Unmasking Dort The Investigation into the Operator of the Disruptive Kimwolf Botnet
In the rapidly evolving landscape of cyber warfare, few entities have demonstrated the disruptive potential of the Kimwolf botnet, a massive network of infected devices that has compromised the security of residential, corporate, and government infrastructure. At the center of this digital storm is a persistent and aggressive figure known by the pseudonym "Dort." Investigations into this individual have revealed a complex web of digital footprints connecting a former Minecraft cheater to some of the most sophisticated cybercriminal activities of the mid-2020s. Following the exposure of Kimwolf’s operational mechanics in early 2026, Dort launched a coordinated campaign of harassment, including distributed denial-of-service (DDoS) attacks, doxing, and life-threatening "swatting" incidents against security researchers. This report details the identification of the individual behind the handle and the broader implications of his transition from juvenile gaming exploits to high-stakes cybercrime.
The Genesis and Mechanics of the Kimwolf Botnet
The Kimwolf botnet emerged as a significant threat in late 2025 and reached a peak of disruption in January 2026. Unlike traditional botnets that primarily target servers or personal computers through phishing, Kimwolf utilized a more insidious vector: the exploitation of vulnerabilities within residential proxy services. These services allow users to route their internet traffic through residential IP addresses to bypass regional restrictions or maintain anonymity. However, researcher Benjamin Brundage, founder of the proxy tracking service Synthient, discovered that Kimwolf’s operators were exploiting a specific weakness in how these proxy providers managed internal network access.
By hijacking the connections of proxy endpoints, the botmasters gained a foothold inside the private, internal networks of unsuspecting users. From there, they could scan for and infect poorly defended "Internet of Things" (IoT) devices, such as smart TV boxes, digital photo frames, and home automation hubs. Because these devices are located behind firewalls on "trusted" local networks, they are rarely patched or monitored for malicious activity. This strategy allowed Kimwolf to grow into one of the world’s largest botnets, capable of launching massive DDoS attacks that could swamp even the most resilient anonymity networks, such as I2P.
The Digital Paper Trail: From Dortware to Cybercrime
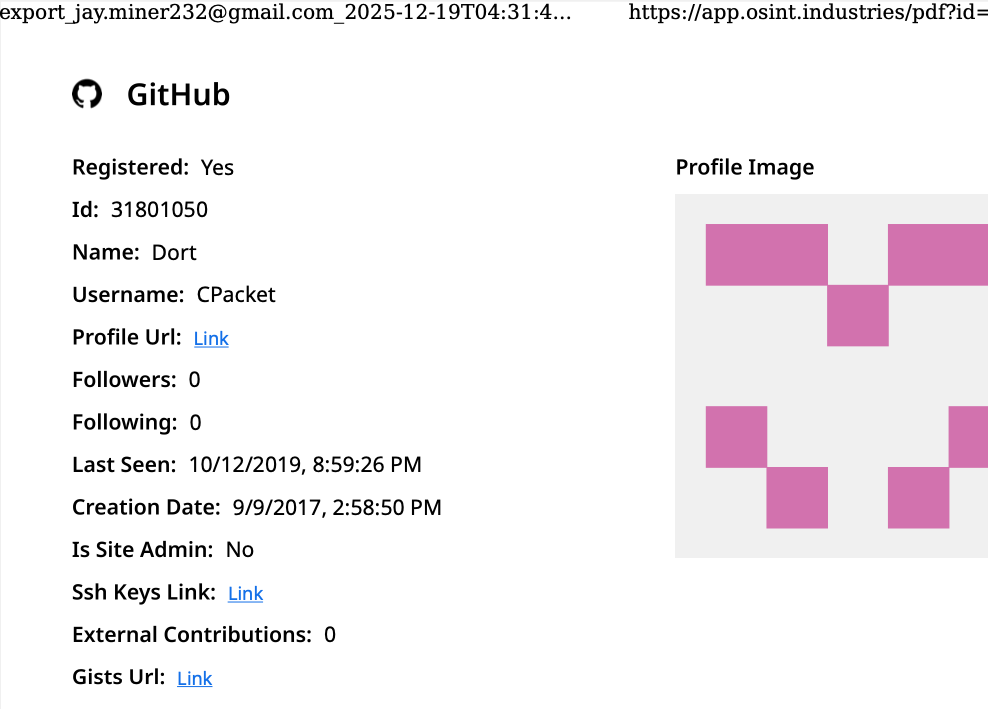
The investigation into Dort began with a "dox" published in 2020, which alleged that the user was a Canadian teenager born in August 2003. According to this early profile, Dort operated under several aliases, including "CPacket" and "M1ce." Utilizing modern open-source intelligence (OSINT) tools, investigators have been able to verify many of these claims. A search on OSINT Industries linked the username CPacket to a GitHub account created in 2017 under the names Dort and CPacket. The account was registered with the email address [email protected].
Further data from cyber intelligence firm Intel 471 reveals that this email address was prolific across various cybercrime forums between 2015 and 2019. It was used to register accounts on Nulled under the handle "Uubuntuu" and on Cracked under the name "Dorted." Crucially, forensic analysis of the metadata associated with these accounts showed they were accessed from a Rogers Canada IP address (99.241.112.24) based in the Ottawa region.
Dort’s initial notoriety did not stem from botnets, but from the popular sandbox game Minecraft. He developed and distributed "Dortware," a suite of software designed to help players cheat. While Minecraft cheating is often dismissed as a juvenile pursuit, it frequently serves as a "gateway" for young hackers to learn the fundamentals of code obfuscation, network exploitation, and community management in illicit forums. For Dort, the transition from manipulating game mechanics to enabling serious financial crimes occurred around 2021 and 2022.
Escalation into SIM-Swapping and LAPSUS$ Activities
By early 2022, the individual behind the Dort identity had expanded his repertoire. Under the moniker "DortDev," he became an active participant in the chat servers of LAPSUS$, a high-profile cybercrime syndicate responsible for breaching major corporations like Nvidia, Samsung, and Microsoft. During this period, Dort marketed several specialized services designed to facilitate automated account abuse.
One such offering was "Dortsolver," a tool designed to bypass CAPTCHA services that protect websites from bot-driven attacks. He also operated a service for registering disposable email addresses. These tools were advertised on "SIM Land," a Telegram channel primarily used by criminals engaged in SIM-swapping—a technique where a target’s phone number is hijacked to bypass two-factor authentication and seize control of financial and social media accounts.
Records indexed by Flashpoint indicate that Dort collaborated closely with another hacker known as "Qoft." In intercepted communications from 2022, Qoft identified Dort as his exclusive business partner, referring to him by the name "Jacob." Qoft boasted that the duo had generated more than $250,000 in illicit revenue by using stolen payment card data to mass-create Microsoft Xbox Game Pass accounts, which were then resold on the black market.
Identifying Jacob Butler: The Ottawa Connection
The link between the pseudonym "Dort" and the real-world identity of Jacob Butler was solidified through credential reuse and domain registration data. Breach tracking services, including Constella Intelligence, found that the password used for the [email protected] account was shared by only one other address: [email protected]. The "803" in the address aligns with the August 2003 birthdate identified in the original 2020 dox.
Historical WHOIS data from DomainTools shows that in 2015, the jacobbutler803 address was used to register several Minecraft-related domains. These registrations were filed under the name Jacob Butler with an address in Ottawa, Canada, and a local 613-area-code phone number. Additional pivots in the data revealed a school-issued email address, [email protected], belonging to the Ottawa-Carleton District School Board, further anchoring the suspect to the Canadian capital.
Retaliation and the Violent Reality of Swatting
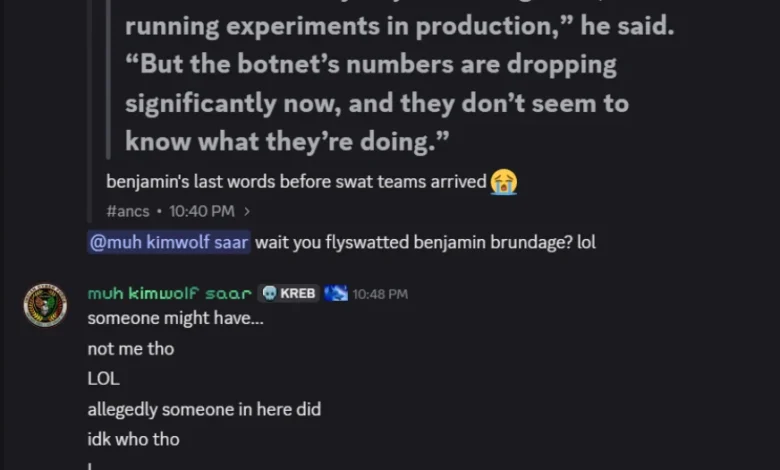
The exposure of the Kimwolf botnet’s vulnerabilities by Benjamin Brundage in January 2026 sparked a violent reaction from Dort. Within hours of the publication of the research, a Discord server was created in the name of the reporting journalist to coordinate attacks. The server, which at various points was named "Krebs’s Koinbase Kallers," became a hub for doxing the researchers and issuing threats.
In February 2026, the situation escalated from digital harassment to physical danger. Dort and his associates orchestrated a "swatting" attack against Brundage. Swatting involves making a fraudulent emergency call to police—often reporting a hostage situation or a violent crime—to trigger a high-risk response from a SWAT team at a victim’s residence. Brundage confirmed that local police arrived at his home in response to a hoax call, an event that coincided with Dort posting taunting messages and a door emoji on the Discord server.
Adding to the evidence of his involvement, Dort released a "diss track" on SoundCloud under the name DortDev. The recording contained explicit threats against Brundage’s life and mocked the damage caused to his home during the swatting incident. The lyrics specifically referenced the cost of a new front door and suggested the victim might be killed by responding officers.
The Defense: Claims of Impersonation and Voice Cloning
When confronted with this evidence, Jacob Butler provided a defense centered on a claim of total withdrawal from the internet. In a brief telephone conversation, Butler acknowledged his past as a Minecraft cheat developer but claimed he had "walked away from everything" in 2021 after his own home was allegedly swatted. He asserted that he suffers from autism and social anxiety, spending his time assisting his mother rather than engaging in cybercrime.
Butler maintained that his old accounts had been compromised and that an unknown party was impersonating him to frame him for the Kimwolf activities. He even addressed the existence of a 2022 "Clash of Code" video where a user named Dort can be heard threatening to swat an opponent. Butler claimed the voice in the video—which closely matches his own—was a "cloned" or "voice-changed" imitation designed to discredit him.
However, cybersecurity experts and investigators find this timeline difficult to reconcile with the technical evidence. The persistent reuse of passwords, the continuity of aliases across different platforms, and the specific timing of the retaliatory attacks suggest a single, motivated individual rather than a multi-year impersonation campaign.
Broader Implications and Federal Intervention
The case of Dort and the Kimwolf botnet highlights a disturbing trend in the cybercrime underground: the radicalization of young hackers who move from low-level gaming cheats to life-threatening physical harassment. The use of IoT botnets to disrupt national infrastructure has prompted a significant response from federal authorities. In March 2026, the U.S. Department of Justice and the FBI announced a major disruption of the IoT botnets behind these DDoS attacks, signaling that the era of impunity for botnet operators may be coming to an end.
The investigation into Jacob Butler serves as a stark reminder of the "digital exhaust" left behind by cybercriminals. Even as they attempt to hide behind aliases and claims of impersonation, the interconnected nature of the modern internet—from school board emails to gaming forums—provides a roadmap for investigators. As legal proceedings and international cooperation continue, the focus remains on holding those who weaponize the internet accountable for both their digital disruptions and their real-world violence.





