What is OT security? It’s the crucial protection of industrial control systems (ICS) from cyber threats. Unlike typical IT security, which focuses on data, OT security prioritizes physical and cyber safety, ensuring the reliability of critical processes in sectors like energy, manufacturing, and healthcare. Understanding this difference is key to protecting our increasingly interconnected world.
Operational technology (OT) systems are vulnerable to a range of attacks, from malware to sabotage and even simple human error. This vulnerability highlights the importance of a robust security framework. Protecting these systems is not just about preventing cyberattacks; it’s about maintaining the integrity and reliability of essential infrastructure.
Defining Operational Technology Security (OT Security)
Operational Technology (OT) security is a critical aspect of safeguarding industrial systems and processes in today’s interconnected world. It encompasses the protection of physical and cyber infrastructure, ensuring the reliability and safety of operations within industries like energy, manufacturing, and transportation. This includes not only the digital systems but also the physical processes they control. The implications of a successful attack on OT systems are significant, potentially leading to substantial economic losses, safety hazards, and even societal disruptions.OT security is distinct from Information Technology (IT) security, focusing on the unique needs and challenges of industrial control systems (ICS).
OT security, or Operational Technology security, is crucial for protecting industrial systems. Think about how vital secure systems are for things like the production processes in the tech industry, even the launch of a new smartphone like the Huawei Mate X5 launch. Strong OT security ensures these systems stay operational and safe, preventing vulnerabilities that could have serious consequences.
Protecting these systems is paramount to maintaining a stable and reliable infrastructure.
The traditional focus on data confidentiality, integrity, and availability in IT systems is complemented in OT by a critical concern for physical and cyber safety, process reliability, and operational continuity. This difference demands specialized strategies and tools tailored to the specific nature of OT environments.
Defining Operational Technology (OT)
Operational Technology (OT) encompasses the hardware and software systems that monitor and control physical processes. This includes industrial control systems (ICS), supervisory control and data acquisition (SCADA) systems, and other systems that automate and regulate industrial operations. Examples range from power grids and water treatment facilities to manufacturing plants and oil refineries. These systems often involve complex interactions between sensors, actuators, and controllers, forming a critical infrastructure that underpins many aspects of modern life.
Key Differences Between IT and OT Security
IT security primarily focuses on protecting data and information assets within information systems. OT security, on the other hand, prioritizes the safety and reliability of physical processes and the integrity of industrial control systems. This distinction stems from the fundamental difference in the nature of the assets and the potential consequences of security breaches. OT systems are often directly linked to physical equipment, and disruptions can have immediate and significant consequences.
Types of Operational Technologies and Vulnerabilities
Various types of operational technologies exist, each with its unique vulnerabilities. Supervisory Control and Data Acquisition (SCADA) systems, for example, monitor and control critical infrastructure like power grids and water treatment plants. These systems are often legacy systems with outdated software and limited security measures, making them vulnerable to cyberattacks. Programmable Logic Controllers (PLCs) are used in manufacturing and industrial automation.
These controllers, often embedded in equipment, can be vulnerable to malicious code or manipulation that could lead to production downtime or safety incidents. Similarly, Industrial Internet of Things (IIoT) devices, which connect industrial equipment to the internet, can expose systems to new vulnerabilities as they integrate with wider networks.
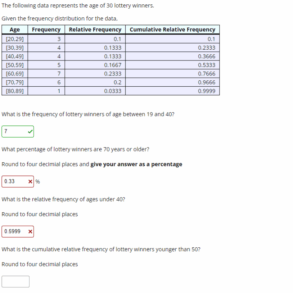
Comparison of IT and OT Security Threats
| Feature | IT Security | OT Security |
|---|---|---|
| Target | Information Systems | Industrial Control Systems |
| Focus | Data confidentiality, integrity, availability | Physical and cyber safety, process reliability |
| Typical Attacks | Malware, phishing, denial-of-service attacks | Cyberattacks, sabotage, human error, equipment failures |
The table highlights the key differences in the targets, focuses, and typical attacks associated with IT and OT security. OT security threats often involve a combination of cyberattacks and physical vulnerabilities, creating a complex security landscape.
Key Components of OT Security
Operational Technology (OT) security is not just about protecting IT systems; it’s about safeguarding the critical infrastructure that powers our world. From power grids to water treatment plants, industrial control systems (ICS) are essential for modern society. Securing these systems requires a multifaceted approach that addresses the unique vulnerabilities of OT environments.A robust OT security framework must go beyond simply installing firewalls.
It needs to encompass a holistic strategy that includes people, processes, and technology. This approach will help prevent costly downtime, data breaches, and potentially catastrophic failures. The goal is to establish a strong defense against threats that can disrupt vital services and cause significant damage.
Security Awareness Training
Security awareness training is crucial for personnel working within OT environments. Employees need to understand the potential risks associated with their daily tasks and how to identify and report suspicious activities. This training should be tailored to the specific roles and responsibilities of each individual, highlighting the importance of following established protocols and reporting any anomalies. Regular updates to the training materials are necessary to keep pace with evolving threats and best practices.
OT security, or Operational Technology security, is crucial for protecting industrial systems. Think about how important it is to safeguard critical infrastructure, like power grids or water treatment plants. Improved notifications in Android P, like those highlighted in android p features youll love improved notifications , demonstrate how software can be more user-friendly and efficient. Ultimately, both OT security and robust software like Android P features are vital for safety and reliability in today’s interconnected world.
Training should cover topics like recognizing phishing attempts, avoiding social engineering tactics, and understanding the proper handling of sensitive information.
Network Segmentation
Network segmentation is a fundamental component of OT security. It involves isolating OT networks from IT networks to limit the potential spread of malicious attacks. This separation creates a barrier, preventing threats from easily traversing between the two networks. This is critical because an attack on an IT network might not have the same impact on an OT network, and vice versa.
The goal is to create independent networks, each with its own security measures, making it harder for attackers to move laterally within the organization’s infrastructure. By implementing proper segmentation, companies can minimize the impact of a breach and ensure the continued operation of critical processes.
OT security, or Operational Technology security, is all about protecting industrial systems. Think about the intricate network of machinery and systems that power our factories, utilities, and transportation. A comparison like the Huawei P20 Pro vs Pixel 2 XL camera comparison in low light huawei p20 pro vs pixel 2 xl camera comparison low light highlights how critical safeguarding these systems is in the digital age.
Ultimately, robust OT security measures are vital to ensure the reliability and safety of our infrastructure and processes.
Access Control
Access control is a vital aspect of securing OT systems. It involves restricting access to OT systems based on the user’s role and responsibilities. This ensures that only authorized personnel can interact with sensitive data and equipment. A robust access control system can identify and verify users, track their actions, and limit their access to only the necessary resources.
Implementing strong passwords, multi-factor authentication, and role-based access control (RBAC) are essential measures to enhance security. This layered approach strengthens the overall defense posture and minimizes the risk of unauthorized access.
Security Information and Event Management (SIEM)
A Security Information and Event Management (SIEM) system plays a critical role in monitoring OT networks for suspicious activity. It collects and analyzes logs from various OT devices, identifying patterns and anomalies that might indicate a security breach. The SIEM system acts as an early warning system, alerting security personnel to potential threats and enabling timely responses. This proactive approach can prevent significant damage and minimize disruption to operations.
Physical Security
Physical security is often overlooked but plays a vital role in OT security. Protecting physical access to critical equipment and infrastructure is just as important as protecting digital access. This includes measures such as access control systems, surveillance cameras, and security personnel to monitor and prevent unauthorized entry. Physical security measures are essential to prevent tampering, sabotage, and theft of equipment and data.
Incident Response Plan
An incident response plan is a critical component for handling security breaches or incidents in OT environments. It Artikels the steps to be taken in the event of a security incident, including containment, eradication, recovery, and lessons learned. This plan ensures a coordinated and efficient response to any security event, minimizing the impact and damage. A well-defined incident response plan will also help identify vulnerabilities and improve the overall security posture.
| Component | Description | Importance |
|---|---|---|
| Security Awareness Training | Education programs for OT personnel | Reduces human error and improves security culture |
| Network Segmentation | Isolation of OT networks from IT networks | Limits attack spread and contains breaches |
| Access Control | Restricting access to OT systems | Prevents unauthorized access and misuse of resources |
| Security Information and Event Management (SIEM) | Monitoring OT networks for suspicious activity | Enables proactive threat detection and response |
| Physical Security | Protecting physical access to critical equipment | Prevents tampering, sabotage, and theft |
| Incident Response Plan | Artikel steps for handling security incidents | Ensures a coordinated and efficient response |
Threats and Vulnerabilities in OT Systems
Operational Technology (OT) systems, crucial for industrial processes, are increasingly vulnerable to sophisticated attacks. These systems, often controlling critical infrastructure like power grids, water treatment plants, and manufacturing facilities, face unique challenges in terms of security compared to traditional Information Technology (IT) systems. Understanding the specific threats and vulnerabilities is paramount for protecting these vital assets.
Common Threats to OT Systems
OT systems are susceptible to a variety of threats, often stemming from vulnerabilities in their design and implementation. These threats often exploit weaknesses in legacy systems, lack of security awareness, and inadequate security controls. The unique nature of OT environments, including remote locations and specialized equipment, can exacerbate these vulnerabilities.
- Malware: Malicious software specifically designed to disrupt or disable OT systems can have devastating consequences. This can range from simple data breaches to complete system shutdowns, potentially impacting entire facilities or critical infrastructure. Examples include Stuxnet, which targeted Iranian nuclear facilities, and other similar attacks that have shown the destructive potential of OT malware.
- Cyberattacks from Nation-States and Hacktivists: Advanced persistent threats (APTs) from nation-states and hacktivist groups represent a serious concern. These actors often have significant resources and expertise to develop and execute sophisticated attacks, targeting specific vulnerabilities in OT systems.
- Supply Chain Attacks: A growing concern involves malicious actors infiltrating the supply chain of OT equipment or software. Compromised components or software updates can provide unauthorized access and control over the entire system. This is a silent threat that is often undetected until an incident occurs. A key aspect of supply chain security is thorough vetting and verification of all third-party vendors.
- Human Error: Accidental or malicious actions by human operators can also lead to vulnerabilities. This can involve configuration errors, failure to follow security protocols, or even phishing attacks targeting human operators.
Vulnerabilities in OT Protocols and Architectures
OT systems often rely on proprietary protocols and architectures that can introduce unique vulnerabilities. These protocols may lack robust security features compared to modern IT protocols, creating significant security risks. A deep understanding of these specific protocols is crucial for identifying and mitigating potential vulnerabilities.
- Legacy Protocols: Many OT systems rely on older, less secure communication protocols. These protocols may lack encryption or authentication mechanisms, making them susceptible to eavesdropping and unauthorized access. The use of these protocols necessitates the implementation of compensating controls.
- Lack of Security in OT Architectures: Often, OT architectures lack the same level of security as IT architectures. This includes a lack of proper segmentation, limited intrusion detection systems, and a general absence of security awareness in the OT environment. The importance of isolating OT networks from IT networks is crucial.
- Lack of Security Awareness: Operators and personnel involved in OT systems may lack sufficient security awareness training. This can lead to human errors and vulnerabilities that are easily exploited by attackers. Regular security training and awareness programs are essential.
Real-World OT Security Breaches
Several real-world incidents demonstrate the potential impact of OT security breaches. These breaches highlight the need for robust security measures and a proactive approach to protecting OT systems.
- The Colonial Pipeline Attack: This attack, involving ransomware, demonstrated the potential for widespread disruption caused by compromising critical infrastructure. The attack affected fuel delivery across a significant portion of the US East Coast. This event underscored the vulnerability of critical infrastructure to cyberattacks.
- The NotPetya Attack: This attack showcased the devastating potential of malware targeting OT systems. The attack had a significant impact on global supply chains, causing widespread disruptions and financial losses. This incident further emphasized the interconnectedness of systems and the potential for cascading effects.
Potential Threats to Different Types of OT Equipment
Various OT equipment presents different vulnerabilities based on its function and design. Understanding these vulnerabilities is crucial for implementing targeted security measures.
- Industrial Control Systems (ICS): ICS equipment often utilizes proprietary protocols and lacks the security features found in IT systems. This can create opportunities for malicious actors to compromise the system and disrupt operations. Security hardening measures are necessary to reduce this vulnerability.
- Supervisory Control and Data Acquisition (SCADA) Systems: SCADA systems control large-scale processes, making them prime targets for attacks. Their vulnerabilities can lead to widespread disruptions in critical infrastructure, such as power grids and water treatment facilities. Security protocols must be rigorously enforced to address these vulnerabilities.
OT Vulnerabilities Table
| Threat | Description | Impact |
|---|---|---|
| Malware | Malicious software targeting OT systems | Disruption of operations, data breaches, potential physical damage |
| Supply Chain Attacks | Compromising OT systems through third-party vendors | Unauthorized access, system compromise, data breaches |
| Phishing | Tricking users into revealing sensitive information | Data breaches, unauthorized access, system compromise |
| Insider Threats | Malicious or negligent actions by authorized personnel | Unauthorized access, data breaches, system compromise |
| Zero-Day Exploits | Exploiting unknown vulnerabilities | Unpredictable impact, potentially catastrophic system failures |
Security Measures and Best Practices

Securing Operational Technology (OT) systems requires a multifaceted approach that goes beyond traditional IT security measures. OT environments, often critical infrastructure, face unique challenges due to their reliance on physical processes and real-time data exchange. Implementing robust security measures is crucial to prevent costly downtime, data breaches, and potential safety hazards.
Various Security Measures for OT Systems
Protecting OT systems necessitates a layered approach, combining technical, procedural, and physical safeguards. These measures should address vulnerabilities across the entire OT lifecycle, from design and implementation to operation and maintenance. Implementing a robust security posture involves addressing not only the immediate threats but also the potential long-term risks.
- Network Segmentation: Isolating OT networks from IT networks limits the potential impact of breaches. This crucial step helps prevent malicious actors from gaining access to sensitive industrial processes. A segmented network architecture creates multiple security boundaries, reducing the attack surface and containing any potential compromises.
- Access Control and Authentication: Implementing strict access controls and multi-factor authentication is essential to prevent unauthorized access to critical systems. Strong passwords, role-based access, and regular audits are vital for maintaining security. Using unique credentials for OT and IT systems further enhances security and prevents cross-contamination.
- Data Encryption: Encrypting sensitive data both in transit and at rest protects it from unauthorized access. Data encryption is particularly important for protecting industrial control systems (ICS) data and communications.
- Regular Security Audits and Penetration Testing: Periodic security audits and penetration testing identify vulnerabilities and ensure that security controls are functioning as intended. Proactive assessments help in maintaining a robust security posture. This is essential for ICS and OT environments as it helps to identify weaknesses in the security measures in place.
Best Practices for Securing Industrial Control Systems (ICS)
Industrial Control Systems (ICS) are complex and often critical for maintaining essential services. Security best practices for ICS must address the unique characteristics of these systems, including their real-time nature and reliance on specific protocols. Compliance with industry standards is also critical for maintaining operational integrity.
- Security Hardening of ICS Devices: Implementing strong security configurations on ICS devices is critical. This includes disabling unnecessary services, using strong passwords, and applying the latest security patches. Proactive measures like these are essential for preventing potential compromises.
- Security Monitoring and Alerting: Monitoring ICS networks for suspicious activity and implementing robust alerting systems are vital. This allows for quick detection and response to potential threats. Advanced security monitoring solutions can detect anomalies and malicious activity in real time.
- Physical Security Measures: Protecting physical access to ICS equipment is just as important as protecting the digital infrastructure. Implementing physical security measures, such as access controls and surveillance systems, is essential to prevent unauthorized access to sensitive equipment.
Security Protocols and Standards
Adhering to established security protocols and standards is essential for maintaining a consistent and effective security posture. Industry standards, such as ISA/IEC 62443, provide a framework for secure OT systems design, implementation, and operation.
- ISA/IEC 62443 Standards: This international standard provides a comprehensive framework for securing industrial automation and control systems. Adherence to the standards helps ensure a consistent and robust security posture for OT environments.
- NIST Cybersecurity Framework: This framework offers guidance for managing cybersecurity risk across all sectors, including OT environments. It provides a common language and approach for identifying, assessing, and managing cybersecurity risks.
Recommended Security Measures for Different OT Environments
The specific security measures required will vary based on the environment and the criticality of the assets.
| OT Environment | Recommended Security Measures |
|---|---|
| Power Generation | Network segmentation, strong authentication, regular audits, physical security, and compliance with industry standards. |
| Manufacturing | Device hardening, intrusion detection systems, regular patching, security training, and continuous monitoring. |
| Water Treatment | Access controls, data encryption, physical security, redundant systems, and disaster recovery plans. |
Security Tools for OT Environments
A variety of security tools can be employed to enhance OT security. These tools can be categorized into different types, each with specific functions and applications.
- Intrusion Detection/Prevention Systems (IDS/IPS): These tools monitor network traffic for malicious activity and can block or alert on suspicious behavior. IDS/IPS are important for real-time threat detection.
- Security Information and Event Management (SIEM) Systems: These systems collect and analyze security logs from various sources, providing insights into potential threats. SIEM systems help in identifying patterns and potential security incidents.
- Vulnerability Scanners: These tools identify security weaknesses in OT systems, including misconfigurations, outdated software, and unpatched vulnerabilities. Vulnerability scanners are essential for proactive security assessments.
Implementing Robust Security Measures
Implementing a robust security strategy requires a phased approach, beginning with a thorough risk assessment and culminating in ongoing monitoring and maintenance.
- Risk Assessment: Identifying potential threats and vulnerabilities is crucial for prioritizing security measures. A comprehensive risk assessment helps in developing targeted security strategies.
- Phased Implementation: Implementing security measures incrementally, based on risk assessment and criticality, is often more effective than a large-scale deployment. Phased implementation helps in managing the complexity and ensuring successful adoption.
- Continuous Monitoring and Maintenance: Security is an ongoing process, not a one-time event. Regular monitoring, maintenance, and updates are crucial for ensuring the long-term effectiveness of security measures.
OT Security in Different Industries
Operational Technology (OT) security is crucial across diverse industries, each with unique operational needs and vulnerabilities. Understanding these differences is vital for tailoring effective security strategies. Different industries face varying levels of risk and require customized approaches to protect their critical infrastructure and processes.
OT Security Considerations in Energy
Energy companies, particularly those managing power grids, face significant OT security challenges. Ensuring the stability and reliability of power generation and distribution is paramount. Cyberattacks targeting these systems can have devastating consequences, potentially causing widespread outages and economic disruption. Protecting Supervisory Control and Data Acquisition (SCADA) systems and critical infrastructure is paramount.
OT Security Considerations in Manufacturing, What is ot security
Manufacturing facilities heavily rely on OT systems for automation and production processes. Maintaining production efficiency while safeguarding against cyber threats is a key concern. Disruptions to production lines due to cyberattacks can lead to significant financial losses and delays. Securing industrial control systems (ICS) and preventing unauthorized access are critical aspects of OT security in manufacturing.
OT Security Considerations in Healthcare
Healthcare facilities utilize OT systems to control medical devices and equipment. Patient safety is paramount, and OT security breaches can have dire consequences. Malware impacting medical devices can lead to life-threatening situations. Securing these systems to prevent unauthorized access and ensure the integrity of medical equipment is critical. Data protection and patient confidentiality are also vital considerations.
Comparison of OT Security Needs Across Sectors
Different industries exhibit varying OT security requirements. The energy sector, for instance, prioritizes grid stability and resilience to cyberattacks that could disrupt power supply. Manufacturing emphasizes maintaining production efficiency and preventing disruptions to automated processes. In healthcare, patient safety is the top concern, requiring robust security measures to protect medical devices and patient data.
Table Comparing OT Security Requirements
| Industry | Specific Needs | Example Risks |
|---|---|---|
| Manufacturing | Maintaining production efficiency, preventing downtime, and protecting intellectual property. Securing industrial control systems (ICS) is crucial. | Cyberattacks disrupting production lines, sabotage of automated systems, theft of sensitive data related to product design or manufacturing processes. |
| Healthcare | Ensuring patient safety, protecting medical devices, and maintaining data confidentiality. Protecting critical medical equipment and patient records. | Malware impacting medical devices, unauthorized access to patient data, disruptions in critical medical equipment functionality. |
| Energy | Maintaining grid stability, preventing outages, and ensuring reliability of power generation and distribution. Protecting SCADA systems. | Cyberattacks impacting power generation, causing widespread outages, and disrupting essential services. |
OT Security Incident Response
Operational Technology (OT) environments, critical for industrial processes, are increasingly vulnerable to sophisticated cyberattacks. A robust incident response plan is crucial for mitigating the damage and restoring operations quickly. Effective response hinges on preparedness, rapid action, and clear roles and responsibilities.Addressing OT security incidents demands a different approach compared to Information Technology (IT) security. The consequences of a successful attack can be catastrophic, impacting safety, production, and financial stability.
Therefore, a dedicated, well-defined incident response process is essential.
Steps for Responding to OT Security Incidents
A comprehensive incident response process must include a series of defined steps to effectively contain, analyze, and recover from a security breach. This process should be documented and regularly reviewed and updated to ensure its effectiveness.
- Identification: Detecting the incident is paramount. This often involves monitoring security logs, alerts from intrusion detection systems, and observing unusual activity in the OT network. Early detection minimizes potential damage.
- Containment: Immediately isolate the affected system or network segment to prevent the incident from spreading. This may involve shutting down specific equipment or disconnecting it from the network. A clear communication plan is vital for informing all stakeholders of the containment measures.
- Eradication: Removing the threat is critical. This might involve patching vulnerabilities, removing malware, or restoring compromised systems to a known good state. Thorough analysis and understanding of the attack vector are key.
- Recovery: Restoring normal operations is the ultimate goal. This entails bringing back systems to their previous functional state, ensuring data integrity, and validating the restored systems’ functionality. Testing the recovery process is essential to ensure its efficacy.
- Post-incident analysis: Evaluating the incident to identify weaknesses in the security posture and improve future defenses is crucial. Lessons learned from the incident will aid in strengthening the security posture and preventing future breaches.
Importance of Incident Response Planning
Planning is crucial for successful incident response. A well-defined incident response plan provides a structured framework for handling security incidents, ensuring a coordinated and efficient response.
- Pre-emptive Strategy: A well-defined plan helps organizations to anticipate potential threats and develop countermeasures. This proactive approach minimizes the impact of incidents.
- Clear Roles and Responsibilities: A well-structured plan designates roles and responsibilities for each team member, enabling a coordinated response to any incident.
- Improved Efficiency: A plan provides a standardized approach to incident response, which streamlines the process and ensures consistency.
Need for Rapid and Effective Incident Response
In OT environments, the speed of response is critical. Timely containment and resolution of incidents minimizes downtime and reduces potential damage.
- Minimized Downtime: Rapid incident response minimizes disruption to operations, preventing significant losses in production or service.
- Limited Damage: Quick containment of incidents prevents the spread of malicious code or further system compromise.
- Financial Implications: A well-planned response can save significant financial costs associated with downtime, recovery, and legal repercussions.
Procedure for Dealing with Potential Security Incidents in OT Environments
A detailed procedure for handling OT security incidents should be documented and regularly reviewed.
| Step | Action |
|---|---|
| Identification | Monitor logs, alerts, and unusual activities. |
| Containment | Isolate affected systems and networks. |
| Eradication | Remove threats and restore compromised systems. |
| Recovery | Restore normal operations and validate systems. |
| Post-Incident Analysis | Identify weaknesses and improve security. |
Roles and Responsibilities in Handling OT Security Breaches
Clearly defined roles and responsibilities are crucial for effective incident response.
- Security Team: Responsible for incident detection, containment, and eradication.
- Operations Team: Handles recovery and restoration of systems.
- Management: Approves critical decisions and ensures resources are available.
- External Experts: Engage specialized consultants if necessary.
Summary: What Is Ot Security

In conclusion, OT security is vital for safeguarding industrial systems and maintaining critical infrastructure. Understanding the unique challenges and threats faced by OT systems, and implementing robust security measures, is essential for ensuring the safety and reliability of our interconnected world. From security awareness training to network segmentation and access control, a multi-faceted approach is crucial for effectively protecting against evolving threats.