TeamPCP Escalates Cloud-Native Cyberattacks with Targeted Data-Wiping Campaign Against Iranian Infrastructure
A sophisticated cybercriminal syndicate, identified as TeamPCP, has pivoted from traditional financial extortion to high-impact disruptive operations, deploying a self-propagating worm designed to permanently erase data on systems located within Iran. This escalation marks a significant shift in the group’s tactics, transitioning from a focus on data theft and credential harvesting to the deployment of "wiper" malware that triggers based on a system’s geographic and linguistic settings. Security researchers tracking the group indicate that the campaign, which intensified over the third weekend of March 2026, leverages a cloud-native infrastructure to automate the destruction of corporate data across poorly secured cloud environments.
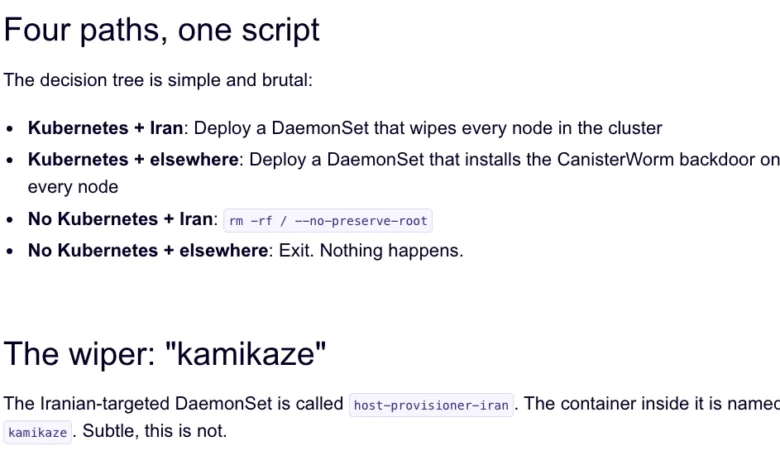
The group’s latest weapon, dubbed "CanisterWorm" by researchers at the security firm Aikido, specifically targets systems that utilize Iran’s timezone or have Farsi configured as the default language. The malware is designed to be highly efficient; if it detects it is running within a Kubernetes cluster, it attempts to move laterally to destroy data on every node within that cluster. On standalone systems, it performs a local wipe of all accessible data. This targeted approach suggests a deliberate attempt by the group to insert itself into the regional tensions surrounding Iran, though researchers remain divided on whether the group’s motivations are political or a pursuit of notoriety through what has been described as "chaotic evil" behavior.
The Technical Architecture of CanisterWorm
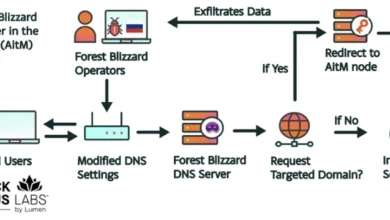
The operational core of TeamPCP’s current campaign relies on the Internet Computer Protocol (ICP). By utilizing ICP "canisters"—decentralized, blockchain-based smart contracts—the group has created a resilient and tamperproof command-and-control (C2) architecture. Because these canisters are distributed across a global network of nodes, they are exceptionally difficult for traditional cybersecurity agencies or internet service providers to take down. As long as the operators continue to fund the canisters with the required virtual currency, the malicious code remains accessible and functional, serving as a persistent source for malware downloads and data exfiltration.
Technical analysis from Aikido researcher Charlie Eriksen reveals that the wiper component is just one facet of a broader, more volatile payload. During periods when the wiper is not active, the group has been observed replacing the malicious code with benign content, such as links to "Rick Roll" videos on YouTube, or rapidly updating the malware with new credential-stealing features. This erratic behavior complicates the efforts of incident responders, as the nature of the threat can change within hours.
The Rise of TeamPCP: From Extortion to Industrialized Exploitation
While the Iranian wiper campaign is a recent development, TeamPCP has been an active threat since at least December 2025. The group initially gained notoriety for its "industrialized" approach to cloud-native exploitation. Unlike elite state-sponsored actors who rely on zero-day vulnerabilities, TeamPCP specializes in the large-scale automation of well-known attack vectors. Their primary targets are exposed control planes rather than individual end-user devices.
According to a profile published by the security firm Flare in January, TeamPCP’s methodology focuses heavily on misconfigured cloud infrastructure. Their statistics show a clear preference for major cloud providers, with Microsoft Azure accounting for 61% of compromised servers and Amazon Web Services (AWS) making up 36%. By targeting exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability, the group has successfully turned exposed infrastructure into a self-propagating criminal ecosystem.
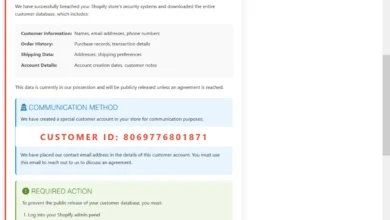
Assaf Morag, a researcher at Flare, noted that the group’s strength lies in its ability to recycle existing tools and vulnerabilities into a streamlined exploitation platform. This "cloud-native ransomware" model allows them to siphon authentication credentials and sensitive corporate data at a scale that traditional manual hacking cannot match. Recent claims by the group on Telegram suggest they have successfully exfiltrated vast amounts of data from major global entities, including a prominent multinational pharmaceutical corporation.
Supply Chain Compromises: The Trivy and KICS Incidents
The most alarming aspect of TeamPCP’s recent activity is its successful infiltration of the software supply chain. On March 19, the group executed a supply chain attack against Trivy, a widely used vulnerability scanner developed by Aqua Security. By compromising official releases on GitHub Actions, the attackers were able to inject credential-stealing malware into a tool that is specifically designed to enhance security.
According to reports from Wiz, the malicious versions of Trivy were capable of "snarfing" a wide array of sensitive information, including:

- SSH keys and cloud provider credentials.
- Kubernetes authentication tokens.
- Cryptocurrency wallet files.
- GitHub access tokens.
Although Aqua Security moved quickly to remove the tainted files, the breach demonstrated the group’s ability to compromise high-trust environments. This was followed by a second supply chain attack on March 23, targeting the KICS (Keeping Infrastructure as Code Secure) vulnerability scanner from Checkmarx. Wiz reported that the KICS GitHub Action was compromised for several hours, during which time it distributed malware similar to that found in the Trivy incident.
These attacks highlight a growing trend of "double-dipping" by threat actors. By gaining access to a developer’s environment once, TeamPCP was able to leverage that access to perpetrate subsequent attacks. Security experts believe the group used credentials stolen during their initial breach of Aqua Security to facilitate the later deployment of the Iranian wiper payload.
Chronology of Recent TeamPCP Activity
The rapid pace of TeamPCP’s operations can be traced through a series of escalating events over the past several months:
- December 2025: TeamPCP begins mass-exploitation of exposed Docker and Kubernetes environments, using a self-propagating worm to build a network of compromised cloud servers.
- January 2026: Flare publishes a comprehensive profile of the group, identifying their focus on Azure and AWS and their use of automated "industrialized" hacking techniques.
- February 2026: The Trivy scanner is hit by a separate automated threat known as HackerBot-Claw. While not directly linked to TeamPCP, this event signaled the vulnerability of the tool’s GitHub workflow.
- March 19, 2026: TeamPCP successfully compromises the Trivy GitHub repository, injecting credential-stealing malware into official releases.
- March 21-22, 2026: The group pivots to a disruptive campaign, leveraging its established infrastructure to deploy the CanisterWorm wiper against Iranian-configured systems.
- March 23, 2026: A new supply chain compromise is detected in the KICS vulnerability scanner by Checkmarx. The malicious payload is active for approximately four hours before being mitigated.
Industry Responses and the GitHub Security Challenge
The repeated success of TeamPCP in compromising GitHub-hosted projects has sparked a broader debate about the security of the software development lifecycle. Catalin Cimpanu, a reporter for Risky Business, recently highlighted that GitHub is facing an increasingly severe malware problem. Attackers are now using sophisticated methods to keep their malicious packages visible, such as pushing meaningless commits to boost repository activity or purchasing "stars" and "likes" to manipulate search rankings.
The nature of GitHub—a platform designed for forking and cloning code—presents a unique engineering challenge. Distinguishing between a legitimate fork and a malicious clone that has been subtly altered is difficult for automated systems. Security experts argue that while firms like Wiz, Aikido, and Flare are doing essential work in identifying these threats, the platform providers themselves must implement more robust safeguards to prevent the weaponization of GitHub Actions.
Aqua Security and Checkmarx have both released statements confirming the removal of the malicious code and advising users to audit their environments for unauthorized credential usage. However, the transient nature of TeamPCP’s payloads—which appear and disappear rapidly—makes it difficult for organizations to determine with certainty if they were affected during the short windows of compromise.
Implications for Global Cloud Security
The emergence of TeamPCP and the CanisterWorm signals a new era of cloud-native threats where the boundary between financial crime and geopolitical disruption is increasingly blurred. For enterprises, the implications are clear: the security of cloud-native tools and the integrity of the software supply chain can no longer be taken for granted.
The use of data-wiping malware by a group that previously focused on extortion suggests that the "ransomware" landscape is evolving. In some cases, destruction may be used as a "chaotic" distraction or as a way to punish victims who refuse to negotiate. Furthermore, the group’s ability to automate the exploitation of misconfigured cloud services underscores the critical importance of cloud security posture management (CSPM).
As organizations continue to migrate their most sensitive workloads to Kubernetes and Docker environments, they must account for the fact that threat actors are no longer just looking for a way in—they are looking for a way to automate the entire process of discovery, theft, and destruction. The Iranian wiper campaign may be a localized event for now, but the infrastructure and techniques developed by TeamPCP represent a global threat to the stability of cloud-integrated industries.