German Authorities Unmask Leader of Infamous REvil and GandCrab Ransomware Cartels

German law enforcement authorities have officially identified the individual allegedly behind two of the most prolific and damaging ransomware operations in cybercrime history. In a detailed advisory released by the Bundeskriminalamt (BKA), the German Federal Criminal Police, 31-year-old Russian national Daniil Maksimovich Shchukin was named as the high-ranking cybercriminal who operated under the pseudonym "UNKN" or "UNKNOWN." Shchukin is accused of spearheading the GandCrab and REvil ransomware-as-a-service (RaaS) organizations, which collectively extorted billions of dollars from victims worldwide and pioneered aggressive new tactics in digital extortion.
According to the BKA, Shchukin, alongside 43-year-old associate Anatoly Sergeevitsch Kravchuk, orchestrated at least 130 acts of computer sabotage and extortion against German entities between 2019 and 2021. While the direct extortion amounts cited in German cases total approximately 2 million euros across two dozen specific attacks, the BKA estimates the total economic damage caused by these disruptions exceeds 35 million euros. The identification of Shchukin represents a significant breakthrough for international law enforcement, putting a face to a figure who once boasted of his untouchability within the Russian Federation.
The Architecture of Modern Extortion: GandCrab and REvil
The investigation into Shchukin provides a window into the evolution of the ransomware economy. Shchukin is credited with managing GandCrab, a ransomware strain that first emerged in January 2018. GandCrab was revolutionary not just for its technical sophistication, but for its business model. It operated as a "Ransomware-as-a-Service" platform, where Shchukin’s core team maintained the malware and payment infrastructure while "affiliates" handled the actual breaching of corporate networks.
GandCrab’s curators were known for their rapid development cycles, releasing five major versions of the code in less than two years. Each iteration included bug fixes and advanced features designed to bypass the latest security software and thwart the efforts of "The Ransomware Hunting Team"—a global coalition of security researchers and white-hat hackers. By May 2019, the GandCrab team announced its retirement in a brazen farewell post on a Russian cybercrime forum, claiming they had extorted more than $2 billion and were retiring to a life of luxury.
However, the retirement proved to be a strategic rebranding. Shortly after GandCrab’s departure, a new group called REvil (also known as Sodinokibi) appeared. The group was fronted by a user named "UNKNOWN," who established credibility by depositing $1 million in Bitcoin into a forum’s escrow account. Cybersecurity analysts quickly noted technical overlaps between the GandCrab and REvil codebases, concluding that REvil was the successor organization, led by the same core group under Shchukin’s direction.
The Double Extortion Model and Big Game Hunting
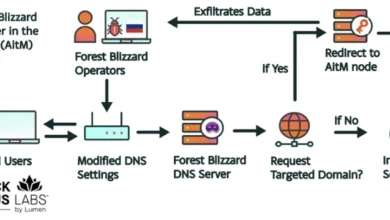
Under Shchukin’s leadership, REvil pioneered the "double extortion" technique, a tactic that fundamentally changed the risk profile for targeted organizations. In traditional ransomware attacks, hackers simply encrypted a victim’s data and sold the decryption key. Shchukin’s groups added a second layer: before encrypting the files, they would exfiltrate sensitive internal documents. If a victim refused to pay for the decryption key—perhaps because they had reliable backups—the group would threaten to leak the stolen data on their "Happy Blog" leak site unless a second "privacy" ransom was paid.
REvil also shifted the focus of cybercrime toward "Big Game Hunting." Rather than targeting individual home users for small sums, the group focused on massive corporations, government agencies, and managed service providers (MSPs) with annual revenues exceeding $100 million. They specifically targeted companies with comprehensive cyber insurance policies, knowing that insurers were often more likely to authorize large payments to facilitate a quick recovery.
This strategy led to some of the most high-profile cyberattacks in history, including the 2021 attack on JBS, the world’s largest meat processor, and the massive supply chain attack on Kaseya. The Kaseya incident, occurring over the July 4 holiday weekend in the United States, affected more than 1,500 downstream businesses and organizations, demonstrating the terrifying scale at which Shchukin’s organization could operate.
Financial Seizures and the Paper Trail
While Shchukin remained elusive for years, a paper trail of digital transactions eventually began to catch up with him. In February 2023, the U.S. Department of Justice filed a seizure warrant for various cryptocurrency accounts linked to the proceeds of REvil attacks. Court documents associated with this filing identified a digital wallet belonging to Shchukin that contained over $317,000 in illicitly obtained cryptocurrency.

The financial investigation revealed how the ransomware ecosystem mirrored legitimate corporate structures. As noted in the investigative work of Renee Dudley and Daniel Golden, ransomware developers like Shchukin reinvested their earnings into specialized services. They hired "initial access brokers" to find vulnerabilities in target networks, "cryptor" providers to ensure their malware remained undetected by antivirus software, and "tumblers" to launder their Bitcoin and Monero payments. This professionalization allowed REvil to operate with the efficiency of a Fortune 500 company, albeit one dedicated to criminal enterprise.
Investigating the Identity: From Ger0in to Krasnodar
The BKA’s identification of Shchukin was the result of years of cross-border intelligence sharing and digital forensics. Intelligence reports from firms like Intel 471 indicate that Shchukin’s history in the cyber underground dates back at least to 2010. Under the alias "Ger0in," a younger Shchukin was allegedly involved in operating large-scale botnets and selling "installs"—a service that allowed other criminals to pay for the automatic installation of malware on thousands of compromised computers.
The transition from a botnet operator to a ransomware kingpin suggests a long-term evolution in technical skill and organizational ambition. Despite his attempts at anonymity, Shchukin’s personal life eventually provided the clues needed for a positive identification. Open-source intelligence (OSINT) researchers, following leads from the BKA, discovered social media evidence from a birthday celebration in Krasnodar, Russia, in 2023. Images from the event showed a man identified as "Daniel" wearing an expensive, high-end watch identical to one seen in photos obtained by German investigators during their probe.
The BKA believes Shchukin currently resides in Krasnodar, a city in southern Russia. While Russia does not typically extradite its citizens to Western nations—particularly for cybercrimes that do not target Russian interests—the public naming and shaming of Shchukin significantly restricts his ability to travel. Any entry into a country with an extradition treaty with Germany or the United States would likely result in his immediate arrest.
The Fall of REvil and the FBI’s Counter-Offensive
The downfall of the REvil organization began in earnest following the Kaseya attack. The sheer scale of the disruption forced a massive response from U.S. and international intelligence agencies. It was later revealed that the FBI had successfully infiltrated REvil’s internal servers months before the Kaseya hack. While the bureau could not prevent the attack without compromising their access, they were able to obtain a universal decryption key, which they eventually released to victims, saving hundreds of companies from having to pay ransoms.
The subsequent pressure from the White House on the Kremlin led to a rare moment of cooperation in early 2022, when the Russian Federal Security Service (FSB) conducted raids against several alleged REvil members in Russia. However, in the wake of the invasion of Ukraine and the subsequent breakdown in diplomatic relations between Russia and the West, many of these legal proceedings stalled or were quietly dismissed. The BKA’s decision to name Shchukin now suggests that Western authorities have abandoned hope for Russian cooperation and are instead focusing on public attribution and the freezing of global assets.
Broader Implications for Global Cybersecurity
The unmasking of Daniil Maksimovich Shchukin serves as a stark reminder of the persistent threat posed by state-tolerated cybercrime. The BKA’s report underscores that while individuals like Shchukin may be the architects of the code, the environment in which they operate—protected from extradition and often encouraged by geopolitical tensions—is what allows ransomware to flourish.
For the global business community, the REvil saga has prompted a fundamental shift in defensive strategies. The "double extortion" threat has forced companies to prioritize data encryption at rest and robust egress filtering to prevent data exfiltration. Moreover, the targeting of cyber insurance policies has led to a hardening of the insurance market, with providers now requiring stringent security controls, such as multi-factor authentication (MFA) and regular penetration testing, before issuing coverage.
The BKA’s advisory concludes with a warning that while Shchukin is currently believed to be in Russia, his "travel behavior cannot be ruled out." Law enforcement agencies continue to monitor global transit hubs and financial gateways, hoping that the man who once claimed to be "living proof that you can do evil and get off scot-free" will eventually make a mistake that brings him into a courtroom. Until then, the identification of "UNKNOWN" stands as a testament to the persistence of digital investigators in an era of borderless crime.