity remains low. Analysts identify consolidation of funds into 70 high-risk addresses.
- April 18: Grinex officially suspends operations. The exchange releases a statement blaming Western intelligence agencies for the theft of 1 billion rubles.
- April 19: Blockchain analytics firms publish preliminary reports suggesting the "hack" mirrors the obfuscation patterns previously used by Garantex operators.
Conclusion
The suspension of Grinex is a pivotal moment in the ongoing "cat-and-mouse" game between international financial regulators and crypto-enabled sanctions evasion networks. Whether the $13.7 million loss was the result of a genuine state-sponsored cyber operation, a criminal exploit, or a calculated internal exit, the result is the same: one of the primary conduits for illicit Russian capital has been neutralized.
However, the history of this group suggests that the infrastructure may simply migrate once again. As Garantex became Grinex, the industry now watches to see what new entity might emerge from the ashes of this latest disruption. For global law enforcement, the challenge remains not just to shut down individual exchanges, but to dismantle the decentralized networks and jurisdictional loopholes that allow these "shadow" platforms to persist in the first face of global sanctions. The Grinex saga serves as a stark reminder that in the world of high-stakes digital finance, the line between a security breach and a geopolitical statement is increasingly thin.