HTTP HTTPS insecure connections Chrome Firefox are a critical aspect of online security. Websites using HTTP, the standard protocol for transferring web pages, lack encryption, making your data vulnerable to interception. HTTPS, on the other hand, employs encryption, safeguarding your information. This post dives into the specifics of insecure connections, examining how browsers like Chrome and Firefox handle them and what security implications arise from their use.
Understanding the differences between HTTP and HTTPS is crucial. HTTP operates without encryption, exposing sensitive data like passwords and credit card numbers to potential eavesdroppers. HTTPS, in contrast, employs encryption protocols to protect this data. This article delves into the technical aspects, examining how browsers react to insecure connections, including warnings and default behavior. Furthermore, it explores security implications, common attacks, and methods for mitigating these risks.
Finally, the article concludes with practical advice on how to ensure secure connections and user awareness of these important security considerations.
Understanding Insecure Connections
In today’s digital landscape, secure communication is paramount. Web applications rely on protocols like HTTP and HTTPS to transmit data between clients and servers. However, understanding the vulnerabilities inherent in insecure connections is crucial for ensuring the safety and integrity of sensitive information. This discussion delves into the specifics of insecure connections, highlighting the risks associated with them.Insecure connections, often relying on the HTTP protocol, expose data transmitted between a user’s device and a website to potential interception and manipulation.
This lack of security can compromise user privacy and data integrity, leading to various malicious activities. Understanding the differences between HTTP and HTTPS, and the risks associated with each, is vital for anyone interacting with online services.
Vulnerabilities of HTTP Connections
HTTP, the fundamental protocol for web communication, lacks inherent security mechanisms. This means that data exchanged between a user’s browser and a website, such as login credentials or financial information, travels in plain text, making it susceptible to eavesdropping and tampering. Malicious actors can potentially intercept this data, leading to unauthorized access and data breaches.
Comparison of HTTP and HTTPS
HTTP and HTTPS are both used for transferring data over the internet, but they differ significantly in terms of security. HTTP operates without encryption, exposing sensitive information to potential threats. HTTPS, on the other hand, employs encryption, significantly reducing the risk of data breaches. This crucial difference safeguards user data during transmission.
Risks of Using Insecure Connections
Using insecure connections for web applications exposes users to a variety of risks. For example, sensitive information like passwords, credit card details, and personal data can be intercepted by malicious actors. This can lead to identity theft, financial fraud, and other serious consequences. Furthermore, the lack of encryption can compromise the integrity of data, potentially altering or corrupting information during transmission.
This can result in incorrect data being used for transactions or calculations, causing significant issues for businesses and individuals alike.
Differences Between HTTP and HTTPS
The following table highlights the key differences between HTTP and HTTPS:
| Feature | HTTP | HTTPS |
|---|---|---|
| Security | Insecure | Secure |
| Encryption | No | Yes |
| Data Protection | Vulnerable | Protected |
| URL | http:// | https:// |
| Connection | Unencrypted | Encrypted |
Impact on Browsers
Insecure connections, using HTTP instead of HTTPS, pose a significant risk to user privacy and data security. Browsers play a crucial role in mitigating these risks, providing warnings and implementing measures to protect users from potential threats. This section delves into how browsers handle insecure connections, focusing on the user experience and the security measures employed.Browsers are not passive recipients of web traffic; they actively assess the security of connections and display warnings to users.
This proactive approach is essential for safeguarding users from malicious actors who might exploit insecure connections for phishing, data theft, or other malicious activities. The user experience is directly impacted by these warnings and how browsers handle insecure connections.
User Experience Impact
Users often encounter insecure connections when visiting websites that haven’t implemented HTTPS. This lack of encryption can expose sensitive information, like passwords and credit card details, to eavesdropping by malicious third parties. Browsers provide clear warnings to alert users to the security risks associated with insecure connections.
Browser Handling of Insecure Connections
Browsers like Chrome and Firefox implement various mechanisms to manage insecure connections. These mechanisms range from displaying warnings to blocking or restricting access to insecure content. This proactive approach is crucial in today’s digital landscape where online security is paramount.
Security Warnings for Insecure Sites
Browsers prominently display warnings when users access an insecure site. These warnings typically take the form of visual cues, such as a padlock icon that appears as an unsecure icon, along with a warning message, usually located in the address bar or a prominent location on the webpage. The specific appearance and wording of these warnings may vary between browsers, but the underlying message remains consistent: the connection is not secure.
While secure connections like HTTPS are crucial for browsing, understanding the intricacies of insecure HTTP connections in browsers like Chrome and Firefox is still important. For instance, the FCC’s recent broadcast incentive auction, explained in detail here: fcc broadcast incentive auction explained , highlights the need for robust security measures. Ultimately, ensuring secure connections across the web remains a top priority for web users and developers.
For example, in Chrome, the address bar displays a not secure icon with a warning message like “Not secure.” In Firefox, a similar warning icon with a text message indicating the connection is insecure is shown.
Default Behavior for Handling Mixed Content
Mixed content refers to situations where a website uses both secure (HTTPS) and insecure (HTTP) connections. This can occur when a webpage contains elements like images, scripts, or stylesheets that are loaded over HTTP while the main page is loaded over HTTPS. Browsers typically handle mixed content by displaying warnings and potentially blocking or restricting the loading of insecure elements.
This helps mitigate the risks associated with mixed content, as a single insecure element can expose the entire session to vulnerabilities.
Comparison of Chrome and Firefox Handling
| Feature | Chrome | Firefox |
|---|---|---|
| Mixed Content Warnings | Chrome displays a warning in the address bar, typically with a message indicating the presence of mixed content. The warning usually includes a visual indicator like a small icon next to the address bar. The warning highlights the specific insecure resource causing the issue. | Firefox displays a warning icon and message in the address bar. The message clearly identifies the insecure resource(s) and their location on the page. |
| Default Behavior | Chrome often blocks or restricts the loading of insecure content, depending on the specific context. This typically involves displaying a warning message and allowing users to choose whether to proceed or not. | Firefox similarly displays a warning and allows the user to choose whether to load the insecure resource or not. However, the behavior might differ based on the type of insecure content. |
Security Implications of Insecure Connections
Unencrypted connections, lacking the crucial security layer of HTTPS, expose sensitive data to potential interception and manipulation. This vulnerability is a significant concern for users sharing personal information online, ranging from financial transactions to sensitive medical records. Understanding the security risks associated with insecure connections is paramount to protecting oneself from malicious actors.
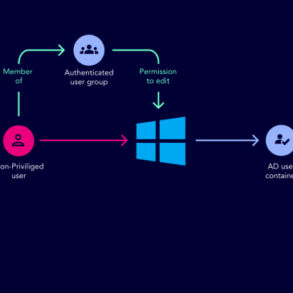
Exploitation Methods
Attackers exploit the lack of encryption on insecure connections by employing various methods. These methods allow them to eavesdrop on communications, intercept data, and modify transmitted information without the user’s knowledge. This is particularly concerning for users sharing sensitive information such as passwords, credit card details, or personal data.
- Man-in-the-Middle Attacks (MITM): An attacker intercepts the communication between the user and the website, allowing them to view, modify, or even completely fabricate the exchanged data. This is a serious threat because the user might be unknowingly communicating with a malicious entity instead of the legitimate website. For example, a user logging into a bank account on an insecure connection might unknowingly be sending their credentials to an attacker posing as the bank.
- Data Interception: Attackers can intercept sensitive data transmitted over insecure connections, such as login credentials, financial information, or personal details. The intercepted data can then be used for various malicious purposes, including identity theft, fraudulent activities, or unauthorized access to accounts.
- Data Modification: Attackers can modify data transmitted over insecure connections, potentially altering the user’s intended actions or input. For example, an attacker might modify an online shopping order to change the shipping address or order different items.
Common Attacks
Several types of attacks exploit the vulnerabilities of insecure connections. These attacks vary in sophistication but share the common thread of compromising the integrity and confidentiality of data exchanged.
- Phishing Attacks: Attackers often leverage insecure connections to create fraudulent websites that mimic legitimate platforms. Users unknowingly input sensitive information on these fake websites, providing attackers with valuable data. This can be particularly effective when the fraudulent site uses an insecure connection, which avoids detection by browsers and potentially the user.
- Session Hijacking: Attackers can gain unauthorized access to user sessions on insecure connections, allowing them to impersonate the user and access protected resources. This can happen through various techniques, such as sniffing network traffic or exploiting vulnerabilities in the web application.
- Malware Infections: Attackers may deploy malware on compromised websites or applications that operate over insecure connections. This malware can then steal data, install additional malicious software, or even take control of the user’s device.
Mitigation Strategies
Implementing measures to mitigate the security risks of insecure connections is crucial. These strategies are essential to safeguard sensitive data and prevent malicious actors from exploiting these vulnerabilities.
While HTTP and HTTPS connections are crucial for secure browsing, it’s still a concern that insecure connections are still an issue in browsers like Chrome and Firefox. Thankfully, recent leaks regarding the Samsung Galaxy S24 FE, like this sneak peek at its potential wardrobe options here , offer a welcome distraction from these security worries. Hopefully, improved security protocols will be prioritized in future browser updates to keep up with the evolving technological landscape.
- Using HTTPS: The use of HTTPS, which encrypts the communication between the user’s browser and the website, is a crucial step to prevent eavesdropping and data manipulation. This is a standard practice that significantly reduces the risk of attacks.
- Strong Passwords: Using strong, unique passwords for online accounts is essential. Strong passwords are complex and difficult to guess, making them more resistant to brute-force attacks. This also helps protect accounts on both secure and insecure connections.
- Software Updates: Regularly updating software and browser applications patches security vulnerabilities, thus preventing exploitation by attackers. Keeping software current is a crucial step in mitigating security risks across all connections.
Attack Process Flowchart
A simplified flowchart depicting the attack process of a Man-in-the-Middle attack targeting an insecure connection is shown below.
Note: This is a simplified representation. Actual attack processes can be far more complex and involve multiple steps.
[Imagine a flowchart here. The flowchart would start with a user accessing a website over an insecure connection. A malicious intermediary would intercept the communication. The attacker would then either modify the data or act as a proxy, sending the data to the intended recipient. The user would remain unaware of the interception.]
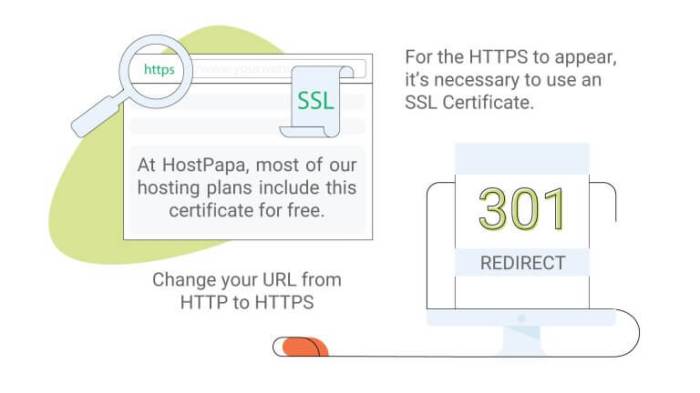
Mitigating Insecure Connections
Protecting your website and user data from cyber threats is paramount in today’s digital landscape. One of the most crucial steps is transitioning to a secure connection, specifically HTTPS. This protocol encrypts communication between the user’s browser and the website, safeguarding sensitive information like passwords and credit card details. HTTPS is no longer a luxury; it’s a necessity.HTTPS, or Hypertext Transfer Protocol Secure, is the secure version of HTTP.
It establishes an encrypted channel between a web server and a client (like a web browser), making it significantly more resistant to eavesdropping and man-in-the-middle attacks. This added layer of security is essential for protecting user data and building trust with your audience.
Securing Connections with HTTPS
HTTPS leverages Transport Layer Security (TLS), a protocol that establishes a secure connection by encrypting data transmitted between a web server and a client. This process involves negotiating a secure session, exchanging cryptographic keys, and authenticating the server’s identity. Crucially, this encryption prevents unauthorized parties from intercepting and modifying data during transmission.
Configuring HTTPS for Websites
Configuring HTTPS involves several steps, from obtaining a digital certificate to properly configuring the web server. A digital certificate, issued by a Certificate Authority (CA), is essential for verifying the website’s identity. This process is crucial to establishing trust and ensuring that users are communicating with the legitimate website.
Configuring HTTPS for Different Web Servers
The process of configuring HTTPS varies slightly depending on the web server used. For example, Apache and Nginx, two popular web servers, have specific configurations for enabling HTTPS. These configurations typically involve enabling the SSL/TLS module, obtaining a certificate, and configuring the server to use it. These configurations are documented on the respective web server’s official documentation.
Examples of HTTPS Configuration
Illustrative examples of HTTPS configuration for different web servers would show how to add the certificate file to the server’s configuration. The configuration directives for Apache and Nginx would differ, reflecting the distinct syntax of each server.
Importance of Strong Encryption Algorithms
Selecting strong encryption algorithms is critical for maintaining the security of HTTPS connections. Modern algorithms, like AES-256, are designed to resist attacks. Choosing weaker algorithms would compromise the security of the connection.
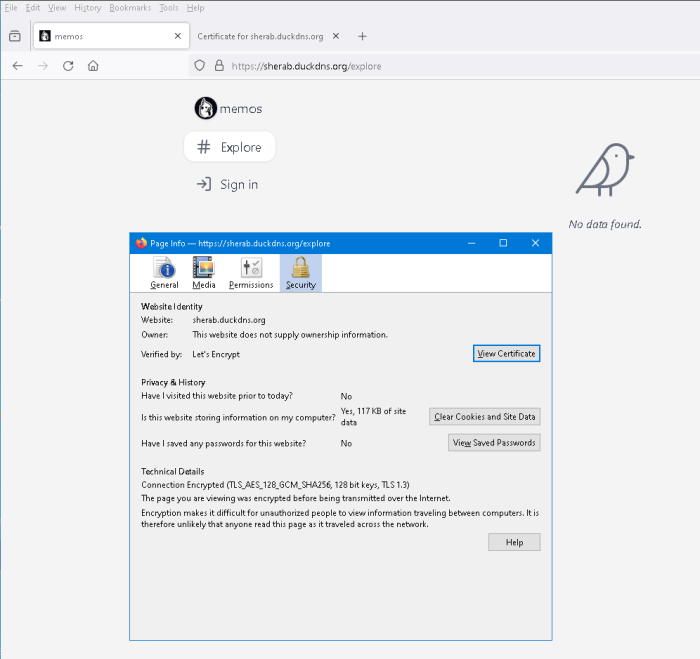
Checking if a Website Uses HTTPS
The simplest way to verify if a website uses HTTPS is to check the URL in your browser. If the URL starts with “https://”, then the connection is secure. The presence of a padlock icon in the browser’s address bar further confirms a secure connection.
Steps to Configure HTTPS on a Web Server
Configuring HTTPS on a web server involves several key steps. These steps are applicable across various web servers, though the specific commands or configuration files may differ.
- Obtain an SSL/TLS certificate from a trusted Certificate Authority (CA). This certificate proves the website’s identity and enables encryption.
- Install the certificate on your web server. This process involves placing the certificate files in the appropriate location on the server.
- Configure your web server to use HTTPS. This involves modifying the server’s configuration files to enable SSL/TLS and specify the location of the certificate.
- Test the HTTPS configuration to ensure that the website loads securely.
User Awareness: Http Https Insecure Connections Chrome Firefox
Knowing the importance of secure connections isn’t just for tech gurus; it’s crucial for everyone online. A secure connection, like a locked door, protects your personal information from prying eyes. This section focuses on how to educate users about these vital security aspects and how to recognize secure connections.
Educating Users About Secure Connections
Understanding the benefits of secure connections is paramount. Users need to know that secure connections, often indicated by “https” in the address bar, encrypt the data exchanged between their devices and websites, safeguarding their sensitive information from unauthorized access. This encryption process protects passwords, credit card details, and other personal data from falling into the wrong hands. Clear and concise explanations, coupled with real-world examples, can significantly improve user awareness.
Ever wondered why HTTP and HTTPS connections matter? Well, a recent Twitter hack exposed 200 million email addresses and usernames, highlighting the critical need for secure connections. This massive breach serves as a stark reminder that insecure HTTP connections can be exploited, leaving personal data vulnerable. Switching to HTTPS for your browsing, especially on Chrome and Firefox, is a crucial step in protecting yourself online.
User Interface Elements for Identifying Secure Connections
Browsers provide clear visual cues to indicate secure connections. A padlock icon in the address bar, typically positioned to the left of the website address, is a common indicator. This icon is a visual signal that the connection is encrypted. Additionally, the address bar itself may display a green or other color-coded indication, further emphasizing the secure connection.
Benefits of Using Secure Connections
Using secure connections provides a multitude of benefits for users. The encryption protects sensitive data from theft, safeguarding personal information. Users can browse and perform transactions with greater confidence, knowing that their data is protected. Websites that offer secure connections build trust with their users, which is essential in the modern digital world. Secure connections prevent unauthorized access, ensuring privacy.
Verifying Secure Connections
Users can verify secure connections by looking at the address bar of their web browser. The presence of “https” in the address bar, along with a padlock icon, confirms a secure connection. Users should also look for a green or colored address bar, as this is another visual indicator. Websites using strong encryption protocols like TLS 1.3 provide an added layer of security.
Furthermore, checking for site seals or certificates can help to confirm the authenticity of the website and the connection.
Understanding HTTP vs. HTTPS: An Infographic
A simple infographic explaining the difference between HTTP and HTTPS can be extremely helpful. The infographic should visually illustrate how HTTP transmits data in plain text, making it vulnerable to interception, while HTTPS uses encryption to protect the data. A clear comparison of the two protocols is key to educating users about the importance of secure connections.
| Feature | HTTP | HTTPS |
|---|---|---|
| Data Transmission | Plain text | Encrypted |
| Security | Vulnerable to interception | Secure |
| Privacy | Data exposed | Data protected |
| Example | Sending a message without a lock | Sending a message with a lock |
Technical Depth
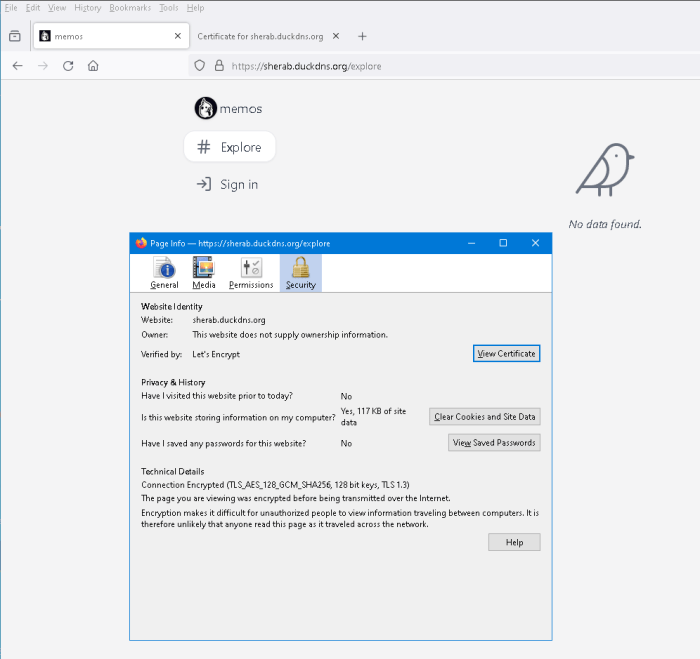
Secure connections rely on robust encryption protocols like TLS/SSL. These protocols safeguard sensitive data exchanged between users and websites. Understanding the technical intricacies of these protocols is crucial for appreciating the importance of secure connections and their impact on the digital landscape. This section delves into the technical details of TLS/SSL, exploring certificates, authorities, validation, and different versions.
TLS/SSL Encryption Details, Http https insecure connections chrome firefox
TLS/SSL, or Transport Layer Security/Secure Sockets Layer, establishes a secure channel over a network. This channel encrypts communication between a client (e.g., a web browser) and a server (e.g., a website). The encryption process uses complex mathematical algorithms to scramble data, making it unreadable to unauthorized parties. This ensures the confidentiality and integrity of the data transmitted.
Role of Certificates in Secure Connections
Digital certificates are fundamental to secure connections. They act as digital IDs, verifying the authenticity of a website or server. These certificates contain the server’s public key, along with other identifying information. When a user connects to a website, the browser verifies the certificate to ensure it’s legitimate.
Examples of Certificate Authorities
Certificate authorities (CAs) are trusted entities that issue and manage digital certificates. They play a critical role in the security of online transactions. Examples of well-known CAs include DigiCert, Symantec (now a part of DigiCert), and GlobalSign. These organizations maintain a hierarchical structure of trust, validating the identities of websites and servers.
Importance of Certificate Validation
Certificate validation is a critical step in ensuring secure connections. A browser checks the certificate’s validity against the CA’s records to ensure the certificate hasn’t been compromised. This process verifies the authenticity of the website or server. If the validation fails, the browser typically displays a warning to the user, alerting them to potential security risks.
Comparison of TLS/SSL Versions
Different TLS/SSL versions offer varying levels of security and functionality. Upgrades to these protocols address vulnerabilities and enhance security.
| Version | Features | Security |
|---|---|---|
| TLS 1.0 | Introduced initial encryption methods. | Vulnerable to several known exploits and considered outdated. |
| TLS 1.2 | Improved cipher suites, strengthened authentication mechanisms, and enhanced security. | More secure than TLS 1.0, but still susceptible to certain vulnerabilities if not implemented correctly. |
TLS 1.2 offers enhanced security compared to TLS 1.0. This upgrade addressed some critical vulnerabilities, making it a more secure protocol. However, newer versions like TLS 1.3 further enhance security and performance. It’s crucial to understand the security implications of each version and ensure compatibility with the latest versions. The use of older, less secure versions should be avoided.
Final Conclusion
In conclusion, understanding insecure connections and the role of browsers like Chrome and Firefox is paramount in today’s digital landscape. Choosing HTTPS is crucial for protecting sensitive data. This guide has provided a comprehensive overview of the security implications and practical steps for mitigating risks. By prioritizing secure connections, users and website administrators can contribute to a safer online environment.