Cybercriminals Exploit Apple Account Security Notifications to Facilitate Sophisticated Callback Phishing Campaigns

A sophisticated new phishing technique has emerged that weaponizes Apple’s internal account notification systems to deliver fraudulent messages that bypass traditional security filters. By exploiting the automated security alerts generated by Apple’s own servers, threat actors are successfully delivering "callback phishing" lures that appear entirely legitimate to both end-users and automated email verification systems. This method represents a significant evolution in social engineering, as it leverages the inherent trust users place in official communications from major technology providers like Apple to facilitate financial fraud and unauthorized system access.
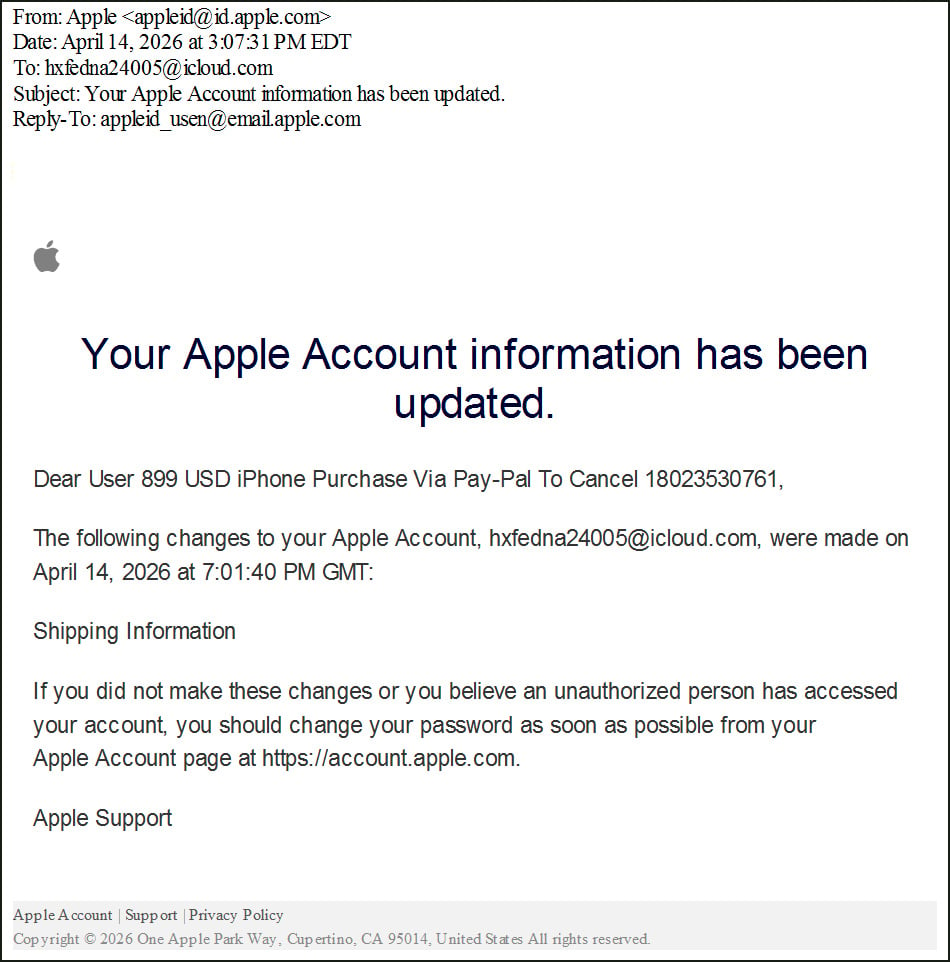
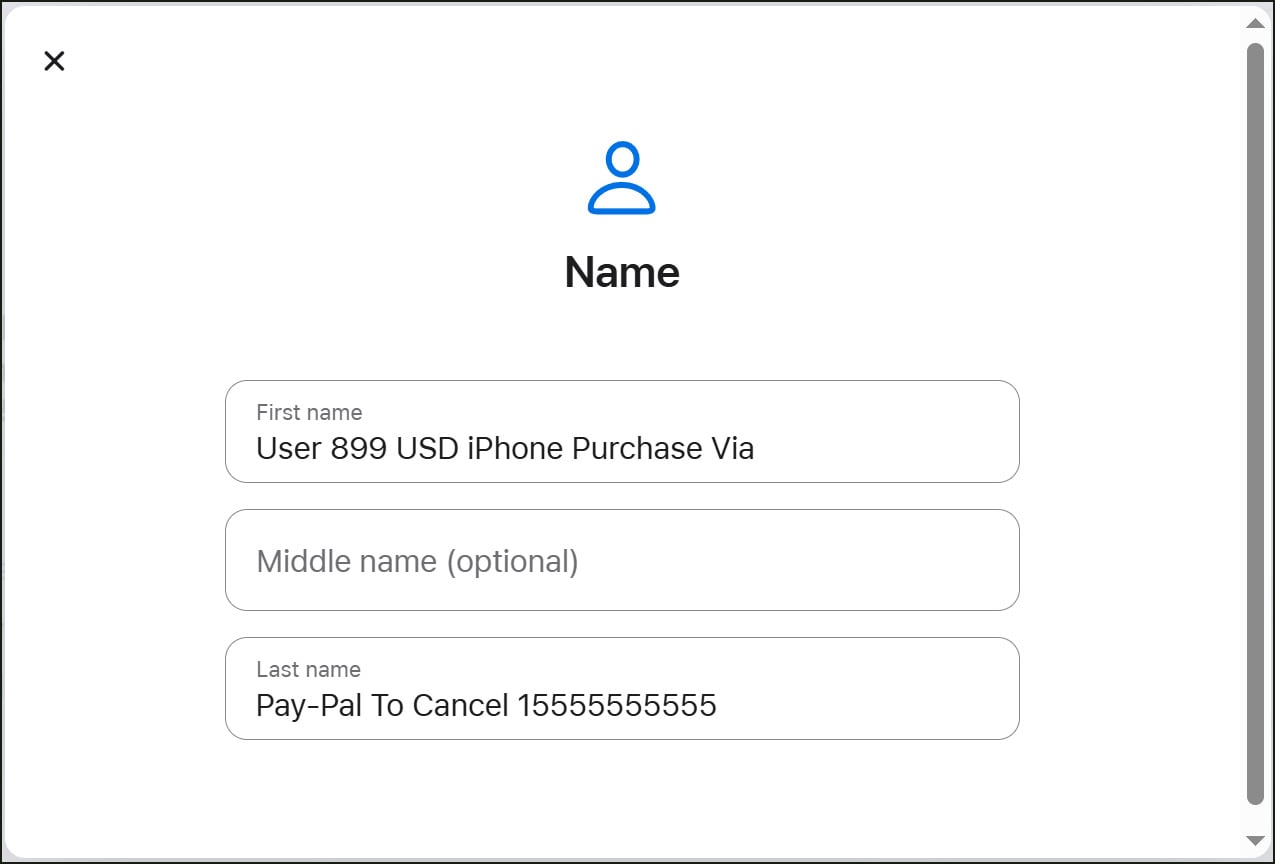
The campaign centers on the abuse of Apple ID account management features. When a user updates critical information on their Apple account—such as their name, password, or shipping details—Apple’s system automatically generates a notification email to alert the account holder of the change. Security researchers have discovered that attackers are creating new Apple IDs and populating the "First Name" and "Last Name" fields with urgent, fraudulent messages. Because these fields are mirrored in the automated notification emails sent by Apple, the phishing lure is embedded directly into a legitimate, digitally signed email originating from Apple’s official servers.
The Mechanics of Infrastructure Abuse
The process begins with the attacker registering a new Apple ID. Rather than using a standard name, the actor inputs a phishing lure into the name fields. For example, the first name field might be populated with "Dear User 899 USD iPhone Purchase," and the last name field might contain "Via Pay-Pal To Cancel Call 1-800-XXX-XXXX." Due to character limits in individual fields, the attackers strategically split the message to ensure it remains coherent when reconstructed by Apple’s automated mailing system.

Once the profile is set up, the attacker triggers an account notification by modifying the shipping address or other account metadata. Apple’s system, programmed to ensure user security, immediately dispatches an email from the address [email protected] to the email address associated with the account. The resulting email informs the recipient that changes have been made to their Apple account, but prominently displays the attacker’s "name"—which is actually the phishing lure—at the top of the message.
The primary objective of this specific campaign is "callback phishing." Unlike traditional phishing that directs users to a fraudulent website via a malicious link, callback phishing encourages the victim to call a phone number. In this instance, the email claims a high-value purchase of $899 has been made via PayPal and provides a fraudulent support number to "cancel" the transaction. This creates a sense of urgency and panic, a hallmark of successful social engineering, prompting the victim to act quickly to protect their finances.
Technical Authentication and the Failure of Traditional Filters
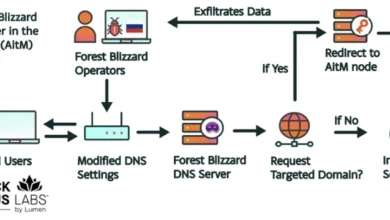
What makes this campaign particularly dangerous is its ability to pass rigorous email authentication checks. Because the email is genuinely generated and sent by Apple’s infrastructure, it carries all the hallmarks of a safe communication. Technical analysis of the email headers reveals that these messages pass Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC) checks.
SPF confirms that the sending server is authorized to send mail on behalf of the domain, while DKIM provides a cryptographic signature that ensures the content has not been tampered with in transit. DMARC ties these two protocols together to provide a comprehensive verification of the sender’s identity. Because the email originates from an Apple-owned IP address (such as 17.111.110.47) and is signed with Apple’s private key, security gateways and spam filters categorize the message as legitimate. This allows the phishing lure to land directly in the victim’s primary inbox rather than being relegated to a spam folder.

Furthermore, header analysis indicates that attackers may be utilizing mailing lists or forwarding rules to distribute these notifications to a wider audience than just the single email associated with the fraudulent Apple ID. This suggests a scalable operation designed to target numerous individuals simultaneously while maintaining the high "reputation" of the sending domain.
The Evolution of Callback Phishing Tactics
The transition toward callback phishing, also known as "BazarCall" or "Luna Moth" style attacks, marks a strategic shift in the threat landscape. By removing the malicious link from the email, attackers eliminate the primary trigger used by Secure Email Gateways (SEGs) to identify phishing. Modern security tools are highly adept at scanning URLs against blacklists or analyzing the code of landing pages for malicious behavior. However, a plain-text phone number within a legitimate email body is much harder to flag as inherently dangerous.
When a victim calls the provided number, they are connected to a fraudulent call center staffed by scammers. These actors typically pose as Apple Support or PayPal billing agents. The interaction usually follows a predictable but effective script:
- Verification: The scammer "confirms" the fraudulent purchase to heighten the victim’s anxiety.
- Remote Access: The victim is told that their device or account has been compromised and that "technical assistance" is required to secure it. They are then instructed to download remote desktop software, such as AnyDesk or TeamViewer.
- Exploitation: Once the scammer gains remote access, they may install malware, steal browser-stored credentials, or initiate unauthorized wire transfers while the victim watches a "blacked-out" screen or is distracted by the caller.
Chronology and Replication of the Threat
The vulnerability was highlighted after security researchers and users reported receiving unusual Apple security alerts in mid-April 2026. BleepingComputer, a cybersecurity news outlet, conducted a controlled replication of the attack to verify the claims. By creating a test Apple account and inserting callback phishing language into the name fields, researchers were able to trigger the exact same notification emails seen in the wild.
The test confirmed that Apple’s system does not currently perform adequate sanitization or pattern matching on the name fields to prevent the inclusion of fraudulent language or phone numbers. This "Living off the Land" (LotL) technique—where attackers use legitimate software and features for malicious purposes—is increasingly common because it requires no specialized malware and leverages the victim’s existing trust in a brand.
This is not the first time Apple’s ecosystem has been abused in this manner. In previous years, threat actors exploited the iCloud Calendar system to send "invites" that contained phishing links. Because the invites were sent through Apple’s notification system, they appeared as system-level pop-ups on iPhones and Macs, making them highly deceptive. The current campaign involving account change notifications is a continuation of this trend, moving from malicious links to the even more persuasive callback model.
Broader Cybersecurity Implications
The abuse of automated notifications poses a significant challenge for the tech industry at large. As companies move toward more automated user-security features, they inadvertently create new surfaces for exploitation. This campaign demonstrates that the "sender" of an email is no longer a sufficient metric for determining its safety. If the content of a verified email is user-generated, that content must be treated with the same level of scrutiny as an unverified external message.
For enterprises, this threat underscores the need for robust security awareness training. Employees must be taught that even an email from a trusted source like apple.com can be weaponized. The presence of a phone number and a request for urgent financial action should be treated as a major red flag, regardless of the sender’s address.
For platform providers like Apple, the implication is a need for stricter input validation. Implementing heuristics that flag name fields containing phrases like "USD," "Purchase," "Cancel," or ten-digit strings resembling phone numbers could significantly mitigate this risk. However, attackers are known for their agility; if Apple blocks specific keywords, scammers will likely pivot to obfuscated text or different fields, such as "Company Name" or "Shipping Instructions."
Protecting Users Against Automated Notification Fraud
As of late April 2026, the ability to exploit these name fields remains active. Users are advised to exercise extreme caution when receiving unexpected security alerts. Security experts recommend the following best practices to defend against this and similar campaigns:
- Verify Independently: If you receive a notification about a purchase or an account change, do not use the contact information provided in the email. Instead, log in to the official website by typing the address directly into your browser or use the official app to check your account status.
- Analyze the Content: Legitimate security alerts from Apple will generally address the user by their actual name on file and will not include urgent demands to call a specific number to cancel a PayPal transaction.
- Beware of Remote Access Requests: No legitimate support representative from Apple or PayPal will ever ask a user to download remote desktop software to process a refund or secure an account.
- Report Abuse: Users who receive these emails should report them to Apple’s security team. This helps the provider refine their filters and potentially block the accounts being used by the attackers.
The persistent evolution of these tactics highlights the ongoing "arms race" between cybercriminals and security teams. While Apple has a reputation for high security standards, the creative abuse of legitimate business logic remains a difficult frontier to defend. As long as automated systems prioritize user-friendliness and immediate notification, threat actors will continue to seek ways to insert themselves into that flow of trust. This campaign serves as a stark reminder that in the digital age, the most dangerous threats often arrive in the most familiar packages.