Hacking
-
Artificial Intelligence

Amazon Tacks on 3.5% Fuel Surcharge to FBA Seller Fees
Amazon has officially announced the implementation of a new 3.5% "fuel and logistics-related surcharge" for third-party merchants utilizing its Fulfillment…
Read More » -

Absolute Batman #17: "The Seventh Kingdom: Part One" Unleashes Botanical Terror on Gotham
Gotham City finds itself under an unprecedented botanical assault as Dr. Pamela Isley, infamously known as Poison Ivy, has unleashed…
Read More » -
Cybersecurity and Privacy

0ktapus Phishing Campaign Compromises Over 130 Organizations and Thousands of Employee Credentials by Bypassing MFA
The cybersecurity landscape has been significantly altered by a sophisticated and wide-reaching phishing campaign, now known as "0ktapus," which has…
Read More » -
Cybersecurity and Privacy

Critical Systemic Vulnerability in Anthropic Model Context Protocol Exposes Global AI Supply Chain to Remote Code Execution Attacks
Cybersecurity researchers have identified a foundational security flaw within the architecture of the Model Context Protocol (MCP), a standardized framework…
Read More » -
Cybersecurity and Privacy
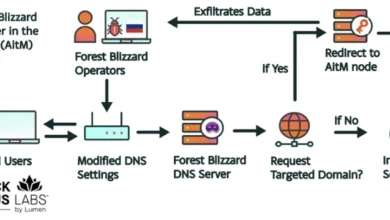
Russian Intelligence Operatives Leverage Global SOHO Router Network to Harvest Microsoft Authentication Tokens at Scale
Cybersecurity researchers have uncovered a massive, state-sponsored espionage campaign orchestrated by Russian military intelligence, which successfully compromised more than 18,000…
Read More » -
Cybersecurity and Privacy

Chinese Cyber-Espionage Group TA423 Targets South China Sea Energy Interests and Australian Entities with ScanBox Reconnaissance Framework
The landscape of international cyber-espionage has witnessed a significant escalation as a China-based threat actor, identified as TA423, has intensified…
Read More » -
Cybersecurity and Privacy

The High Cost of Downtime and the Strategic Necessity of Business Continuity and Disaster Recovery
In the modern digital economy, the infrastructure of commerce is no longer composed solely of brick-and-mortar assets but of interconnected…
Read More » -
Cybersecurity and Privacy
Bridging the Chasm Between AI Prototyping and Enterprise Production in Security and IT Operations
The rapid proliferation of generative artificial intelligence has ushered in a transformative era for enterprise technology, yet a significant disconnect…
Read More » -
Cybersecurity and Privacy
Microsoft Sets Record with 167 Security Fixes in April 2026 Patch Tuesday as AI-Driven Vulnerability Discovery Accelerates
The global cybersecurity landscape reached a significant milestone this month as Microsoft released a record-breaking 167 security updates for its…
Read More » -

Thor Ascends to Leadership: Marvel Studios Crowns God of Thunder as New Avengers Leader in ‘Avengers: Doomsday’ Trailer Reveal
Nearly a decade has passed since the seismic events of Avengers: Endgame fundamentally reshaped the Marvel Cinematic Universe, leaving a…
Read More »
