Active Directory NTLM attack security advisory: This advisory details the critical threats posed by attacks targeting the vulnerabilities in NTLM authentication within Active Directory environments. Understanding these attacks, their potential impact, and effective mitigation strategies is crucial for maintaining network security. We’ll explore the intricacies of NTLM, the common attack vectors, and the best practices for safeguarding your Active Directory against exploitation.
This advisory covers a range of topics, from the fundamental concepts of Active Directory and NTLM authentication to the various attack scenarios, mitigation strategies, and practical case studies. We’ll analyze the effectiveness of different security measures, discuss the importance of strong passwords and multi-factor authentication, and highlight the role of timely patching and network segmentation. Detailed tables will compare different attack types, security measures, and tools, providing clear and concise information.
Introduction to Active Directory NTLM Attack Security Advisory

Active Directory (AD) is the backbone of many corporate networks, managing user accounts, computers, and resources. It acts as a central repository for authentication and authorization, crucial for maintaining security and access control. However, its reliance on certain authentication protocols can leave it vulnerable to attack. This advisory focuses on NTLM vulnerabilities and their impact on AD environments.NTLM, or the New Technology LAN Manager, is an authentication protocol used by Windows systems.
Staying vigilant about Active Directory NTLM attack security advisories is crucial. Recent security breaches highlight the need for robust defenses. Thankfully, companies like JetBlue are proactively improving customer service, as seen in their recent overhaul, detailed in a recent article about jetblue gladly customer service overhaul text twitter. This customer-centric approach, however, doesn’t negate the importance of robust security measures against attacks like NTLM.
Ultimately, a layered approach to security is key.
While once common, NTLM is now considered insecure due to its susceptibility to various exploits. Its weakness stems from the transmission of passwords in cleartext or using easily crackable hashing methods, leaving the door open to attackers.The potential impact of an NTLM attack on an Active Directory environment is significant. Compromised credentials can grant attackers unauthorized access to sensitive data, network resources, and potentially the entire network.
This can lead to data breaches, financial losses, reputational damage, and operational disruption. Attackers could also gain elevated privileges, enabling them to install malware, delete data, or even control critical systems.Common methods for exploiting NTLM vulnerabilities include Pass-the-Hash, Pass-the-Ticket, Golden Ticket, and Kerberoasting attacks. These techniques leverage the weaknesses in NTLM authentication to gain unauthorized access. These methods vary in their sophistication and complexity, but all exploit the same core vulnerabilities in the system.
NTLM Attack Types and Their Characteristics
NTLM vulnerabilities allow attackers to exploit authentication protocols, potentially compromising critical systems and data. Understanding the various attack types is essential for mitigating these risks.
| Attack Type | Description | Impact | Mitigation |
|---|---|---|---|
| Pass-the-Hash | Attackers capture a user’s hash and use it to authenticate to the system as that user. | Unauthorized access to user accounts and resources. | Implement strong password policies, use modern authentication protocols (like Kerberos), and regularly audit Active Directory. |
| Pass-the-Ticket | Attackers use stolen Kerberos tickets to gain access to resources. | Elevated privileges and unauthorized access to network resources. | Restrict access to sensitive resources, implement strong password policies, and regularly monitor Active Directory for suspicious activity. |
| Golden Ticket | Attackers create a forged Kerberos ticket granting them unrestricted access to Active Directory. | Full control over Active Directory, allowing attackers to compromise critical systems and data. | Regularly update Active Directory and security tools, implement strong password policies, and monitor Active Directory for suspicious activity. |
| Kerberoasting | Attackers exploit the Kerberos protocol to crack service accounts’ passwords. | Elevated privileges and potential access to sensitive data. | Restrict service account access to necessary resources, use strong passwords for service accounts, and implement least privilege principles. |
Understanding the Threat Landscape: Active Directory Ntlm Attack Security Advisory
NTLM (NT LAN Manager) attacks exploit a legacy authentication protocol, leaving organizations vulnerable to various forms of unauthorized access. Understanding the vectors, stages, and attack scenarios is crucial for implementing effective security measures. This section delves into the threat landscape of NTLM attacks, highlighting common vulnerabilities and potential attack strategies.
Common Vectors for an NTLM Attack
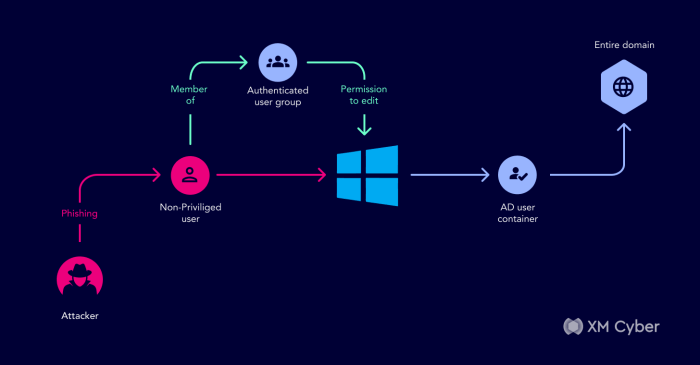
NTLM attacks often leverage weaknesses in user accounts and network configurations. Compromised accounts, often through phishing or brute-force attacks, provide attackers with initial access points. Weak passwords, easily guessed or cracked, also facilitate unauthorized entry. Furthermore, insecure network configurations, such as poorly configured firewalls or lack of network segmentation, can increase the attack surface.
Typical Stages in an NTLM Attack
NTLM attacks typically follow a sequence of steps. Initial compromise often involves exploiting a weak or compromised account. The attacker then leverages this access to gain further privileges. This may involve escalating privileges through known vulnerabilities or exploiting weaknesses in the Active Directory environment. The attacker might then move laterally across the network, seeking valuable data or sensitive systems.
Finally, the attacker may exfiltrate the data or execute malicious commands.
How Attackers Leverage Compromised Accounts
Once an attacker gains initial access through a compromised account, they can exploit this foothold to achieve broader network access. Techniques like credential stuffing or password spraying can be employed to gain further access. The attacker can also attempt to exploit vulnerabilities within the compromised account’s permissions to escalate privileges. This escalation allows the attacker to access resources they wouldn’t normally have access to.
Sophisticated attackers often use automated tools and scripts to automate these processes.
Attack Scenarios for NTLM Attacks
NTLM attacks can manifest in various forms. Targeted attacks focus on specific organizations or individuals, leveraging detailed reconnaissance to exploit known vulnerabilities. Opportunistic attacks, on the other hand, aim to exploit vulnerabilities in any organization that might be susceptible. Attackers may also use automated tools to scan networks for vulnerable systems and accounts.
Comparison of Security Measures Effectiveness
| Security Measure | Description | Effectiveness | Cost |
|---|---|---|---|
| Strong Password Policies | Enforce complex password requirements and regular password changes. | High (reduces brute-force attacks and credential stuffing). | Low (minimal investment for policy implementation). |
| Multi-Factor Authentication (MFA) | Requires multiple forms of authentication beyond passwords. | Very High (significantly reduces unauthorized access). | Medium (investment in MFA solutions). |
| Network Segmentation | Isolate sensitive resources and systems within the network. | High (limits lateral movement). | Medium to High (depends on the scope of segmentation). |
| Regular Security Audits and Vulnerability Assessments | Proactively identify and address security weaknesses. | Medium to High (detects and mitigates vulnerabilities). | Medium (requires skilled personnel and resources). |
| NTLM Authentication Disablement | Remove reliance on NTLM authentication entirely. | Very High (eliminates the vulnerability). | High (requires significant effort and potentially system reconfiguration). |
Mitigation Strategies and Best Practices
Protecting your Active Directory from NTLM attacks requires a multi-layered approach. Simply patching vulnerabilities isn’t enough. A comprehensive strategy encompassing strong passwords, robust authentication, timely updates, and network isolation is crucial. This approach minimizes the attack surface and strengthens your defenses against sophisticated attackers.
Strong Password Policies
Effective password policies are paramount in thwarting NTLM attacks. Weak passwords are the easiest entry point for attackers. Implementing strong password policies forces users to create complex passwords that are difficult to guess or crack. This significantly reduces the likelihood of successful brute-force attacks.
- Enforce a minimum password length requirement. Passwords should be at least 12 characters long to make them more difficult to crack.
- Demand a combination of uppercase and lowercase letters, numbers, and special characters. This increases password complexity, making them much harder to guess.
- Implement password expiration policies. Regular password changes reduce the time an attacker could exploit a compromised password.
- Discourage the use of easily guessable passwords, like birthdays, names, or common phrases.
Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) adds an extra layer of security beyond a simple password. By requiring multiple forms of verification (e.g., a code sent to a phone, a biometric scan), MFA makes it significantly harder for attackers to gain access even if they compromise a password.
- Implement MFA for all user accounts, particularly for administrative accounts.
- Consider using hardware tokens or authenticator apps for increased security.
- Ensure MFA is enforced consistently across all systems and applications that interact with the Active Directory.
Timely Patching and Updates
Regular patching and updates are essential for mitigating vulnerabilities. Attackers frequently exploit known weaknesses in software. By promptly applying security updates, organizations can significantly reduce the risk of successful attacks.
- Establish a robust patch management system to ensure all systems are updated promptly.
- Implement automated patching processes to reduce manual intervention and human error.
- Prioritize critical security updates and patches to address known vulnerabilities.
Network Segmentation and Access Controls
Network segmentation limits the impact of a successful attack. By isolating sensitive resources, an attacker’s ability to move laterally within the network is reduced. Access controls restrict access to resources based on user roles and responsibilities.
- Segment the network into smaller, isolated zones to limit the spread of potential breaches.
- Implement granular access controls to limit user access to only necessary resources.
- Regularly review and update access controls to ensure they align with current security needs.
Password Complexity Requirements
The effectiveness of password complexity requirements depends on the specific requirements. Different levels of complexity offer varying degrees of protection.
| Requirement | Description | Strength | Implementation |
|---|---|---|---|
| Basic | Minimum length (8 characters), no special characters. | Low | Easy to implement, but very vulnerable to attacks. |
| Moderate | Minimum length (12 characters), combination of uppercase and lowercase letters, numbers. | Medium | Moderately strong, but still susceptible to dictionary attacks. |
| Strong | Minimum length (16 characters), combination of uppercase and lowercase letters, numbers, special characters. | High | More difficult to crack, requiring more computational resources. |
| Extra Strong | Minimum length (20 characters), complex combination of uppercase and lowercase letters, numbers, special characters, symbols. | Very High | Highly resistant to brute-force and dictionary attacks. |
Security Advisory Recommendations
NTLM authentication, while historically common, presents significant vulnerabilities. Exploiting these weaknesses can lead to unauthorized access, data breaches, and system compromise. Proactive measures are crucial to mitigate the risks associated with NTLM attacks. This section provides actionable recommendations for preventing, detecting, and responding to such threats.
Preventative Measures Against NTLM Attacks
Implementing strong preventative measures is paramount to securing Active Directory environments. These steps focus on reducing attack surfaces and enhancing overall security posture.
- Disable NTLM authentication where possible. Migrate to more secure authentication protocols like Kerberos. This eliminates a primary attack vector for malicious actors.
- Enforce strong passwords and multi-factor authentication (MFA). Robust password policies and MFA significantly reduce the impact of compromised credentials. Regular password audits and enforced password complexity are also essential.
- Regularly update software and operating systems. Patches often address vulnerabilities that could be exploited in NTLM attacks. Automated patching systems are highly recommended for efficiency.
- Segment the network. Isolating critical systems and resources reduces the impact of a successful attack. Proper network segmentation limits the reach of malicious activity.
- Implement network access controls (NAC). NAC solutions control network access based on various factors like device health and security posture. This restricts unauthorized access.
Recommendations for Detecting and Responding to NTLM Attacks
Early detection and swift response are critical in minimizing the damage from an NTLM attack. A proactive approach is essential for minimizing downtime and preventing escalation.
- Utilize intrusion detection and prevention systems (IDS/IPS). IDS/IPS solutions can monitor network traffic for suspicious activity, alerting administrators to potential attacks.
- Implement security information and event management (SIEM) systems. SIEM systems correlate security events from various sources, providing a comprehensive view of the security posture and detecting potential threats.
- Monitor Active Directory logs. Regularly review logs for unusual login attempts, account creation, or modification activities. Abnormal activities often indicate malicious intent.
- Implement security monitoring tools to track user behavior and access patterns. Unusual access patterns or privilege escalation attempts might signify malicious activity.
- Establish a clear incident response plan. Having a well-defined plan for handling security incidents is crucial for swift and effective response. This plan should Artikel roles, responsibilities, and procedures for different scenarios.
Detailed Incident Response Plan for an NTLM Attack, Active directory ntlm attack security advisory
A well-structured incident response plan is crucial for minimizing the impact of an NTLM attack. It should Artikel procedures for various stages, from detection to containment.
- Detection and Analysis: Identify the attack vector, scope of the compromise, and affected systems. Detailed logging and monitoring systems are key.
- Containment: Isolate affected systems and accounts to prevent further compromise. Network segmentation is critical for limiting the spread.
- Eradication: Remove malware and restore compromised systems to a known good state. Careful restoration procedures are critical to avoid further issues.
- Recovery: Restore services and data, and review security controls for weaknesses. Comprehensive auditing is essential to identify and correct any vulnerabilities.
- Post-Incident Activity: Review the incident response process, identify lessons learned, and update security controls to prevent future attacks. Comprehensive reporting and analysis are critical.
Tools and Technologies for Detecting and Mitigating NTLM Attacks
Various tools and technologies are available to detect and mitigate NTLM attacks. Choosing the right tools depends on the specific needs and resources of the organization.
- Security Information and Event Management (SIEM) tools: These tools collect and analyze security logs from various sources, detecting anomalies and suspicious activities.
- Intrusion Detection and Prevention Systems (IDS/IPS): These systems monitor network traffic for malicious patterns, alerting administrators to potential threats.
- Active Directory Auditing Tools: These tools help to track and analyze changes in Active Directory, detecting unauthorized access or modifications.
- Network Monitoring Tools: These tools provide visibility into network traffic, helping to identify unusual patterns or suspicious connections.
Active Directory Security Audit Tools Summary
| Tool Name | Description | Features | Pricing |
|---|---|---|---|
| Security Onion | Open-source security information and event management (SIEM) platform. | Log aggregation, analysis, and correlation; intrusion detection; network traffic analysis. | Free |
| Splunk | Enterprise-grade SIEM platform. | Advanced log analysis, threat hunting, incident response; customizable dashboards. | Subscription-based |
| Wireshark | Open-source network protocol analyzer. | Deep packet inspection; protocol analysis; network traffic visualization. | Free |
| Microsoft Security Compliance Manager | Microsoft’s tool for assessing and managing security compliance. | Active Directory compliance assessment; vulnerability scanning; policy management. | Included with Microsoft licensing |
Case Studies and Examples
NTLM authentication, while once a standard, is now a significant security vulnerability. Real-world attacks leveraging this protocol have demonstrated its weaknesses and the devastating impact on organizations that fail to mitigate the risks. Understanding these examples is crucial for implementing robust security measures.Understanding the vulnerabilities of NTLM is essential to prevent exploitation. Analyzing real-world attacks highlights the critical need for proactive security measures to safeguard against these threats.
Real-World NTLM Attack Examples
The lack of encryption in NTLM authentication makes it susceptible to various attacks. Attackers can intercept authentication packets, decrypt them, and potentially gain access to sensitive information or systems. These attacks often involve credential theft, lateral movement within a network, and even full system compromise.
Staying on top of security advisories like the Active Directory NTLM attack is crucial. Thankfully, while dealing with these threats, I’ve been enjoying the new content in Diablo Immortals’ first major update, “Forgotten Nightmares,” which adds a ton of new quests and rewards. This update is a welcome distraction from the ongoing need to patch vulnerabilities like the NTLM attack in Active Directory environments.
Fortunately, there are some great resources to help in mitigating those risks.
Impact of NTLM Attacks on Organizations
The impact of NTLM attacks can be severe, affecting an organization’s reputation, financial stability, and operational efficiency. Data breaches can lead to financial losses, regulatory penalties, and a loss of customer trust. Disruptions to business operations can result in significant downtime and lost productivity.
Staying on top of security advisories like the Active Directory NTLM attack is crucial. These vulnerabilities can impact your systems, but the implications extend beyond the digital realm. For instance, the recent visa rejection of the PUBG Nations Cup team Vietnam esports team for participating in illegal tournaments highlights how seemingly disparate events can connect. Understanding these connections is key to a holistic security approach.
Ultimately, vigilance against Active Directory NTLM attack vulnerabilities is essential for robust cybersecurity practices. pubg nations cup team vietnam esports illegal tournaments visa rejection
Preventing Security Breaches through Proactive Measures
Proactive measures are crucial in preventing NTLM-based attacks. These measures include implementing strong authentication protocols, like modern authentication methods, along with regular security assessments and vulnerability scanning to identify and address potential weaknesses in the system. Regular security audits and penetration testing can help identify vulnerabilities in the system and network.
Analysis of Security Advisory and Preventative Measures
A well-structured security advisory should provide clear recommendations for mitigating the risks of NTLM attacks. The advisory should Artikel specific actions to update authentication protocols, implement strong password policies, and utilize robust security controls. It should also highlight the importance of network segmentation and restricting access privileges.
Example of Successful NTLM Attack Mitigation
A company discovered a vulnerability in its Active Directory infrastructure that exposed it to NTLM attacks. They immediately updated their Active Directory to implement Kerberos authentication, a more secure protocol. They also conducted a network segmentation to isolate potentially compromised systems. Furthermore, they enforced strong password policies and conducted regular security audits. This proactive approach successfully mitigated the risk of future NTLM attacks. By addressing the vulnerabilities and implementing strong security controls, the company was able to prevent unauthorized access to sensitive data and maintain business continuity.
Technical Deep Dive
NTLM authentication, a cornerstone of Active Directory, presents a fascinating yet complex target for attackers. Understanding its intricacies, vulnerabilities, and exploitation techniques is crucial for securing your environment. This section delves into the technical aspects of NTLM, illustrating how attackers leverage its weaknesses to gain unauthorized access.NTLM, or the “NT Lan Manager,” is an authentication protocol used to verify user credentials on Windows networks.
It relies on a challenge-response mechanism, exchanging messages between client and server. This seemingly straightforward process harbors vulnerabilities that can be exploited by attackers. The following sections Artikel how these vulnerabilities are exploited, demonstrating the attacker’s perspective and providing mitigation strategies.
NTLM Authentication Mechanics
NTLM authentication involves a series of steps, beginning with the client requesting authentication. The server responds with a challenge, and the client generates a response based on its credentials. This response is then sent back to the server for verification. The security of this process relies on the integrity and confidentiality of the exchanged messages. Weaknesses in the protocol can be exploited to bypass these checks.
NTLM Protocol Vulnerabilities
NTLM’s inherent design flaws are a major source of attack vectors. One key vulnerability is the lack of encryption in the initial stages of authentication. This exposes the authentication process to man-in-the-middle attacks. Another critical weakness is the use of a weak hashing algorithm, allowing attackers to crack passwords through brute-force or dictionary attacks. The lack of strong cryptographic measures in the authentication protocol makes it susceptible to various exploits, enabling attackers to gain unauthorized access.
Attacker’s Perspective: Performing an NTLM Attack
From an attacker’s perspective, the goal is to bypass authentication mechanisms and gain access to the target network. This often involves exploiting the weaknesses in NTLM. Attackers can use tools to capture NTLM authentication traffic, retrieve hashed credentials, and subsequently use them to authenticate as legitimate users. Sophisticated attackers might utilize techniques like credential stuffing or dictionary attacks to further expand their access.
Kerberoasting
Kerberoasting is a specific attack leveraging the vulnerabilities in the Kerberos authentication protocol, often combined with NTLM. It focuses on exploiting service accounts with weak or predictable passwords to obtain their hash. These hashes can then be used to crack domain user accounts or perform further attacks. The attacker’s primary objective is to leverage Kerberos vulnerabilities to obtain service account credentials, potentially escalating their access within the network.
Golden Ticket Attack
The Golden Ticket attack, a sophisticated method of gaining elevated privileges, leverages the Kerberos authentication protocol. It involves creating a forged service ticket granting access to any resource within the domain. Attackers can use this ticket to impersonate privileged accounts, giving them complete control over the system.
Securing Active Directory Against Golden Ticket Attacks
Securing Active Directory against Golden Ticket attacks requires a multi-layered approach. Careful configuration and vigilant monitoring are essential.
| Step | Description | Tools | Expected Outcome |
|---|---|---|---|
| 1 | Implement strong password policies and regular password changes for all service accounts. | Active Directory administrative tools | Reduces the likelihood of service accounts being compromised. |
| 2 | Restrict access to sensitive resources using least privilege principles. | Active Directory administrative tools, RBAC (Role-Based Access Control) | Limits the potential damage if a compromised account is used. |
| 3 | Enable and maintain proper audit logging for all critical activities. | Active Directory audit logs, security information and event management (SIEM) tools | Provides a record of events that can be used for incident response. |
| 4 | Implement and regularly test security awareness training for all users. | Security awareness training platforms, phishing simulations | Reduces the risk of users falling victim to social engineering attacks. |
Final Wrap-Up
In conclusion, understanding and proactively addressing NTLM attacks is essential for maintaining the integrity and security of your Active Directory environment. This advisory provides a comprehensive overview of the threat landscape, mitigation strategies, and best practices. By implementing the recommendations Artikeld in this document, organizations can significantly reduce their vulnerability to NTLM attacks and enhance their overall security posture.
Remember, a robust security strategy involves constant vigilance, continuous learning, and a proactive approach to threat detection and response.