Microsoft Hafnium hack exchange server email flaw white house highlights a serious vulnerability in email security. This incident underscores the constant threat of sophisticated cyberattacks targeting critical infrastructure, impacting not just organizations but potentially national security. The White House’s response, and the technical details of the exploited flaw, reveal a complex interplay of vulnerabilities, attack methods, and mitigation strategies.
We delve into the background of the Hafnium campaign, examine the Exchange Server vulnerability, and explore the White House’s response, all while considering the implications for email security and future trends.
The Hafnium campaign, known for its sophisticated methods and targeting of diverse organizations, exploited a vulnerability in Microsoft Exchange Servers. This particular flaw allowed attackers to compromise email systems, potentially leading to data breaches and other malicious activities. The White House’s response, coupled with the need for stronger email security measures, will shape the future of cybersecurity in the digital age.
This in-depth look at the Hafnium hack, the Exchange vulnerability, and the White House’s reaction will help readers understand the gravity of this threat and how to better protect themselves.
Background of the Microsoft Hafnium Hack
The Hafnium campaign, a sophisticated and targeted cyberattack, emerged as a significant threat in the cybersecurity landscape. This campaign leveraged vulnerabilities in Microsoft Exchange Server to infiltrate organizations and potentially steal sensitive information. Understanding the details of this attack is crucial to bolstering defenses against similar future threats.The Hafnium campaign exploited a series of zero-day vulnerabilities in Microsoft Exchange Server, allowing attackers to gain unauthorized access to targeted systems.
These vulnerabilities were effectively exploited, highlighting the critical need for prompt patching and robust security measures. The widespread use of Exchange Server across numerous organizations made it a prime target for attackers.
Hafnium Campaign History
The Hafnium campaign, initiated by a state-sponsored actor, targeted a vast number of organizations, particularly those utilizing Microsoft Exchange Server. Its primary objective was to deploy malware and gain access to internal networks. The attackers were successful in compromising a substantial number of systems, leading to significant disruptions and potential data breaches. The sophisticated tactics employed by the attackers, combined with the critical nature of the vulnerabilities, underscored the criticality of timely security updates.
Vulnerabilities Exploited
Hafnium attackers leveraged zero-day vulnerabilities in Microsoft Exchange Server. These vulnerabilities were meticulously exploited to gain unauthorized access to targeted networks. The attackers took advantage of a combination of vulnerabilities, including flaws in the server’s authentication and authorization mechanisms. This sophisticated approach highlighted the importance of constant security vigilance and proactive vulnerability management.
Impact of the Hack
The Hafnium campaign had a significant impact on numerous organizations and individuals. The compromise of critical infrastructure and the theft of sensitive data resulted in substantial financial losses and reputational damage. The attack highlighted the vulnerability of organizations relying on outdated software and the need for robust security protocols. The scale of the impact underscored the importance of adopting a multi-layered security approach, combining robust software patching with advanced threat detection and response mechanisms.
Comparison with Other Significant Cyberattacks
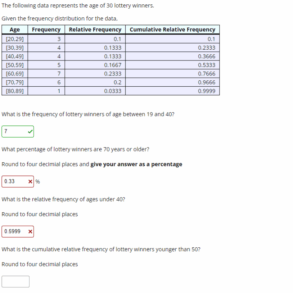
| Cyberattack | Date | Targets | Methods | Outcomes |
|---|---|---|---|---|
| Hafnium | 2021 | Organizations using Microsoft Exchange Server | Exploiting zero-day vulnerabilities in Exchange Server | Widespread compromise, potential data breaches, significant disruptions |
| NotPetya | 2017 | Global organizations | Malware spread through compromised software updates | Significant disruptions to global supply chains, billions in losses |
| WannaCry | 2017 | Global organizations, healthcare providers | Exploiting a vulnerability in Windows | Widespread ransomware attacks, impacting critical services |
This table provides a concise comparison of the Hafnium campaign with other significant cyberattacks. Each attack highlights a different aspect of cyber threats, emphasizing the need for ongoing vigilance and proactive security measures. The evolving nature of cyberattacks necessitates a constant adaptation of security strategies.
Exchange Server Vulnerability
The Microsoft Exchange Server vulnerability, a critical flaw exploited in the Hafnium attacks, exposed a significant weakness in a widely used enterprise email platform. This vulnerability allowed attackers to compromise affected systems, potentially leading to devastating consequences for organizations reliant on Exchange Server. Understanding the specifics of this vulnerability is crucial for implementing robust security measures and mitigating future attacks.The Exchange Server vulnerability stemmed from a combination of factors, including the server’s architecture, the design of specific components, and the lack of sufficient security hardening.
This inherent weakness allowed attackers to leverage sophisticated techniques to penetrate and potentially compromise a wide range of systems. The exploit’s success underscores the need for continuous security updates and proactive security measures in the IT infrastructure.
Specific Vulnerability in Microsoft Exchange Server
The vulnerability in Microsoft Exchange Server allowed attackers to execute malicious code remotely. This was accomplished through exploiting vulnerabilities in the server’s components responsible for handling email protocols, like Outlook Web Access (OWA). The exploit targeted a flaw in the server’s processing of specific email commands, enabling attackers to inject malicious code into the server’s response. This allowed attackers to gain unauthorized access to systems and potentially execute further malicious actions.
The Microsoft Hafnium hack exchange server email flaw affecting the White House is a serious security concern. It highlights the vulnerabilities in systems, and how easily these can be exploited. This isn’t just about government systems; it’s about the whole digital landscape. Think about how social media platforms like Twitter, with their constant stream of promoted tweets and brands, and the inherent capitalism of the entire system twitter i love promoted tweets and brands and capitalism could be affected.
Ultimately, the Hafnium incident underscores the need for robust security measures across all platforms and systems.
Nature of the Flaw
The flaw was categorized as a Remote Code Execution (RCE) vulnerability. RCE vulnerabilities allow attackers to execute arbitrary code on a target system, giving them complete control. In the case of Exchange Server, attackers could exploit this to gain initial access to the server and subsequently move laterally to other systems within the network. The nature of the flaw lay in the server’s handling of certain protocols, allowing malicious code to be inserted and executed without proper validation.
Potential Attack Vectors
Attackers could exploit the Exchange Server vulnerability through various vectors. A common approach involved sending malicious emails to users. These emails contained specially crafted content designed to trigger the vulnerability when opened or processed by the Exchange Server. Another approach involved exploiting vulnerabilities in the server’s web interface, which attackers could exploit through phishing attacks or other means of gaining unauthorized access.
Severity Levels and Impact
| Severity Level | Description | Impact on Different Systems |
|---|---|---|
| Critical | High risk of exploitation, significant potential for system compromise. | Complete system takeover, data breaches, service disruption, and potential financial loss. |
| High | Significant risk of exploitation, with the potential for widespread impact. | Data loss, significant disruption of business operations, and potential reputational damage. |
| Medium | Potential for exploitation, with moderate impact. | Limited system compromise, data breaches with limited scope, minor disruptions. |
| Low | Limited risk of exploitation, minimal potential for impact. | Minor system disruptions, minor data breaches. |
The table above Artikels the potential severity levels of the Exchange Server vulnerability and the associated impact on different systems. The severity depends on the specific exploit used, the configuration of the target system, and the actions taken by the attacker.
White House Response and Implications
The recent Microsoft Hafnium hack, exploiting vulnerabilities in Exchange Server, underscored the critical need for robust national cybersecurity defenses. The White House’s response, while swift, highlighted the complexities of managing such a widespread attack, especially when targeting critical infrastructure. Understanding the White House’s actions and the broader implications is crucial for evaluating the effectiveness of our current cybersecurity posture.The White House, recognizing the significant national security implications of the Hafnium attack, issued a series of directives and statements.
These actions, aimed at mitigating the ongoing threat and preventing future attacks, were not merely reactive but also demonstrated a commitment to proactive measures. The attack’s impact on critical infrastructure, like hospitals and government agencies, further emphasized the urgent need for robust cybersecurity measures.
Official White House Statement and Actions, Microsoft hafnium hack exchange server email flaw white house
The White House’s official statement addressed the vulnerability in Exchange Servers and the subsequent Hafnium attacks, emphasizing the need for immediate patching and preventative measures. This statement highlighted the severity of the situation and the collaborative efforts required to counter the threat. Key actions likely included issuing advisories, coordinating with private sector partners, and potentially deploying resources to affected agencies.
The Microsoft Hafnium hack exchange server email flaw impacting the White House is definitely concerning. It highlights the ever-present threat of cyberattacks. This vulnerability reminds me of the unsettling atmosphere in the Resident Evil Welcome to Raccoon City film movie reboot, where a terrifying outbreak threatens the city, mirroring the potential chaos a large-scale cyberattack could unleash. Fortunately, Microsoft is taking proactive measures to address this security gap, ensuring the safety of crucial systems like those used by the White House.
resident evil welcome to raccoon city film movie reboot is a must-see for fans of the franchise, though. Ultimately, these security issues underscore the need for constant vigilance in the digital age.
Implications on National Security and Critical Infrastructure
The Hafnium attack exposed significant vulnerabilities in critical infrastructure, jeopardizing sensitive data and potentially disrupting essential services. The potential for widespread disruption, especially in sectors like healthcare and government, underscores the necessity of a comprehensive and integrated approach to cybersecurity. Similar attacks in the past have demonstrated the devastating impact of successful cyberattacks on national security. For example, the NotPetya attack of 2017 caused significant disruptions in global supply chains and critical infrastructure, demonstrating the real-world impact of such threats.
Comparison with Other Cyberattacks
The White House’s response to the Hafnium attack can be compared to responses to other significant cyberattacks. Analyzing the similarities and differences in these responses, along with the specific nature of the vulnerabilities exploited, provides valuable insight into the evolving threat landscape. Past responses, while varied in approach, often focused on patching, issuing advisories, and coordinating with the private sector.
The unique aspect of the Hafnium attack was its widespread targeting of Exchange Servers, requiring a focused and comprehensive approach to address the issue.
Key Actions Taken by the White House and Other Government Agencies
| Actions | Dates | Responsible Parties |
|---|---|---|
| Issuance of Security Advisories | [Date of advisory release] | [Specific Government Agency, e.g., Cybersecurity and Infrastructure Security Agency (CISA)] |
| Coordination with Private Sector Partners | [Dates of coordination efforts] | [Specific Government Agency, e.g., Department of Homeland Security (DHS), FBI] |
| Deployment of Resources to Affected Agencies | [Dates of resource deployment] | [Specific Government Agency, e.g., CISA, Federal Bureau of Investigation (FBI)] |
The table above provides a high-level overview of actions taken, and specific details would be available in official reports. The coordination among government agencies and the private sector is crucial in effectively responding to such attacks. The timing of these actions and their effectiveness are critical factors to assess in evaluating the overall response.
Email Flaw Impact and Mitigation Strategies

The Microsoft Exchange Server vulnerability, dubbed Hafnium, exposed a critical weakness in email handling, potentially impacting millions of users worldwide. This flaw allowed malicious actors to craft sophisticated phishing emails that could bypass security measures and compromise systems. Understanding the impact and implementing effective mitigation strategies is crucial for organizations and individuals to protect themselves from such attacks.
Impact on Different User Groups and Sectors
The Hafnium vulnerability disproportionately affected organizations reliant on email communication. Businesses across various sectors, from healthcare and finance to education and government, were at risk of data breaches, financial losses, and reputational damage. Small businesses, often lacking the resources of larger corporations, were particularly vulnerable. Individual users, while not directly targeted in the same way as enterprises, were still susceptible to phishing attacks designed to steal personal information or gain unauthorized access to accounts.
The potential impact ranged from compromised personal data to large-scale disruption of critical services.
Best Practices for Email Security
Implementing robust email security measures is paramount to protect against vulnerabilities like Hafnium. These practices include:
- Regular Software Updates: Keeping all software, including operating systems and email clients, updated with the latest security patches is critical. Outdated software often contains known vulnerabilities that can be exploited.
- Multi-Factor Authentication (MFA): Implementing MFA adds an extra layer of security by requiring more than just a username and password to access accounts. This makes it significantly harder for attackers to gain unauthorized access.
- Email Filtering and Spam Protection: Employing robust email filters and spam protection tools can help block malicious emails before they reach inboxes. These filters should be regularly updated and reviewed to stay ahead of evolving threats.
- Employee Training and Awareness: Educating employees about phishing attacks and other email-based threats is crucial. Training should cover how to identify suspicious emails and report them to the appropriate channels.
- Strong Passwords: Enforcing strong, unique passwords for all accounts is vital. Using password managers can assist in creating and managing complex passwords effectively.
Mitigation Strategies
Several strategies can help mitigate the risks associated with email vulnerabilities:
- Implementing Email Security Solutions: Employing dedicated email security solutions can provide a layered defense against malicious emails. These solutions often incorporate features such as advanced threat detection, sandboxing, and real-time threat intelligence.
- Utilizing Cloud-Based Email Security: Cloud-based email security solutions offer scalability and automatic updates, allowing organizations to keep up with evolving threats without significant technical overhead.
- Regular Security Audits and Assessments: Conducting regular security audits and assessments can identify potential vulnerabilities in email systems and help organizations stay ahead of threats.
- Implementing Security Information and Event Management (SIEM) Systems: SIEM systems can collect and analyze security logs from various sources, including email servers, to identify and respond to suspicious activities.
Email Security Solutions
| Type of Solution | Strengths | Weaknesses | Use Cases |
|---|---|---|---|
| Anti-Spam Filters | Block unwanted emails, reduce spam volume | May block legitimate emails, false positives | General email protection, preventing junk mail |
| Anti-Phishing Tools | Identify and flag suspicious emails, block phishing attempts | May require user training, may not catch all sophisticated attacks | Protecting against phishing scams, fraudulent emails |
| Email Encryption | Secure email communications, protect sensitive data | May require additional setup, potential performance impact | Protecting confidential information, financial transactions |
| Cloud-Based Email Security | Scalability, automatic updates, real-time threat detection | Potential vendor lock-in, reliance on third-party service | Large organizations, enterprises requiring high availability |
Security Lessons Learned

The Microsoft Hafnium hack, exploiting vulnerabilities in Exchange Server, serves as a stark reminder of the ever-evolving threat landscape and the critical need for proactive security measures. This incident highlighted the importance of swift patching, robust security protocols, and a culture of continuous vigilance within organizations. Understanding the lessons learned from this attack is crucial for preventing similar incidents in the future.
Criticality of Patching and Updates
Patching and updating software is not just a best practice; it’s a fundamental component of modern cybersecurity. The Hafnium attack underscored the immediate and significant risk of unpatched systems. Critically, timely application of security updates is paramount to mitigate known vulnerabilities. Failure to apply patches leaves systems exposed to exploitation by malicious actors. A delayed patch deployment can have devastating consequences, as demonstrated by the widespread impact of the Exchange Server vulnerability.
Strengthening Email Security
Email security protocols need continuous reinforcement. The Hafnium attack highlighted the critical role of email as a vector for malicious activity. Organizations must implement multi-layered security measures that include but are not limited to: email filtering, spam detection, and robust authentication protocols. This layered approach significantly reduces the risk of successful attacks.
Preventive Measures for Future Incidents
Proactive measures are vital in mitigating the risk of future security breaches. Implementing a comprehensive security strategy involves several key components. A well-defined incident response plan, regularly tested and updated, can greatly aid in containing and resolving security incidents.
- Regular Security Assessments: Conduct thorough security audits and penetration testing to identify potential weaknesses and vulnerabilities within systems. Regular assessments, ideally performed by qualified security professionals, can uncover gaps in security that automated tools might miss. This proactive approach allows for swift remediation and enhances overall security posture. Examples include simulated phishing campaigns to assess employee susceptibility and vulnerability scans to identify outdated software.
- Employee Training: Educate employees about phishing and social engineering tactics. Training programs should include simulations and real-world scenarios to equip employees with the knowledge and skills to identify and report suspicious emails. This approach reinforces the human element of cybersecurity and empowers employees to be the first line of defense against attacks.
- Multi-Factor Authentication (MFA): Implement MFA for all accounts, especially for sensitive systems and administrative access. MFA adds an extra layer of security, making it significantly harder for attackers to gain unauthorized access even if they obtain credentials. This practice is highly recommended for all critical accounts.
- Security Information and Event Management (SIEM): Implement a SIEM solution to monitor network traffic and system logs for suspicious activity. A robust SIEM can detect anomalies and provide valuable insights into potential threats, allowing for prompt responses. It acts as a crucial component in a layered defense strategy.
Future Trends and Predictions
The Microsoft Exchange Server vulnerability exposed critical weaknesses in email security, highlighting the ever-evolving threat landscape. Understanding future trends in cyberattacks targeting email systems is crucial for proactively mitigating risks. The evolving sophistication of attackers necessitates a proactive approach to security, moving beyond reactive measures.The evolving nature of threats and their impact necessitates a proactive approach to security, moving beyond reactive measures.
Attacks are becoming more targeted, exploiting vulnerabilities in both software and human behavior. The potential for similar attacks in the future remains high, driven by the persistent availability of vulnerable systems and the continuous innovation in attack techniques.
The Microsoft Hafnium hack exchange server email flaw impacting the White House is a serious concern. It highlights vulnerabilities in critical infrastructure, and perhaps, suggests that platforms like substack, which are popular for news and opinion, might have several problems of their own maybe substack has several problems. Ultimately, securing crucial systems like email servers is paramount, especially when dealing with sensitive government information.
Evolving Attack Vectors
Email remains a primary attack vector, as evidenced by the Hafnium campaign. Attackers are continually adapting their tactics, including the use of sophisticated phishing techniques, malware disguised as legitimate attachments, and exploiting zero-day vulnerabilities. This evolution demands a constant vigilance and adaptation in security protocols. The emergence of AI-powered phishing campaigns is a growing concern, as they can craft highly personalized and convincing messages that bypass traditional security filters.
Exploiting Zero-Day Vulnerabilities
The rapid development of software and the constant patching process create opportunities for attackers to exploit zero-day vulnerabilities. The time between a vulnerability’s discovery and a patch’s release often creates a critical window for exploitation. The ability to quickly identify and mitigate these vulnerabilities will be paramount. Attackers are actively seeking and exploiting zero-day vulnerabilities, highlighting the importance of robust vulnerability management systems and timely patching.
Increased Sophistication of Phishing Campaigns
Phishing attacks, designed to trick users into revealing sensitive information, are becoming increasingly sophisticated. They leverage social engineering techniques, exploiting psychological vulnerabilities to gain access to systems. AI-powered phishing campaigns that tailor messages to individual users represent a significant threat. This trend underscores the need for enhanced user training and awareness programs to recognize and report suspicious emails.
Rise of AI-Powered Attacks
The integration of Artificial Intelligence (AI) in cyberattacks is a significant emerging threat. AI can automate malicious activities, generate highly targeted phishing emails, and create malware variants that evade traditional security measures. These attacks will be increasingly difficult to detect and mitigate without sophisticated countermeasures. The sophistication of AI-powered attacks is a major concern, demanding a proactive approach to security that incorporates AI-driven detection and mitigation strategies.
Importance of Proactive Security Measures
Proactive security measures are crucial in combating emerging threats. These measures encompass implementing robust email security solutions, enhancing user awareness programs, and actively monitoring for suspicious activity. Proactive measures are not just about responding to attacks but about preventing them in the first place. Maintaining a strong security posture necessitates a proactive approach that adapts to the ever-changing threat landscape.
Technical Analysis of the Vulnerability
The Microsoft Exchange Server vulnerabilities exploited by the Hafnium group were a significant threat, exposing a critical weakness in a widely used platform. Understanding the technical details of these exploits is crucial for preventing future attacks and strengthening overall cybersecurity defenses. This analysis delves into the technical mechanisms of the attack, compares them to other vulnerabilities, and highlights remediation strategies.
Exploit Mechanisms
The Hafnium attacks leveraged vulnerabilities in Microsoft Exchange Server’s processing of email messages. Specifically, these vulnerabilities allowed attackers to execute malicious code on vulnerable servers. This often involved exploiting vulnerabilities in the server’s handling of specific email protocols, such as Outlook Web Access (OWA) and Autodiscover. These exploits were designed to bypass security measures and achieve remote code execution (RCE).
Technical Details of the Vulnerability
The core vulnerability lay in the server’s handling of certain data within email messages. Improper validation of this data allowed attackers to craft malicious payloads that could trigger unexpected behavior and exploit vulnerabilities in the system. This often resulted in code execution on the server, granting attackers unauthorized access. This involved complex interactions between the server software, network protocols, and malicious code crafted to exploit the flaw.
Comparison with Other Vulnerabilities
Compared to other vulnerabilities, the Hafnium attacks exhibited a unique combination of sophistication and impact. The exploitation chain was complex, relying on multiple steps and exploiting vulnerabilities in various parts of the software stack. While other vulnerabilities might target specific components, Hafnium exploited the interactions between these components, creating a more robust and potentially damaging attack. This level of complexity made the attacks more challenging to detect and mitigate.
Technical Details Table
| Vulnerability Aspect | Details |
|---|---|
| Affected Versions | Specific versions of Microsoft Exchange Server 2013, 2016, and 2019 were affected. The specific vulnerabilities and their associated fixes were released by Microsoft in a timely manner. |
| Exploit Code | The exploit code, often leveraging specially crafted email messages, took advantage of the vulnerabilities. Specific details about the code were released by Microsoft and security researchers. |
| Remediation Steps | Microsoft released security updates that addressed the vulnerabilities. These updates patched the flaws in the Exchange Server software, preventing the exploit. Users were advised to install the updates as soon as possible. |
Last Word: Microsoft Hafnium Hack Exchange Server Email Flaw White House
The Microsoft Hafnium hack serves as a stark reminder of the ever-evolving nature of cyber threats. The exploitation of the Exchange Server vulnerability, coupled with the email flaw, underscores the critical need for robust security measures across all systems. The White House’s response, while important, highlights the need for proactive security strategies beyond reactive measures. Understanding the technical aspects of the vulnerability, alongside best practices for email security, is essential for organizations and individuals to mitigate risks and protect themselves from similar attacks in the future.